Professional Documents
Culture Documents
E-learning resource locator software requirements specification
Uploaded by
janajohnny0 ratings0% found this document useful (0 votes)
336 views58 pagesE-learning Resource Locator
Original Title
E-learning Resource Locator
Copyright
© © All Rights Reserved
Available Formats
DOCX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentE-learning Resource Locator
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
336 views58 pagesE-learning resource locator software requirements specification
Uploaded by
janajohnnyE-learning Resource Locator
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
You are on page 1of 58
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
1
GIZMOS
SOFTWARE REQUIREMENT SPECIFICATION
SVS COLLEGE OF ENGINEERING, COIMBATORE
TEAM NAME: GIZMOS
PROJECT GUIDE
Siva Kumar. M
Assistant Professor
Department of Computer Science and Engineering
TEAM MEMBERS
Sangavee.V
Ardra Menon
DEPARTMENT
Department of Computer Science and Engineering
III-YEAR
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
2
GIZMOS
CONTENTS
1. INTRODUCTION
1.1. Project Summary...4
1.2. Purpose...4
1.3. Scope....4
2. PROJECT MANAGEMENT
2.1. Project Planning Scheduling
2.1.1. Project Development Approach.5
2.1.2. Project Planning..6
2.2. Risk Management
2.2.1. Risk Identification.7
2.2.2. Risk Analysis.7
2.2.3. Disaster Prevention..8
2.2.4. Risk Planning9
2.2.5. Risk Avoidance9
2.2.6. Risk Reduction..10
3. SYSTEM ANALYSIS
3.1. Objective10
3.2. Preliminary Analysis..11
3.3. System Requirements13
3.4. System Requirements Study.14
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
3
GIZMOS
4. SYSTEM DESIGN
4.1. Use Case Diagram15
4.2. Class Diagram16
4.3. Sequence Diagram.17
4.4. Architectural Diagram.20
4.5. Database Diagram...21
4.6. Deployment Diagram22
4.7. Database22
5. IMPLEMENTATION DETAILS
5.1. Module Specification.24
6. TESTING
6.1. Testing..26
6.2. Testing Plan27
6.3. Testing Method28
6.4. Test Cases33
7. SCREENSHOTS ..39
8. CONCLUSION..59
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
4
GIZMOS
1. INTRODUCTION
1.1 PROJECT SUMMARY
The aim of the project is to set a website for registered users, who can
download E-Books and clear doubts through the forum. It also keeps the track
of uploaded books and provides links to download the books directly. The users
can give their feedbacks. Administrator views the feedbacks and generates
reports.
1.2 PURPOSE
To create an education based website to help students to get all the
resources and study materials of every courses available. It uses E-Book
facility. It is reliable and time efficient approach compared to all the links of the
website provided by any search engine while searching for course materials. E-
learning can be applied for all levels of schooling from grade school to graduate
degrees, and is versatile enough to accommodate all learning styles.
1.3 SCOPE
Acts as a platform to provide interaction between professor and students
to clear their doubts.
Provides official and legal links of the website from which the student can
download resources and study materials of relevant course.
Helps to get associated with the well-known publication house so as the
students can access soft copy of the books published for future use.
Component based development provides better scalability and
maintainability.
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
5
GIZMOS
2. PROJECT MANAGEMENT
2.1 Project Planning and Scheduling
2.11 Project Development Approach
In present scenario, people have lots of job to do and budget is also very
less. So everybody wants to learn from wherever they are and clarify their
doubts to experts at instance of time. Users need an online resource to get
materials of E-Books and develop their skills. For a website an extra-ordinary
and attractive look is very much necessary to attract new users and second is
very good functionalities. The user can easily fine their books by giving
keywords. The users can also give their feedbacks for the development of the
website. Likewise they can use the forum to ask their doubts and professors
and mentors will reply to their doubts. Various other features can be executed
with the minimum efforts and accordingly database design has been setup for
this website.
Software Process Model
To solve actual problems in industry setting, software engineer or a team
of engineers must incorporate a development strategy that encompasses the
process, methods and tools layers and generic phases. This strategy is often
referred to as process model or a software engineering paradigm. A process
model for software engineering chosen based on the nature of the project and
application, the method and tools to be used, and the controls and deliverables
are required.
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
6
GIZMOS
2.12 Project Planning
Software Project Scheduling is an activity that distributes estimated
efforts across the planned duration by allocating the efforts to specific software
engineering tasks.
For this project, the requirements are examined from different aspects of
the developments requirements. Then the whole project is divided into
modules and according to those modules the development work has been done.
2.2 RISK MANAGEMENT
Risk management is the process of measuring, or assessing, risk and
developing strategies to manage it. Strategies include transferring the risk to
another party avoiding the risk, reducing the negative effect of the risk, and
accepting some or all of the consequences of a particular risk. Traditional risk
management focuses on risks stemming from physical or legal causes (e.g.
natural disaster, fire or accidents). Financial risk management, on the other
hand, focuses on risk that can be managed using traded financial instruments.
In ideal risk management, a prioritization process is followed whereby
the risks with lower probability of occurring are handled first, and risk with
lower probability of occurrence and lower loss are handled later.
Steps in the risk management process establishing the context involves
Planning the remainder of the process.
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
7
GIZMOS
Mapping out the following: the scope of the exercise, the identity
and objectives of stakeholders and the basis upon which risks will
be evaluated.
Defining a framework for the process and an agenda for the
identification.
Developing an analysis of risk involved in the process.
2.2.1 Risk Identification
After establishing the context, the next step in the process of managing
risks is to identify potential risks. Risks are about events that, when triggered,
cause problems, Hence, risk identification can start with the source of
problems, or with the problem itself.
In this project there can be following risks:
The order risk is associated with the software. If in the software the
wrong user is authorized by mistake then he may do changes that cause the
system in dangerous mode. There can be risk of natural threats.
2.2.2 Risk Analysis
Once risks have been identified, they must be assessed as to their
potential severity of loss and to the probability of occurrence. Regardless of the
prevention techniques employed, possible threats that could arise inside and
outside the organization need to be assessed. Regardless of the type of threat,
the goals of the business recovery planning are to ensure the safety of
customers, employees and other personal during the following a disaster.
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
8
GIZMOS
If by mistake any person hack Administrator password then he can
change the data in software and can leak information. Same thing occurs if the
wrong user is authorized. The software may be in problem by natural threat.
E.g. internal flooding, external flooding, etc.,
2.2.3 Disaster Prevention
Because a goal of business recovery planning is to ensure the safety of
personnel and assets during the following a disaster, a critical aspect of the risk
analysis process is to identify the preparedness and preventive measures in
place at any point in time. Once the potential areas of high exposure to the
organization are identify, additional preventive measures can be considered for
implementation.
Disaster prevention and preparedness begins at the top of organization.
The attitude of senior management toward security and prevention should
permeate the entire organization. Therefore, managements support of disaster
planning can focus attention on good security and prevention techniques and
better prepare the organization for unwelcome and unwanted.
Disaster prevention techniques include two categories
Procedural prevention
Physical prevention
Procedural prevention related to activities performed on a day-to-day,
month-to-month, or annual basis, relating to security and recovery. Procedural
prevention begins with assigning responsibility for overall security of the
organization to an individual with adequate competence and authority to meet
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
9
GIZMOS
the challenges. The objective of procedural prevention is to define activities
necessary to prevent various types of disasters and ensure that these activities
are performed regularly.
Physical prevention and preparedness for disaster brings when a site is
constructed. It includes special requirements for building constructions, as well
as fire protection for various equipment components. Special considerations
include: computer area, fire detection and extinguishing system, records
protection, air conditioning, heating, and ventilation, electrical supply and UPS
system, emergency procedures, vault storage area(s), archival systems.
2.2.4 Risk Planning
Once risks have been identified and assessed, all techniques to manage
the risk fall into one or more of these four major categories:
Tolerate (retention)
Treat (mitigation)
Terminate (elimination)
Transfer (buying insure)
Ideal use of these strategies may not be possible. Some of them may involve
tread-offs that are not acceptable to the organization or a person making the
risk management decisions.
2.2.5 Risk Avoidance
It includes not performing an activity that could carry risk. An example
would be not buying a property or business in order to not take on the liability
that comes with it. Another would be not to take the risk that the airplanes
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
10
GIZMOS
were to be hijacked. Avoidance may seem the answer to all risk, but avoiding
risk also means losing out on the potential gain that accepting (retaining) the
risk may have allowed, not entering a business to avoid the risk of loss also
avoid the possibility of earning profits.
2.2.6 Risk Reduction
It involves methods that reduce the severity of the loss. Examples include
sprinklers designated to put out a fire to reduce the risk of loss by fire. This
method may cause a greater loss by water damage and therefore may not be
suitable. Hal on fire suppression systems may mitigate that risk, but the cost
may be prohibited as a strategy. Modern software development methodologies
reduce risk by developing and delivering software incrementally. Early
methodologies suffered from the fact that they only delivered software in the
final phase of development; any problems encountered in earlier phases meant
costly rework and often jeopardized the whole project. By developing in
iteration, software project can limit effort wasted to a single iteration. A current
trend in software development, spearheaded by the extreme programming
community, is to reduce the size of iteration to the smallest size possible,
sometimes as little as one week is allocated to an iteration.
3. SYSTEM ANALYSIS
3.1. Objective
A key objective of this system is that it consolidates the data in one
central location. This will enable easy management of all information and
ensure data integrity across the entire breadth of the system. The E-Learning
Resource Locator will provide such a facility for users to get E-Books and to
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
11
GIZMOS
connect with professors and mentors of various top universities. It is very
useful for the users to save their time and money.
To provide official and legal link to websites from which the user can
download materials directly.
To get associated with well known publication house so students can
access soft copies of the books.
It saves the time of the user.
The main object of the project is to create a system that allows users to
get connected with others and to make use of the E-Books
3.2. Preliminary Analysis
Scope
Due to Internet access users use Internet more and more for their
education needs. They also save time and money by doing so and for
more of their related activity.
This system should provide facility to register online.
The system should provide the facility for inquiry if the user has a query.
The system should be able to generate user related report
Feasibility Study
A feasibility study is carried out to select the best system that meets
performance requirements. A feasibility study is designed to provide an
overview of the primary issues related to a business idea. The purpose is to
identify any make or break issues that would prevent your website from
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
12
GIZMOS
being successful in the market place. In other words, a feasibility study
determines whether the ideas make sense.
Feasibility study provides a lot of information necessary for the website
plan.
Technical Feasibility
The system will be hosted on the internet so company need internet
connection in that organizations as well as they need DB2 to store the data
related to users. This system can be easily supported by the hardware and
software requirements of any system. The system can also produce its
required output.
Behavioral Feasibility
Proposed system will behave according to the requirement made or not.
Responses time of the system must be noticed because it is a web based
system whether it takes too much time to response or give quick response
or response in the specific period of time this consideration is more
important. Time consuming processes are possible to run on this
environment or not are also important.
Operational Feasibility
The proposed system will meet the operational requirements like system
performance, accessibility of information, client acceptance and efficient
solutions to the queries of the user. If user has some basic knowledge of
Internet, user can operate this application easily. It provides easy user
interface.
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
13
GIZMOS
Operational feasibility has been considered from the users point of view.
This application once deployed, can run easily without any maintenance at
this point of time. After the inclusion of database in future, the database
might need some clean up after some period of time. If the database size
becomes large, then it might need some changes in handling of the
application and might require some optimization so that application runs
faster and retrieves data faster.
3.3 System Requirements
Hardware Interface
Software Interface
S.No
1 Client on the Internet Web Browser, Operating System (Any)
2 Client on the Intranet Web Browser, Operating System (Any)
3 Application Server WASCE, Operating System (Any)
Processor RAM Disk Space
Client Side
IE/Mozilla Firefox/
Netscape Navigator
Any Standard Intel or
AMD Processor
512 MB 50 100 MB
Server Side
JAVA PLATFORM,
WASCE
Pentium Dual Core
2.8 GHz
1 GB 2 GB
DB2 Pentium Dual Core
2.8 GHz
1 GB 5 GB (Excluding
data size)
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
14
GIZMOS
4 Database Server DB2, Operating System (Any)
5 Application Environment Java
3.4. System Requirement Study
The requirements can be classified as below
Functional Requirements
Non-functional Requirements
Users:
Browsing through the E-Learning to see the E-Books in each
category and clarify their doubts.
Adequate searching mechanisms for easy and quick access to
particular products and services
Admin:
Uploading new books this its description.
Check the feedbacks from various users.
Generate Report between a particular period
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
15
GIZMOS
4. SYSTEM DESIGN
4.1. USECASE DIAGRAM
End user
Student Professor Publication House Administrator
Sign in
Feedback
Search
Register
Forum
Upload
Update
Download
Authentication
Feedback
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
16
GIZMOS
4.2. CLASS DIAGRAM
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
17
GIZMOS
4.3. SEQUENCE DIAGRAM
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
18
GIZMOS
For Professors/Mentors:
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
19
GIZMOS
For Students:
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
20
GIZMOS
4.4. ARCHITECTURE DIAGRAM
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
21
GIZMOS
4.5. DATABASE DIAGRAM
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
22
GIZMOS
4.6. DEPLOYMENT DIAGRAM
4.7. DATABASE
REGISTRATION:
KEY NAME DATA TYPE LENGTH NULLABLE
RID INTEGER 4 NO
FIRSTNAME VARCHAR 50 NO
LASTNAME VARCHAR 50 NO
EMAIL VARCHAR 50 NO
PASSWORD VARCHAR 50 NO
USERTYPE VARCHAR 50 NO
ADDRESS VARCHAR 100 NO
MOBILENUMBER BIGINT 8 NO
REGISTERDATE DATE 4 NO
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
23
GIZMOS
FEEDBACK:
KEY NAME DATA TYPE LENGTH NULLABLE
FDATE DATE 4 NO
FID INTEGER 4 NO
NAME VARCHAR 50 NO
EMAIL VARCHAR 50 NO
COMMENTS VARCHAR 200 NO
UPLOAD:
KEY NAME DATA TYPE LENGTH NULLABLE
BOOK_ID INTEGER 4 NO
PATH VARCHAR 150 NO
AUTHOR VARCHAR 50 NO
KEYWORDS VARCHAR 50 NO
PUBLISHDATE VARCHAR 50 NO
CATEGORY VARCHAR 50 NO
DESCRIPTION VARCHAR 400 NO
TECHNICAL DOUBTS:
KEY NAME DATA TYPE LENGTH NULLABLE
TDID INTEGER 4 NO
NAME VARCHAR 200 NO
SUBJECT VARCHAR 200 NO
QUERIES VARCHAR 200 NO
TDDATE DATE 4 NO
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
24
GIZMOS
TECHNICAL ANSWERS:
KEY NAME DATA TYPE LENGTH NULLABLE
TAID INTEGER 4 NO
TDID VARCHAR 4 NO
NAME VARCHAR 200 NO
ANSWERS VARCHAR 800 NO
TADATE DATE 4 NO
5. IMPLEMENTATION DETAILS
5.1. Module Specification
These are different modules in the system
Administrator Module
Login
User Module
Feedback Module
Uploading/downloading Module
Forum Module
Administrator
This module can help administrator to manage the system. It
contains administrator login. If administrator is valid then administrator
can manipulate the data in the system. It also deals with the database of
the system. The administrator can check the feedbacks and generate
reports.
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
25
GIZMOS
Login
In this page the user should enter the user name and password. If
the user has valid user name and password then user can make use of the
website and download books
Feedback
Users of the website ie., students, professors, mentors, universities
and publication houses can give their feedbacks. Administrator can view
these feedbacks between a particular period of time.
Uploading/Downloading
Administrator and Publication Houses can upload books in sever.
Students, Professors and universities can download the books by
specifying the keywords. Links are also provided for users to download
the materials directly from various other websites.
Forum
Users of the website can post their queries. Other users can view
these queries and if they know the answer they can share their answers
in the forum. Through this the user can communicate with professors and
mentors of various universities.
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
26
GIZMOS
6. TESTING
6.1. Testing
Errors are more common, more pervasive and more troublesome in
software than with other technologies.
Software Testing has a duel function, it is used to establish the presence
of defects in program and it is used to help judge whether or not the program is
usable in practice. Thus software testing is used for validation and verification,
which ensure that software conforms to its specification and meets the need of
the software customer.
Developer resorted Alpha testing, which usually comes in after the basic
design of the program has been completed. The project scientist will look over
the program and give suggestion and ideas to improve or to correct the design.
They also report and give ideas to get rid of around any major problems. There
is bound to be a number of bugs after a program have been created.
Software Inspection
Analyze and check system representation such as the requirements
document, design diagram and the program source code. They may be applied
to all stages of the process.
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
27
GIZMOS
Testing Process
6.2. Testing Plan
The Testing Process:
Developer tests the software process activities such as Design,
Implementation and Requirement Engineering. Because, design errors are very
costly to repair one system has been started to operate. Therefore, it is quite
obvious to repair them at early stage of the system. So analysis is the most
process of any process.
Unit
Testing
Module
Testing
Sub-System
Testing
System
Testing
Acceptance
Testing
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
28
GIZMOS
Requirements Tractability
As most interested portion is whether the system is meeting its
requirements or not, for that testing should be planned so that all requirements
are individually tested. Developer checked the output of certain combination of
input, which gives desirable result, or not. Strictly stick to your requirement
specifications, give you the path to get desirable result from the system.
Tested Items
Our tested items are like image reading, plotting, color-shedders and
distance between any two selected points on the image, query system. This
portion is very interesting, first of all put the mouse curser on a specific point
and note down the elevation, then after that put height value into the text box
for the query processing, then at particular height bearing areas will be
separated out from the other regions of the map by other color and likewise.
Testing Schedule
Developer tests each procedure back-to-back so that errors and
omissions can be found as early as possible. Once the system has been
developed fully developer tests it on other machines, which differ in
configuration.
6.3 Testing Method
Software testing involves executing an implementation of the software
with the test data and examining the output of the software and its operational
behavior to check that it is performing as required.
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
29
GIZMOS
Statistical Testing
Statistical Testing is used to test the programs performance and
reliability and to check how it works under operational conditions. Tests are
designed to reflect the actual user inputs and there frequency.
The stages involved in the static analysis for the systems are follows:
Control flow analysis
Unreachable code
Unconditional branches into loops.
Data use analysis
Variable used before initialization
Variables declared but never used
Variables assigned twice but never used between assignments
Possible array bound violations
Declared variables
Interface Analysis
Parameter type mismatches
Parameter number mismatches
Non-uses of the result of function
Uncalled function and procedure
Storage Management Faults
Images not stored in resources
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
30
GIZMOS
Programs non-volatile memory out of Bound.
Defect Testing
Defect Testing is intended to find inconsistencies between a program and
its specification. These consistencies are usually due to the program faults or
detect.
Black-Box Testing
In Black-Box testing or Functional Testing, Developer is concerned about
the output of the module and the software, i.e., whether the software gives
proper output as per the requirements or not. In other words, these testing
aims to test a programs behavior against its specification without making any
reference to the internal structure of the program or the algorithms used.
Therefore the source code is not needed, so even purchased modules can be
tested. The program just gets a certain input and its functionality is examined
by observing the output.
This can be done in the following way:
Input Interface
Processing
Output Interface
The tested program gets certain inputs. Then the program does its job
and generates a certain output, which is collected by a second interface.
This result is then compared to the expected output, which has been
determined before the test.
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
31
GIZMOS
White-Box Testing:
White box testing is used as an important primary testing approach. Here
code is inspected to see what it does, test are designed to exercise the code.
Code is testing user code scripts, driver, etc which are employed to directly
interface with the drive and the code.
The tester can analyze the code and use the knowledge about the stricter
of a component to derive the test data.
Structural Testing:
Developer has done path testing to exercise every independent execution
path through a component or program. If every independent path is executed
then all statements in the component must have been executed at least once.
The structure of our program is also checked.
Integration Testing
After our individual modules developer tested out developer go to the
integrated to create a complete system. This integration process involves
building the system and testing the resultant system for problems that arise
from component interactions.
Developer has applied top down strategy to validate high level
components of a system before design and implementation have been
completed. Because, our department process started with high level
components and developer worked down the component hierarchy.
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
32
GIZMOS
Performance Testing
Performance testing is designed to test the run time performance of the
system within the context of the system.
Condition Testing
Condition Testing is a test case design method that exercises the logical
conditions contained in a program module. If the condition is incorrect, then as
least one part of the condition is incorrect. It may include
Boolean variable error
String index out of Bound error
Null pointer assignment
Input Output Connection Exceptions
Images or Map Unloaded errors
Parsing(conversion) errors
Arithmetic expression error
Interface Testing
Interface Testing is integral part of Integration testing. Therefore
Developer checked for the
Interface Misuse
Interface Misunderstanding
Developer examined the code to be tested and explicitly list each call to
an external component. In the system, standards tests for GUIs have been
performed, which are as follows
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
33
GIZMOS
The position and related labels for all controls checked.
All menu functions and sub functions verified for correctness.
Validations for all input done.
Each menu functions tested, whether it invokes the corresponding
functionality properly
Pull down controls was verified for properly functionality.
Whether the non-editable text control is disabling and it was also
verified that it doesnt exceed the maximum length.
Whether the system prompts the user with appropriate message as
and when invalid information is entered.
Object Testing
Object testing is to test object as individual components, which are often
larger than single function. Here following activities have taken placed.
Testing the individual operations associated with object.
Testing individual object classes
Testing cluster of objects
Testing object-oriented system
6.4. TEST CASES
Equivalence Partitioning
Valid Input Valid Output
System
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
34
GIZMOS
Input equivalence partitioning is a set of data where all of the set member
should be processed in an equivalent way. Output equivalence partitions are
program output that has common characteristics so can be considered as a
distinct class.
Purpose
The purpose of the test cases is to test the various input and see the
output produce any error or not. There are different test cases according to the
system. It is tested with different types of value like single value multiple value
and see it can generate expected output.
Reliability of the System
There are three approaches to reliability of the system
Error Avoidance
Error Avoidance is impossible in any system, as it points to
prevention of errors from occurring in system. In our system, we
cannot prevent occurrence of errors because, if user does not call
methods properly and does not input appropriate parameters, we
are unable to avoid errors.
Error Detection and Correction
Error Detection corresponds to reorganization of errors when they
are encountered. In the system, developer user message boxes to
prompt errors to users. We also use catch structure to prompt
errors. Message box shown to users are in well understood forms.
System prompt varicose error message like file does not exist,
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
35
GIZMOS
whenever the user tries to open any other file instead of image file.
However, system does not support correction of errors: it is users
responsibility to take appropriate action.
Error Tolerance
Error Tolerance refers to reorganize of errors when they occur, but
enables system to keep running through degraded system. In system will
never shutdown automatically due to errors, but is it possible that
because of errors it may not work efficiently. For example, if invalid
image is given then system will prompt error and it will not shutdown.
Furthermore, if user does not add image file, in that case, that layer is not
displayed nor activated and any further operations are not done.
There are two levels of reliability:
First level
Second level
First Level
During the project development, we performed a thorough and effective
determination of system requirements. This is necessary to satisfy the
reliability at first level. Our system is meeting right requirement and thus it
is reliable at first level.
Second Level
During the testing phase of system, it does not produce unexpected
output unless and until the user make some mistake. Moreover, a chance of
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
36
GIZMOS
system failure is almost zero, so system is meeting second level reliability
too. Hence, we can say that system is reliable.
Test Case Number 1
Name Valid user test
Description This test case will check whether User ID and Password
is valid or not. If not it will not allow the user to operate
Input Data 1. Valid ID and Password (already defined)
2. Valid ID and wrong Password
3. Wrong ID and wrong Password
Expected Output 1. System allow login
2. System prompts error that user name is wrong
3. System prompts error that user name is wrong
Actual Output 1. System allow login
2. System prompts error that user name is wrong
3. System prompts error that user name is wrong
Test Case Number 2
Name Blank field validation
Description This test will check whether all the fields in the form are
entered
Input Data Fill the various fields of the form
Expected Output 1. Shows message that the field is blank
2. Message of success
Actual Output 1. Shows message that the field is blank
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
37
GIZMOS
2. Message of success
Test Case Number 3
Name Feedback validation
Description This test case will check whether the feedback given by
the user is stored to the database
Input Data User fills all the fields
Expected Output Feedback success message
Actual Output Feedback success message
Test Case Number 4
Name Report generation
Description This test case will check whether the report is
generated in admin login
Input Data Admin clicks on Report
Expected Output pdf file will automatically start its download
Actual Output pdf file will automatically start its download
Test Case Number 5
Name Download validation
Description This test case checks whether the book available in the
keyword is downloading properly
Input Data User clicks download
Expected Output Books starts downloading and stored in the system
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
38
GIZMOS
Actual Output Books starts downloading and stored in the system
Test Case Number 6
Name Registration validation
Description This test case will check whether the user registration is
confirmed and a mail is sent to the registered user
Input Data User fills all the forms and give confirm
Expected Output A mail is sent to the user with user name and password
Actual Output A mail is sent to the user with user name and password
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
39
GIZMOS
7. SCREENSHOTS
Home Page
About us
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
40
GIZMOS
Contact details
Admin Login
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
41
GIZMOS
User Login
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
42
GIZMOS
Registration of new user
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
43
GIZMOS
User login
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
44
GIZMOS
Edit faculty profile
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
45
GIZMOS
Update Faculty profile success
Mentor Profile
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
46
GIZMOS
Mentor profile Updated
Student Profile
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
47
GIZMOS
Student Profile Update
Student Profile update success
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
48
GIZMOS
Publisher profile
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
49
GIZMOS
Publisher Profile Update
Publisher Profile update success
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
50
GIZMOS
Feedback
Feedback Success
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
51
GIZMOS
Download
Search Results
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
52
GIZMOS
Links to download
Forum
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
53
GIZMOS
After Posting
When another user views the queries
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
54
GIZMOS
Replying to the queries
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
55
GIZMOS
Uploading E-Books
Uploading Success
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
56
GIZMOS
Admin page
Viewing Feedback by Admin
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
57
GIZMOS
Generating reports by Admin
E-LEARNING RESOURCE LOCATOR
IBM TGMC 2012
58
GIZMOS
8. CONCLUSION
Students participating in E-Learning environments will prepare them not
only for success as lifelong learners but also to become leaders who dare to
discover. The E-learning report provides a foundation for a process to continue
to review and improve our learning environment by the full engagement of the
University community in ongoing effort to examine the issues, explore the
emerging technologies and determine the priorities. Nothing is above customer
satisfaction. So the rules need to be kept flexible to meet user needs and
preferences at different times. Other models can be applied but is beyond the
scope of the team.
You might also like
- Risk Management Plan (RMMMDocument20 pagesRisk Management Plan (RMMMMaitray WaniNo ratings yet
- Paper-1 Effects of Software Security On Software Development Lifecycle and Related Security IssuesDocument9 pagesPaper-1 Effects of Software Security On Software Development Lifecycle and Related Security IssuesRachel Wheeler100% (1)
- BENUE STATE UNIVERSITY SOFTWARE RISK MANAGEMENTDocument10 pagesBENUE STATE UNIVERSITY SOFTWARE RISK MANAGEMENTMOONLAITNo ratings yet
- SE Solved QBDocument68 pagesSE Solved QBmramolsalunkheNo ratings yet
- Aadamsoo Anne MaiDocument57 pagesAadamsoo Anne Maiharish babu aluruNo ratings yet
- Risk ManagementDocument41 pagesRisk ManagementKarnam SirishaNo ratings yet
- Project Risk ManagementDocument23 pagesProject Risk ManagementGugine NeveNo ratings yet
- Se 5Document11 pagesSe 5gcyvuNo ratings yet
- PM-5 Risk ManagementDocument34 pagesPM-5 Risk ManagementBizuayehu DesalegnNo ratings yet
- BT0092 Project Management ActivitiesDocument10 pagesBT0092 Project Management Activitieshemant kumarNo ratings yet
- SPM AssignmentDocument24 pagesSPM Assignmentnuhamin zNo ratings yet
- Part 5 Risk ManagementDocument17 pagesPart 5 Risk ManagementPrincess Dayana Quiozon100% (1)
- Cyb 504Document20 pagesCyb 504yormie2019No ratings yet
- Risk ChapterDocument6 pagesRisk ChapterJui BhanushaliNo ratings yet
- Risk Chapter OneDocument16 pagesRisk Chapter OneJui BhanushaliNo ratings yet
- Unit 5Document72 pagesUnit 5227r5a0522No ratings yet
- Ilovepdf Merged 4c7bdd33 159a 4e13 8c6b De1ec358b3caDocument75 pagesIlovepdf Merged 4c7bdd33 159a 4e13 8c6b De1ec358b3cagopalprajapatimovieNo ratings yet
- Risk Management in System Requirement AnalysisDocument8 pagesRisk Management in System Requirement AnalysissrikarNo ratings yet
- Qualitative and Quantitative Risk AnalysisDocument10 pagesQualitative and Quantitative Risk AnalysisYl WongNo ratings yet
- Risk Analysis and ManagementDocument7 pagesRisk Analysis and ManagementNelson LuzigaNo ratings yet
- Risk Management: 1. Project Risks 2. Technical Risks 3. Business RisksDocument11 pagesRisk Management: 1. Project Risks 2. Technical Risks 3. Business RisksSUREDDY TANUJA TANUJA (RA2132003010015)No ratings yet
- SE Unit 5 Notes_UpdatedDocument25 pagesSE Unit 5 Notes_Updatedhedol58662No ratings yet
- Risk Management in Software Development: Reducing Requirements RisksDocument8 pagesRisk Management in Software Development: Reducing Requirements RiskssrikarNo ratings yet
- PRM 6Document23 pagesPRM 6sanjeev shimarNo ratings yet
- Managing A Successful Computing ProjectDocument20 pagesManaging A Successful Computing ProjectAryan AmatyaNo ratings yet
- PMAN637Document16 pagesPMAN637sunita@pasNo ratings yet
- Case Study ON: Risk Analysis and ManagementDocument26 pagesCase Study ON: Risk Analysis and ManagementNishant NairNo ratings yet
- Software Engineering-Assignment 3..Document8 pagesSoftware Engineering-Assignment 3..Tichman MetrixNo ratings yet
- SE512 ProjectDocument23 pagesSE512 ProjectnanokhanNo ratings yet
- SPM Unit-5Document16 pagesSPM Unit-5Nageswara Rao AramandaNo ratings yet
- Software Project Managment: Dr.G.Jose MosesDocument18 pagesSoftware Project Managment: Dr.G.Jose MosesjosemosesNo ratings yet
- Risk Management 5Document10 pagesRisk Management 5ICHHAJAGGINo ratings yet
- UNIT 5 Risk ManagementDocument15 pagesUNIT 5 Risk ManagementhiteshmehtaudemyNo ratings yet
- Risk Assessment Techniques For Software DevelopmentDocument8 pagesRisk Assessment Techniques For Software DevelopmentJayaletchumi MoorthyNo ratings yet
- Project Plan SampleDocument19 pagesProject Plan Sampleapi-533462921No ratings yet
- Project Scope Management: Syllabus For Chapter 4Document10 pagesProject Scope Management: Syllabus For Chapter 4rehan44No ratings yet
- Ias Sbit3l W7sum Vida, John Paul S.Document3 pagesIas Sbit3l W7sum Vida, John Paul S.Vida, John PaulNo ratings yet
- Ims Project Plan-Final 1Document36 pagesIms Project Plan-Final 1api-512644800No ratings yet
- #Assignment AbangDocument5 pages#Assignment AbangNurul SyahirahNo ratings yet
- Event Management ProjectDocument18 pagesEvent Management ProjectSanket Karpe100% (3)
- Project Management MaharishiDocument29 pagesProject Management Maharishiankita choudharyNo ratings yet
- Risk Management Project Lecture NotesDocument5 pagesRisk Management Project Lecture NotestusgNo ratings yet
- Critique On Software Risk ManagementDocument3 pagesCritique On Software Risk ManagementTsing Shi Tao0% (1)
- Oose CHP 2Document18 pagesOose CHP 2Jayaraj JoshiNo ratings yet
- Btec Learner Assessment Submission and DeclarationDocument12 pagesBtec Learner Assessment Submission and DeclarationIslamNo ratings yet
- Unit VDocument24 pagesUnit VPrasad PatilNo ratings yet
- SE Cha 2Document33 pagesSE Cha 2eyobeshete16No ratings yet
- Assignment For SDPM (17 34172 1)Document4 pagesAssignment For SDPM (17 34172 1)Mahmud Ridwan JoyNo ratings yet
- Riks ManagementDocument4 pagesRiks ManagementAkhileshkumar PandeyNo ratings yet
- Chap 2 Software Project ManagementDocument11 pagesChap 2 Software Project ManagementmigadNo ratings yet
- 80 Marks Software Engineering: Fail in A Variety of Ways and Verifies That Recovery Is Properly PerformedDocument9 pages80 Marks Software Engineering: Fail in A Variety of Ways and Verifies That Recovery Is Properly Performedsaurabmi2No ratings yet
- Implementing An Information Technology Project Risk Management Initiative - A Case StudyDocument7 pagesImplementing An Information Technology Project Risk Management Initiative - A Case StudyasifsubhanNo ratings yet
- A Method To Identify and Prioritize Potential Risks of Software Projects Based On C# CodesDocument7 pagesA Method To Identify and Prioritize Potential Risks of Software Projects Based On C# CodeserpublicationNo ratings yet
- Final ExamDocument23 pagesFinal ExamRalphNicholaiApostolUlepNo ratings yet
- Project Management The Challenges and THDocument5 pagesProject Management The Challenges and THRameshk 99No ratings yet
- Term Paper - Risk Management in IT ProjectsDocument26 pagesTerm Paper - Risk Management in IT Projectsankur_saini_17100% (2)
- Risk Management For ICT Project ManagementDocument16 pagesRisk Management For ICT Project Managementimranporasona100% (9)
- research_spm_doc_final1Document7 pagesresearch_spm_doc_final1shahreartonmoyNo ratings yet
- Ylimannela RiskManagementAgileDocument8 pagesYlimannela RiskManagementAgileMarcus CaldevillaNo ratings yet
- Coimbatore Anna UniversityDocument46 pagesCoimbatore Anna UniversityKaarthic EmayNo ratings yet
- Attendance Management SystemDocument6 pagesAttendance Management SystemPramod Theghost RawatNo ratings yet
- 16 MarkDocument2 pages16 MarkjanajohnnyNo ratings yet
- CSTN 142Document8 pagesCSTN 142janajohnnyNo ratings yet
- Attendance Management SystemDocument6 pagesAttendance Management SystemPramod Theghost RawatNo ratings yet
- Billa2 Song ListDocument1 pageBilla2 Song ListjanajohnnyNo ratings yet
- Cricket MiningDocument1 pageCricket MiningjanajohnnyNo ratings yet
- CitiesDocument35 pagesCitiesjanajohnnyNo ratings yet
- Billa2 Song ListDocument1 pageBilla2 Song ListjanajohnnyNo ratings yet
- CitiesDocument35 pagesCitiesjanajohnnyNo ratings yet
- Tell Me Abt UrselfDocument1 pageTell Me Abt UrselfjanajohnnyNo ratings yet
- 3 Phase Induction Motors Objective Questions With AnswersDocument3 pages3 Phase Induction Motors Objective Questions With AnswersMohan Raj0% (2)
- MI MetadataDocument310 pagesMI MetadataMatthew McCreadyNo ratings yet
- Airflex 728 Vinyl Acetate-Ethylene Copolymer Modified With Vinyl ChlorideDocument2 pagesAirflex 728 Vinyl Acetate-Ethylene Copolymer Modified With Vinyl ChlorideNissim Hazar CasanovaNo ratings yet
- GOT2000 - UserManual Monitor - SH 081196 I PDFDocument614 pagesGOT2000 - UserManual Monitor - SH 081196 I PDFFanny Achmad Hindrarta KusumaNo ratings yet
- JDA SCE Standard Release NotesDocument3 pagesJDA SCE Standard Release Notesgolcha_edu532No ratings yet
- Que Dice Ese Gesto Descargar GratisDocument2 pagesQue Dice Ese Gesto Descargar GratisjavierNo ratings yet
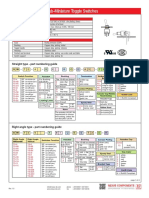
- SW-TS40T Sub-Miniature Toggle SwitchesDocument4 pagesSW-TS40T Sub-Miniature Toggle SwitchesVALTERNo ratings yet
- Guidelines For Planning Childcare Centers & Playground DesignDocument15 pagesGuidelines For Planning Childcare Centers & Playground Design105auco100% (1)
- Odv-065r18ejj-G DS 2-0-3Document1 pageOdv-065r18ejj-G DS 2-0-3Евгений Переверзев0% (1)
- ETN2A ElectromechanicsDocument64 pagesETN2A ElectromechanicsEinstein's VanderbijlparkNo ratings yet
- January2016page1to36 Layout 1Document36 pagesJanuary2016page1to36 Layout 1c737No ratings yet
- CUCM Intracluster Port Usage GuideDocument3 pagesCUCM Intracluster Port Usage GuideAbhinayMylavarapuNo ratings yet
- FGGDocument12 pagesFGGSridharan VenkatNo ratings yet
- Lec 958975Document19 pagesLec 958975Rajasekar PichaimuthuNo ratings yet
- Alketerge EDocument4 pagesAlketerge EYohanes OktavianusNo ratings yet
- Specification for biodiesel (B100) - ASTM D6751-08Document1 pageSpecification for biodiesel (B100) - ASTM D6751-08Alejandra RojasNo ratings yet
- Challenges in PavementsDocument23 pagesChallenges in PavementsSomeshwar Rao ThakkallapallyNo ratings yet
- Huawei EHuawei - Erelay - Solution - OverviewRelay Solution OverviewDocument31 pagesHuawei EHuawei - Erelay - Solution - OverviewRelay Solution Overviewtariq8283% (6)
- TMC 421 PDFDocument82 pagesTMC 421 PDFJamie MooreNo ratings yet
- CV Enric Durany enDocument2 pagesCV Enric Durany enenricduranyNo ratings yet
- 8 Ways To Achieve Efficient Combustion in Marine EnginesDocument10 pages8 Ways To Achieve Efficient Combustion in Marine EnginestomNo ratings yet
- Control Fixed Bed ReactorsDocument4 pagesControl Fixed Bed ReactorsAddison JuttieNo ratings yet
- 2014 Solder Joint ReliabilityDocument18 pages2014 Solder Joint ReliabilitychoprahariNo ratings yet
- J 1 B 1211 CCDDocument3 pagesJ 1 B 1211 CCDRegion 51No ratings yet
- Case Study Cracked Oil Tanks Investigations Web PDFDocument2 pagesCase Study Cracked Oil Tanks Investigations Web PDFyamakunNo ratings yet
- P1 Conservation and Dissipation of Energy Student Book AnswersDocument11 pagesP1 Conservation and Dissipation of Energy Student Book AnswersjoeNo ratings yet
- Chapter 2 Cast IronDocument9 pagesChapter 2 Cast IronHelen AdugnaNo ratings yet
- VDP08 Technical CatalogueDocument47 pagesVDP08 Technical CatalogueAdal VeraNo ratings yet
- Estimating/ Construction Planning/ Scheduling and Programming/ Feasibility Project StudiesDocument4 pagesEstimating/ Construction Planning/ Scheduling and Programming/ Feasibility Project StudiesVholts Villa VitugNo ratings yet