Professional Documents
Culture Documents
HB 324-2008 Lexicon of Key Terms Used in Security
Uploaded by
SAI Global - APACCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
HB 324-2008 Lexicon of Key Terms Used in Security
Uploaded by
SAI Global - APACCopyright:
Available Formats
This is a free 8 page sample. Access the full version at http://infostore.saiglobal.com.
HB 3242008
Lexicon of Key Terms used in Security
HB
This is a free 8 page sample. Access the full version at http://infostore.saiglobal.com.
HB 3242008
Lexicon of Key Terms used in Security
First published as HB 3242008.
Copyright 2008 Standards Australia Limited.
All rights reserved. No part of this publication may be reproduced or copied in any form or by any means,
electronic or mechanical, including photocopying, without the written permission of the publisher.
Published by Standards Australia Limited, GPO Box 476, Sydney, NSW 2001, Australia
ISBN 0 7337 8844 0
HB 3242008
Foreword
FOREWORD
Note from the Author
I would like to sincerely thank the owners and operators of critical
infrastructure represented in Trusted Information Sharing Network (TISN) and
other key interested parties for their participation in the consultation stages of
this project. A full list of contributors is provided at the end of this report.
A lexicon of key security terms can only be relevant if it is informed by the
knowledge and experience of experts in the field. I believe that this has been
achieved through the commitment and dedication of all concerned.
This is a free 8 page sample. Access the full version at http://infostore.saiglobal.com.
I hope that the Lexicon will prove to be a useful tool that will improve
communication across the diverse security sector.
Mark Bezzina, Managing Director
StanCert Pty Ltd
Contents
HB 3242008
CONTENTS
Page
1
2
This is a free 8 page sample. Access the full version at http://infostore.saiglobal.com.
4
5
Introduction ........................................................................................................................ 4
The Security Lexicon Project .............................................................................................. 6
2.1 Purpose........................................................................................................................ 7
2.2 Scope and objectives ................................................................................................... 7
2.3 Project methodology .................................................................................................... 7
Criteria................................................................................................................................ 9
3.1 Creating a definition .................................................................................................... 10
3.2 Audience .................................................................................................................... 10
3.3 Authority levels ........................................................................................................... 11
3.4 Key criteria for good definitions................................................................................... 11
Interrelationships and linkages between terms ................................................................. 13
Overview of stakeholder input........................................................................................... 17
5.1 Pre-consultation submissions ..................................................................................... 18
5.2 Interrelationships of terms........................................................................................... 18
5.3 Selection from existing terms...................................................................................... 19
5.4 Preferred definitions.................................................................................................... 19
Definitions......................................................................................................................... 21
6.1 Security ...................................................................................................................... 22
6.2 Security Risk Management ......................................................................................... 25
6.3 Emergency Management............................................................................................ 28
6.4 Business Continuity Management............................................................................... 32
6.5 Enterprise-Wide Risk Management............................................................................. 35
6.6 Business Resilience .................................................................................................... 37
6.7 Infrastructure Assurance............................................................................................. 40
6.8 National Security......................................................................................................... 42
6.9 Protective Security...................................................................................................... 45
6.10 Critical Infrastructure................................................................................................... 46
Summary of Proposed Definitions .................................................................................... 50
7.1 Overarching Descriptor ............................................................................................... 51
7.2 Proposed Definitions................................................................................................... 51
ANNEXES
A
B
C
D
About Standards Australia................................................................................................ 54
About the National Centre for Security Standards (NCSS) ................................................ 56
Developing the Lexicon .................................................................................................... 59
Contributors ..................................................................................................................... 61
D1 Pre-consultation ......................................................................................................... 62
D2 Consultation ............................................................................................................... 64
E Consolidated comments for Draft Lexicon of Key Terms used in Security ........................ 66
This is a free 8 page sample. Access the full version at http://infostore.saiglobal.com.
HB 3242008
1
Introduction
Introduction
HB 3242008
The Security Lexicon Project was established to develop an authoritative
lexicon of key security terms to be published as a Standards Australia
Handbook. The need for this Lexicon arose out of the Security Standards and
Support Systems project and the Critical Infrastructure Protection Training
Analysis project, in which it was identified that there is a lack of common
understanding of terminology used in the security industry. Good terminology
aids efficiency, security, quality and safety. Using the same terms for the
same concepts helps to avoid misunderstandings that lead to conflict,
wasted time and money.
This is a free 8 page sample. Access the full version at http://infostore.saiglobal.com.
In order to achieve this, extensive consultation took place with the owners
and operators of critical infrastructure represented in the Trusted Information
Sharing Network for Critical Infrastructure Protection (TISN) and other key
interested parties.
This is a free 8 page sample. Access the full version at http://infostore.saiglobal.com.
HB 3242008
2
The Security Lexicon
Project
The Security Lexicon Project
2.1
HB 3242008
Purpose
The Project was initiated by Standards Australia to provide stakeholders with
the definitions of key terms used in security.
2.2
Scope and objectives
This is a free 8 page sample. Access the full version at http://infostore.saiglobal.com.
The Security Lexicon Handbook aims to develop an authoritative lexicon of
key security terms that will assist the owners and operators of critical
infrastructure to develop a common understanding of terminology used in the
security industry and to use standard terminology to communicate security
related matters.
The Lexicon focused on the following ten key terms and their
interrelationships. It is beyond the scope of this document to create a general
dictionary of all the terms used in security. The terms below have been
chosen because they have been identified as creating the most confusion.
(a)
Security
(b)
Security Risk Management
(c)
Emergency Management
(d)
Business Continuity Management
(e)
Enterprise-Wide Risk Management
(f)
Business Resilience
(g)
Infrastructure Assurance
(h)
National Security
(i)
Protective Security
(j)
Critical Infrastructure
The Lexicon of key security terms takes an all hazards approach to critical
infrastructure protection from a business perspective and covers all aspects
of the security industry and security management.
2.3
Project methodology
A project plan that defines the detailed methodology, timelines and
deliverables was approved by the National Centre for Security Standards
(NCSS).
Pre-consultation and analysis and research involved carrying out background
research to identify effective systems for the creation of security definitions. It
also identified existing definitions for the 10 key security terms.
To ensure that the project identified and examined all existing authoritative
definitions, stakeholders were sent a letter requesting their suggested
definitions for the key terms.
Stakeholders were also asked to identify the source of their preferred
definition, along with its strengths and weaknesses.
This is a free preview. Purchase the entire publication at the link below:
This is a free 8 page sample. Access the full version at http://infostore.saiglobal.com.
HB 324-2008, Lexicon of Key Terms used in
Security
Looking for additional Standards? Visit SAI Global Infostore
Subscribe to our Free Newsletters about Australian Standards in Legislation; ISO, IEC, BSI and more
Do you need to Manage Standards Collections Online?
Learn about LexConnect, All Jurisdictions, Standards referenced in Australian legislation
Do you want to know when a Standard has changed?
Want to become an SAI Global Standards Sales Affiliate?
Learn about other SAI Global Services:
LOGICOM Military Parts and Supplier Database
Metals Infobase Database of Metal Grades, Standards and Manufacturers
Materials Infobase Database of Materials, Standards and Suppliers
Database of European Law, CELEX and Court Decisions
Need to speak with a Customer Service Representative - Contact Us
You might also like
- MP 96-2008 Standards For Enterprise-Wide Patient Administration SystemsDocument7 pagesMP 96-2008 Standards For Enterprise-Wide Patient Administration SystemsSAI Global - APAC0% (1)
- MP 99-2009 Telehealth Session Information Required For Health RecordsDocument7 pagesMP 99-2009 Telehealth Session Information Required For Health RecordsSAI Global - APAC0% (1)
- MP 94-2003 Product Numbering Standards For Electronic Health Supply ChainsDocument9 pagesMP 94-2003 Product Numbering Standards For Electronic Health Supply ChainsSAI Global - APAC0% (1)
- SAI Global Expands Standards On-LineDocument2 pagesSAI Global Expands Standards On-LineSAI Global - APAC0% (1)
- MP 88-2000 Evolution of Australian Standard For Pressure Vessel Steel PlateDocument6 pagesMP 88-2000 Evolution of Australian Standard For Pressure Vessel Steel PlateSAI Global - APAC0% (1)
- MP 76-1997 Pressure Equipment - Inspection Bodies and PersonnelDocument8 pagesMP 76-1997 Pressure Equipment - Inspection Bodies and PersonnelSAI Global - APACNo ratings yet
- MP 87.1-2008 Australian New Zealand Certification Scheme For Explosion-Protected Electrical Equipment (ANZExDocument6 pagesMP 87.1-2008 Australian New Zealand Certification Scheme For Explosion-Protected Electrical Equipment (ANZExSAI Global - APACNo ratings yet
- MP 87.2-2007 Australian New Zealand Certification Scheme For Explosion-Protected Electrical Equipment (ANZExDocument7 pagesMP 87.2-2007 Australian New Zealand Certification Scheme For Explosion-Protected Electrical Equipment (ANZExSAI Global - APAC0% (1)
- MP 75-1996 Strategies For The Implementation of A Public Key Authentication Framework (PKAF) in AustraliaDocument15 pagesMP 75-1996 Strategies For The Implementation of A Public Key Authentication Framework (PKAF) in AustraliaSAI Global - APACNo ratings yet
- MP 91-2000 Dynamic Approaches To Healthcare Risk ManagementDocument8 pagesMP 91-2000 Dynamic Approaches To Healthcare Risk ManagementSAI Global - APAC0% (1)
- MP 78-1999 Manual For The Assessment of Risks of Plumbing ProductsDocument5 pagesMP 78-1999 Manual For The Assessment of Risks of Plumbing ProductsSAI Global - APACNo ratings yet
- MP 84-2000 Evolution of Australian Standards For Structural SteelDocument4 pagesMP 84-2000 Evolution of Australian Standards For Structural SteelSAI Global - APACNo ratings yet
- MP 74-1996 Strategies For The Development of Standards For Digital Video and Associated ServicesDocument10 pagesMP 74-1996 Strategies For The Development of Standards For Digital Video and Associated ServicesSAI Global - APACNo ratings yet
- MP 62-1992 OSI - VocabularyDocument5 pagesMP 62-1992 OSI - VocabularySAI Global - APACNo ratings yet
- MP 63-1992 The Australian GarmentMark - Specifications and ProceduresDocument5 pagesMP 63-1992 The Australian GarmentMark - Specifications and ProceduresSAI Global - APAC0% (1)
- MP 67.1-1992 Standardized Interoperability Tests in The OSI Environment X.400 TestsDocument10 pagesMP 67.1-1992 Standardized Interoperability Tests in The OSI Environment X.400 TestsSAI Global - APACNo ratings yet
- MP 25-2002 Basic Guide To MicrofilmingDocument7 pagesMP 25-2002 Basic Guide To MicrofilmingSAI Global - APACNo ratings yet
- MP 67.2-1992 Standardized Interoperability Tests in The OSI Environment FTAM TestsDocument7 pagesMP 67.2-1992 Standardized Interoperability Tests in The OSI Environment FTAM TestsSAI Global - APACNo ratings yet
- MP 55-1988 Vehicle Identification Number (VIN) CodesDocument6 pagesMP 55-1988 Vehicle Identification Number (VIN) CodesSAI Global - APACNo ratings yet
- MP 59-2000 Naming and Addressing in The Australian OSI EnvironmentDocument6 pagesMP 59-2000 Naming and Addressing in The Australian OSI EnvironmentSAI Global - APACNo ratings yet
- As 1562.1-1992 Design and Installation of Sheet Roof and Wall Cladding MetalDocument5 pagesAs 1562.1-1992 Design and Installation of Sheet Roof and Wall Cladding MetalSAI Global - APAC17% (6)
- MP 48-2008 Certified Gas Cylinder Test StationsDocument6 pagesMP 48-2008 Certified Gas Cylinder Test StationsSAI Global - APACNo ratings yet
- MP 2-1938 Report On The Standardization of Minimum Requirements For Sewerage By-LawsDocument8 pagesMP 2-1938 Report On The Standardization of Minimum Requirements For Sewerage By-LawsSAI Global - APACNo ratings yet
- MP 58-1991 Workplace Injury and Disease Recording Standard - Resource KitDocument6 pagesMP 58-1991 Workplace Injury and Disease Recording Standard - Resource KitSAI Global - APAC100% (1)
- MP 53-2004 Personal Financial Planning Part 1 - Definitions Processes and Practices Part 2 - Requirements ForDocument10 pagesMP 53-2004 Personal Financial Planning Part 1 - Definitions Processes and Practices Part 2 - Requirements ForSAI Global - APACNo ratings yet
- MP 51-1986 A Study of Language in Australian Business DocumentsDocument4 pagesMP 51-1986 A Study of Language in Australian Business DocumentsSAI Global - APACNo ratings yet
- MP 52-2005 Manual of Authorization Procedures For Plumbing and Drainage ProductsDocument8 pagesMP 52-2005 Manual of Authorization Procedures For Plumbing and Drainage ProductsSAI Global - APACNo ratings yet
- MP 15.6-1990 Standards Australia Style Manual Drafting and Interpretation of Standards From A Legal PerspectiDocument7 pagesMP 15.6-1990 Standards Australia Style Manual Drafting and Interpretation of Standards From A Legal PerspectiSAI Global - APACNo ratings yet
- MP 100-2009 Procedures For Certification of Organic and Biodynamic ProductsDocument8 pagesMP 100-2009 Procedures For Certification of Organic and Biodynamic ProductsSAI Global - APACNo ratings yet
- MP 15.2-1990 Standards Australia Style Manual Drafting of Australian StandardsDocument8 pagesMP 15.2-1990 Standards Australia Style Manual Drafting of Australian StandardsSAI Global - APACNo ratings yet
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (890)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Akshith+Dutt CVDocument3 pagesAkshith+Dutt CVkal kastNo ratings yet
- Power Supplies SPS1000 Series Operating ManualDocument7 pagesPower Supplies SPS1000 Series Operating ManualKrystyna ZaczekNo ratings yet
- Enforcing Microsoft Active Directory Policies Using LDAP Attribute MapsDocument34 pagesEnforcing Microsoft Active Directory Policies Using LDAP Attribute MapsKaddour El HallaouiNo ratings yet
- Banking SystemDocument68 pagesBanking SystemvermalabNo ratings yet
- LIS Interface Manual of BK Series Biochemistry Analyzer-1Document30 pagesLIS Interface Manual of BK Series Biochemistry Analyzer-1Abdulrahman Biomedical engineerNo ratings yet
- Sandboxing Approach1Document27 pagesSandboxing Approach1Muqheed Shaik67% (3)
- 54 Channel EEG Digital SystemDocument2 pages54 Channel EEG Digital SystemDavit SoesantoNo ratings yet
- Antivirus SoftwareDocument1 pageAntivirus SoftwareMary Ann SalvatierraNo ratings yet
- Visual C++ NET TutorialsDocument39 pagesVisual C++ NET Tutorialspgoyal10No ratings yet
- Cyber Security Challenges - Praveen NayakDocument11 pagesCyber Security Challenges - Praveen NayakPraveen NayakNo ratings yet
- Jiwaji University Gwalior: Self Learning Material FORDocument359 pagesJiwaji University Gwalior: Self Learning Material FORVikas SharmaNo ratings yet
- All About Data Transfer Process (DTP) - SAP BW 7 - SCNDocument6 pagesAll About Data Transfer Process (DTP) - SAP BW 7 - SCNloknathtanikantiNo ratings yet
- Uml 3 PGDocument114 pagesUml 3 PGGurwinder SinghNo ratings yet
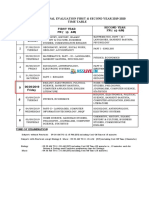
- Hsslive HSS First Term Exam Time Table Revised PDFDocument1 pageHsslive HSS First Term Exam Time Table Revised PDFCricket Creator100% (1)
- Request For ProposalDocument216 pagesRequest For ProposalGilbert KamanziNo ratings yet
- WPSDocument468 pagesWPS0260480981No ratings yet
- Philips Pm3295 Service ManualDocument322 pagesPhilips Pm3295 Service Manualglu7833No ratings yet
- Data Mining MCQ FINALDocument32 pagesData Mining MCQ FINALAmit Kumar SahuNo ratings yet
- Historical Antecedents in The Course of Science and TechnologyDocument2 pagesHistorical Antecedents in The Course of Science and TechnologyElboy Son DecanoNo ratings yet
- VG278 Series LCD Monitor User GuideDocument24 pagesVG278 Series LCD Monitor User GuideEdsel LoquillanoNo ratings yet
- Shailendra Prasad: ABAP OO KnowledgeDocument6 pagesShailendra Prasad: ABAP OO Knowledgeprasadshail41No ratings yet
- Signal To Interference Ratio & Signal To Noise Ratio: Lovely Professional University TopicDocument7 pagesSignal To Interference Ratio & Signal To Noise Ratio: Lovely Professional University TopicRavi RajNo ratings yet
- M817 13 4-GO-LW A4 E ScreenDocument19 pagesM817 13 4-GO-LW A4 E ScreenRikyNo ratings yet
- Kubernetes Troubleshooting DocsDocument15 pagesKubernetes Troubleshooting Docschandrashekar_ganesanNo ratings yet
- Process Performance Report Analyzes Netto CapabilityDocument1 pageProcess Performance Report Analyzes Netto CapabilityDita DesnasariNo ratings yet
- Top 5 sorting algorithms explained: Insertion, Selection, Bubble, Merge and Quick SortDocument2 pagesTop 5 sorting algorithms explained: Insertion, Selection, Bubble, Merge and Quick SortCristine Joy JemillaNo ratings yet
- Thesis Progress TrackerDocument4 pagesThesis Progress Trackerheatherbeninatianchorage100% (2)
- Feature Boxes CV TemplateDocument3 pagesFeature Boxes CV TemplatezaidkhanNo ratings yet
- IFE ZazoAguiar Comics PDFDocument18 pagesIFE ZazoAguiar Comics PDFArk'BenTrek True BluesNo ratings yet
- Iec 61851Document2 pagesIec 61851Radu Marian GospodaruNo ratings yet