Professional Documents
Culture Documents
Managed Security For A Not So Secure World Wp090991
Uploaded by
kp83Original Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Managed Security For A Not So Secure World Wp090991
Uploaded by
kp83Copyright:
Available Formats
White Paper: Managed Security
Managed Security for a Not-So-Secure World
CIOs need a strategy for a secure enterprise in todays insecure world.
It turns out that the infamous TJX Companies breach
in January 2007 was only the tip of the iceberg: there has been an explosion of data security incidents in the past few years. In 2008, the Identity Theft Resource Center (ITRC) reported 656 breaches, a 47 percent increase over 2007. And there have been 213 data breaches in the first five months of this year alone. This risky data environment is colliding with an IT landscape of shrinking resources. An April 2009 Lieberman Software survey of IT professionals discovered that 60 percent of respondents work at organizations that have cut their IT budgets, and 40 percent of organizations have reduced their IT teams. Such cuts leave fewer resources available to handle the ongoing need for compliance with a bevy of regulationsfrom the Sarbanes-Oxley Act (SOX) to the Health Insurance Portability and Accountability Act (HIPAA) to the Payment Card
WP090991 8/09
Qwest White Paper: Managed Security
Industry Data Security Standard (PCI DSS)to whatever new transparency requirements will arise from the banking crisis. But business must go on. CIOs must manage security risks while addressing business needs and focusing on revenue-generating activities. This paper offers a strategy for providing data security and protection that addresses the rising data threat landscape, the need for compliance, and todays lean IT staffs.
For more information about Qwests managed security services, visit us at www.qwest.com/business
Good Enough Isnt Always Enough
Unlike conventional projects with a beginning, middle and an end, IT security is never finished. The security program implemented yesterday may not be adequate tomorrow because new threats arise every day. Opportunistic predators, for example, exist both inside and outside the organization. Organized crime is a major concern from a financial perspective because their motivation is typically financial gain, which causes them to continually seek out potential network infrastructure vulnerabilities, and create new viruses and worms. This has significantly raised the quality of threats that companies must defend themselves against. Though most IT managers are vigilant and diligent in using the tools they have to protect corporate data, there are often blind spots that these predators will find and exploit. Ensuring corporate data is safe takes considerable proactive, continual monitoringor outside help. Keeping up with the high traffic in vulnerability disclosures is a perennial challenge and an important part of our program since we focus on proactively identifying and remediating risks, says Michael Glenn, director of information security and chief information security official (CISO) at Qwest Communications International Inc., a managed security provider. We have to balance our resources between our proactive, innovative programs and our reactive obligations, including a growing list of compliance auditing, certification and reporting activities. Those compliance issues can be burdensome. Mandated compliance with a wide and growing variety of state, federal and industry regulations places an increasing strain on IT staff.
Being Compliant
Some of these regulations, or parts of them, promote data protection within particular industries. For example, the Gramm-Leach-Bliley Act (GLBA) has privacy stipulations to protect information in the financial services industry, including companies providing financial products and services to consumers. For example, the GLBAs Financial Privacy Rule requires financial institutions to give their customers privacy notices that explain the institutions information collection and sharing practices. In addition, customers have the right to limit the sharing of their information. Failure to comply with these regulations can lead to stiff penaltiesHIPAA fines, for example, can be as high as $50,000 per violation. And the American Recovery and Reinvestment Act of 2009 will further tighten HIPAAs privacy and security rules for data breach notification, enforcement, audit trails and encryption. Then theres the PCI DSS, which governs payment card transactions. Here again, noncompliance can be expensive: for example, Visa could fine transaction processors between $5,000 and $25,000 a month if the merchants or retailers they represent are not PCI compliant. Whats troublesome is that companies often think theyre in compliance but end up finding out the hard way that theyre not. Take the examples of RBS WorldPay and Heartland Payment Systems, which process credit card payments. Before the end of 2008, they were believed to be PCI compliant. However, hackers tapped into their data, including cardholders private information. The point is that just checking a checkbox for compliance may not protect your organizations data; you must have solid security practices in place to first protect data, and then meet compliance obligations.
[2]
WP090991 8/09
Qwest White Paper: Managed Security
There are intangible costs as well. A breach in security of this magnitude causes a lack of confidence among current and prospective customers. CIOs and IT managers recognize this threat. In a recent survey conducted by IDG Research Services on behalf of Fiberlink Communications, 81 percent of respondents said that damage to their companys reputation from a data breach was their greatest concern, followed by legal consequences and costs (79 percent) and loss of critical data (74 percent). Things like proactive network monitoring, testing and tracking, complex firewall configuration, a comprehensive vulnerability management program, centralized logging and auditing, an access control program, and sound, comprehensive security policies are necessary for a good security program and to meet compliance obligations. Considerable staff and resources are also required. So, how does the CIO face these challenges?
Benefits of an Outsourcing Partner
r Staff: Professionally trained talent to
manage and implement security programs and plans
r Solutions: Carefully researched and
selected security technologies
r Cost: Lower total cost of ownership for
labor and technology through scaling, configuration, maintenance of technology solutions, training personnel, and researching processes and products
r Knowledge: Experience and knowledge
base to discover vulnerabilities, face new security threats and solve complex security problems
Outsourcing Managed Security
Given the security risk climate and the reduction in IT staffs, working with an IT and security service provider is more practical. With the appropriate foundation of outsourced services, security becomes manageable and reliable. Of course, cost is a consideration. You should conduct a thorough analysis of the time and expenses involved in using internal resources and then weigh it against an outsourcing providers cost model. For example, the cost of managing and configuring technology is a key component of the total cost of a security program. And you have to consider whether your in-house expertise is up to the task. Inevitably, difficult economic times can cause otherwise good people to make poor decisions, says Glenn. I expect to see a continued need for vigilance against malicious software and attacks like spear phishing that are rooted in fraud, along with the ever-present insider threat. In a downturned economy, you do not want to be significantly cutting your information security program. To stay abreast of vulnerabilities and threats, IT personnel must continually expand their knowledge and expertise, which can be challenging if budgets do not allow for a fully dedicated security staff or ongoing training. In addition, expert security professionals, especially those with credentials from professional associations, are in high demand, so retaining them can be difficult. On the flipside, a well-recognized, comprehensive security service provider has already gone through the rigors of recruiting and training quality security personnel. In addition, these teams have been exposed to a variety of enterprise security challenges from a diverse clientele. Tapping into this expertise offers not only a skilled security strategy, but also a fresh look at how to address risks. Another consideration is that IT and business processes are often in flux, due to changing market conditions and business demands. Managing them requires both time and broad experience; organizations with tight IT budgets can suffer process management constraints. An outsourcing partner can add value by bringing a wide range of expertise and the ability to look at the entire scope of a companys processes to identify potential obstacles or problem areas. Employing the best people and processes are only parts of the equation. You also need the right tech-
[3]
WP090991 8/09
Qwest White Paper: Managed Security
nology. Because new security tools and solutions are introduced every day, evaluating, purchasing and maintaining them requires time and an understanding of how they will best fit the organization. A feasible alternative is to lean on a managed security provider that has experience with a wide variety of solutions, and that can provide a thorough analysis of which tools are most appropriate.
term business goals. Using managed services to address security risks is a best practice to reduce costs, ensure compliance and allow IT staff to focus on critical business operations. Glenn offers this closing advice: Spend just as much, and preferably more of your energy on building relationships with key stakeholders across your enterprise than you spend learning the bits and bytes of the latest technical toy. If you have the right relationships with your business, you can always find a means to accomplish your objectives by making your business successful through good security practices and risk management. Learning those technical means together gives you more credibility. Take an honest look at your internal capabilities, and compare them to what a managed security services provider can offer, including economies of scale. Its likely that a security strategy that includes outsourcing in its mix will be a cost-effective, practical and winning solution.
Conclusion
In the IT landscape, vulnerabilities and threats arise constantly while new and shifting compliance regulations place increased pressure on data protection. And CIOs must face these issues with reduced staff and contracted budgets. A solid relationship with a managed service provider can be of great help, freeing CIOs to focus on core business operations, build better relationships with stakeholders and ultimately achieve short and long-
Failing to Comply
Data breaches have resulted in disciplinary actions and fines by the Federal Trade Commission (FTC) in numerous cases. Here are a few examples:
r The FTC disciplined a Texas-based mortgage company after it failed to provide reasonable security to
protect sensitive customer data. Third-party home sellers were able to access private data without security measures in place. A hacker compromised the data by breaking into a home sellers computer, obtaining the lenders credentials and using them to access hundreds of consumer reports. Because this mortgage company had inadequate data protection, they were liable for the security breach.
r When hackers stole the personal data of some 46 million customers of retail conglomerate TJX Companies, the FTC attributed the breach to a failure by TJX to use reasonable and appropriate security measures on its networks. As a result, a third party must audit the company every other year for 20 years and TJX must show improvement in its network security, service provider selection and how it handles consumer information. The retailer also negotiated a settlement reported at more than $40 million with Visa International.
r After it was discovered that hackers had accessed the sensitive information of hundreds of consumers, an online seller of computer supplies was admonished by the FTC. The company failed to provide reasonable security to protect sensitive customer data such as personal information and credit card numbers. The vendor suffered bad publicity and diminished overall customer confidence.
Source: www.ftc.gov
[4]
WP090991 8/09
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (894)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- Financial Reporting and AnalysisDocument50 pagesFinancial Reporting and AnalysisGeorge Shevtsov83% (6)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Desktop Engineering Magazine - Article On Collaboration SoftwareDocument6 pagesDesktop Engineering Magazine - Article On Collaboration Softwarekp83No ratings yet
- Construction Digest - Tupelo Miss Mega SiteDocument4 pagesConstruction Digest - Tupelo Miss Mega Sitekp83No ratings yet
- Those Who Can Do Teach!: To Sir With LoveDocument3 pagesThose Who Can Do Teach!: To Sir With Lovekp83No ratings yet
- Target Marketing With GISDocument4 pagesTarget Marketing With GISgilangwhpNo ratings yet
- Network Computing Magazine - Article On Enterprise Resource Planning SoftwareDocument4 pagesNetwork Computing Magazine - Article On Enterprise Resource Planning Softwarekp83No ratings yet
- THI VacuumGaugeBrochure Proof4Document2 pagesTHI VacuumGaugeBrochure Proof4kp83No ratings yet
- Civil Engineering News - For MetaCarta CorporationDocument3 pagesCivil Engineering News - For MetaCarta Corporationkp83No ratings yet
- Engineering News Record - Article On License ManagementDocument3 pagesEngineering News Record - Article On License Managementkp83No ratings yet
- 2 24551 Virtualization SC 0113Document9 pages2 24551 Virtualization SC 0113kp83No ratings yet
- Acuta Journal - Article On GIS and McHenry Country CollegeDocument4 pagesAcuta Journal - Article On GIS and McHenry Country Collegekp83No ratings yet
- Planning Article On Homelessness in America - by Jim RomeoDocument6 pagesPlanning Article On Homelessness in America - by Jim Romeokp83No ratings yet
- The Essential Ingredient For Today's Enterprise: Mobile SecurityDocument4 pagesThe Essential Ingredient For Today's Enterprise: Mobile SecurityAmila KumanayakeNo ratings yet
- Teradyne Hastings Vacuum Gage BrochrureDocument2 pagesTeradyne Hastings Vacuum Gage Brochrurekp83No ratings yet
- Czarcie Kopyto®: Purchase Order FormDocument1 pageCzarcie Kopyto®: Purchase Order Formandre nusaNo ratings yet
- MortgageDocument142 pagesMortgageSubirNo ratings yet
- International Banking and Future of Banking and FinancialDocument12 pagesInternational Banking and Future of Banking and FinancialAmit Mishra0% (1)
- DDDDDocument2 pagesDDDDMuhammad AmjadNo ratings yet
- Assignment Acc106 Jan 2012Document11 pagesAssignment Acc106 Jan 2012irfanzzz75% (8)
- Lembar Ukk Ud AbadiDocument62 pagesLembar Ukk Ud Abadibayufitriani3953% (15)
- Paypal Fraudulently Holding PaymentsDocument407 pagesPaypal Fraudulently Holding PaymentsCatsLair ArchivesNo ratings yet
- Audit Chapter 14Document36 pagesAudit Chapter 14Arfini LestariNo ratings yet
- b2c E-Commerce ReviewDocument10 pagesb2c E-Commerce ReviewadiltsaNo ratings yet
- Technical Seminar Topic Name 6G Mobile Technology: Seminar By: Karthik Rajaram (1BH17CS028) Sem: VIII Department of CSEDocument9 pagesTechnical Seminar Topic Name 6G Mobile Technology: Seminar By: Karthik Rajaram (1BH17CS028) Sem: VIII Department of CSEYATHISH M GNo ratings yet
- NBFC Sector ReportDocument8 pagesNBFC Sector Reportpawankaul82No ratings yet
- Identity Theft WebquestDocument2 pagesIdentity Theft Webquestapi-256439491No ratings yet
- Zakiyyah Logan Joins PrivatePlus MortgageDocument2 pagesZakiyyah Logan Joins PrivatePlus MortgagePR.comNo ratings yet
- Ekb OZVi JDKQ 37 Ho GDocument7 pagesEkb OZVi JDKQ 37 Ho GSahil SalujaNo ratings yet
- Unit Four: Hotel Staff, Planning and Booking A HolidayDocument7 pagesUnit Four: Hotel Staff, Planning and Booking A HolidayInna PapillionNo ratings yet
- Assignment 1 SolutionDocument7 pagesAssignment 1 SolutionTeh Boon SiangNo ratings yet
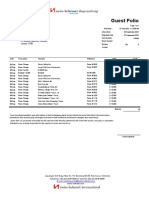
- Guest Folio: Pt. Gilang Agung Perkasa Gedung Artha Graha Jl. Jenderal Sudirman, Senayan Jakarta 12190Document1 pageGuest Folio: Pt. Gilang Agung Perkasa Gedung Artha Graha Jl. Jenderal Sudirman, Senayan Jakarta 12190Renno PartianaNo ratings yet
- Franchise Business Scenario in Bangladesh ExplainedDocument19 pagesFranchise Business Scenario in Bangladesh Explainedmadkiiing100% (1)
- Entrepreneurship Wk. 7: LessonDocument4 pagesEntrepreneurship Wk. 7: LessonJerome Benipayo78% (9)
- CSS12 LAS Patch-Panel-Board 2022Document4 pagesCSS12 LAS Patch-Panel-Board 2022Tirso Bercasio Jr.No ratings yet
- Mobile BankingDocument19 pagesMobile BankingIbe CollinsNo ratings yet
- Ethio Telecom - WikipediaDocument7 pagesEthio Telecom - WikipediaAltesa AbicheNo ratings yet
- Final achievement test reviewDocument8 pagesFinal achievement test reviewJennie LacNo ratings yet
- PTP 600 Series: Point-To-Point Communications in Virtually Any EnvironmentDocument4 pagesPTP 600 Series: Point-To-Point Communications in Virtually Any EnvironmentCheiston FigueiredoNo ratings yet
- Dog Concierges, LLC: Transaction Analysis and Statement of Cash Flows PreparationDocument9 pagesDog Concierges, LLC: Transaction Analysis and Statement of Cash Flows PreparationCristina Elizabeth Portilla BravoNo ratings yet
- Case Study On Sachet InsuranceDocument2 pagesCase Study On Sachet Insurancesmd.naeem2No ratings yet
- SLM-BBA-Supply Chain and Logistics ManagementDocument153 pagesSLM-BBA-Supply Chain and Logistics ManagementVijina CpNo ratings yet
- AddValue Safari BGANDocument2 pagesAddValue Safari BGANMinh Tran VanNo ratings yet
- Must Read Illustrated Guid To Kubernetes NetworkingDocument41 pagesMust Read Illustrated Guid To Kubernetes NetworkingdileepNo ratings yet