Professional Documents
Culture Documents
IDRC Grant Proposal Aug 2012
Uploaded by
Mária Mijtotianin0 ratings0% found this document useful (0 votes)
14 views64 pagesOriginal Title
IDRC Grant Proposal Aug 2012 (1)
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
14 views64 pagesIDRC Grant Proposal Aug 2012
Uploaded by
Mária MijtotianinCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 64
Privacy International 46 Bedford Row, London, WC1R 4LR, GB
Survelllance and lreedom: global
undersLandlngs and rlghLs
developmenL (SAlLCuA8u)
A research and pollcy engagemenL proposal Lo Lhe lnLernaLlonal uevelopmenL 8esearch
CenLre under Lhe purvlew of rlvacy lnLernaLlonal's rlvacy ln Lhe ueveloplng World
programme.
08
"#$$
Table of Contents
1. RESEARCH PROBLEM AND JUSTIFICATION %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%% &
1.1. Research problem """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" #
1.2. Project context """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" $
1.3. Conceptual framework """"""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" %
2. OBJECTIVES %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%% '
2.1. General objective """"""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" &
2.2. Specific objectives """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" '(
3. METHODOLOGY %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%% ((
3.1. Project organisation """"""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" ''
3.2. Effecting change """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" '#
3.3. Partners thematic priorities """"""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" ')
3.4. Women, minorities and vulnerable groups """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" '*
3.5. The role of Privacy International """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" '*
3.6. Activities """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" '&
3.7. Training and meetings """"""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" +'
3.8. Implementing Partners """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" +'
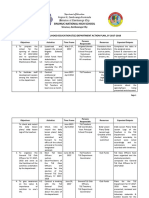
4. PROJECT SCHEDULE %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%% ))
5. RESULTS AND DISSEMINATION %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%% )&
5.1. Results """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" +#
5.2. Outputs and dissemination """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" +$
6. INSTITUTIONS AND PROCESSES %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%% )*
6.1. Privacy International """"""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" +%
6.2. Partner screening """"""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" +*
6.3. Responsiveness to new opportunities """"""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" +*
6.4. Monitoring and evaluation """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" +*
6.5. Risks, prevention and mitigation """"""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" +,
7. PARTNER PROFILES %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%% &(
7.1. Africa Platform for Social Protection, Kenya (APSP) """"""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" #'
7.2. Asociacin por los Derechos Civiles, Argentina """"""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" ##
7.3. Autonomous University of Mexico State, Mexico """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" #$
7.4. Bytes For All, Pakistan """"""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" #%
7.5. Centre for Internet and Society, India """"""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" #*
7.6. Centre for Social Sciences Research, University of Cape Town, South Africa """""""""""""""""""""""""" #&
7.7. Centro de Tecnologia y Sociedad, Universidad San Andres, Argentina, and the Centro de
Tecnologica da Escola de Direito da Fundacao Getulio Vargas, Brasil """""""""""""""""""""""""""""""""""""""""""""""""""""""" $(
7.8. Centre for Cyber Law Studies, University of Padjadjaran Bandung, Indonesia """""""""""""""""""""""""" $'
7.9. Thai Media Policy Center, Chulalongkorn University, Thailand """""""""""""""""""""""""""""""""""""""""""""""""""""""""""" $#
7.10. Derechos Digitales, Chile """"""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" $)
7.11. Dejusticia, Columbia """"""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" $*
7.12. Instituto Nupef, Brazil """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" )(
7.13. Kenyan Ethical and Legal Issues Network, Kenya """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" )+
7.14. Mauritania and Senegal Research Network """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" )#
7.15. Media Institute of Southern Africa (MISA), Namibia """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" ))
7.16. My Computer Law, Thailand """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" )*
7.17. University of Hong Kong, Hong Kong """"""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" ),
7.18. Voices for Interactive Choice and Empowerment, Bangladesh """"""""""""""""""""""""""""""""""""""""""""""""""""""""" %(
7.19. Zimbabwe Human Rights Forum, Zimbabwe """""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""""" %+
1. RESEARCH PROBLEM AND JUSTIFICATION
1.1. Research problem
Privacy International has been working to protect and promote the right to privacy for over 22
years. The need for stronger privacy protections has only increased during that time, and today
more than ever grave challenges to the confines of privacy abound. Technology is developing in
ways and is being deployed in spaces previously unimagined, and we are transforming the ways
we live and communicate. There are fundamental questions about how such technological
change alters our relationships and interactions with governments and the corporate sector. Too
rarely are we given the chance to consider these questions. Instead, as individuals and societies,
we are only offered choices between competing values: our rights and freedoms or security,
modernisation and development; dignity or convenience; freedom or control.
We believe that when societies are given the chance to openly deliberate upon the complexities
of modern policy choices, a richer debate ensues, resulting in more informed policies. The overly
simplified choices between privacy or security must be abandoned in favour of deliberative
policy-making that involves consideration of the necessity of policy change amidst democratic
principles, and proportionality of policy change matched against the legitimacy of our societal
objectives. This is no simple accomplishment and the entire process is fraught with challenges.
It requires a society where rigorous research can generate knowledge that may inform policy,
deliberative political systems that can consider the implications of policy change, and the rule of
law to adjudicate on the value of safeguards.
Nowhere are the challenges to, and opportunities for, privacy protections as dynamic and
complex as in the developing world. As these countries seek new measures to develop their
economies, build social and technological infrastructures, sustain their social systems, and
ensure security they need to consider what are the modern policy frameworks they require to
ensure a just society. The windows around these policy frameworks are key opportunities for
reflection about rights and democratic values, and in the case of this project, the protection of
privacy.
Understanding the complex factors that interact with the right to privacy in developing countries
is an essential first step towards ensuring that privacy remains protected by governments,
respected by corporations and valued by individuals. This project will tackle these challenges
head on. We will ask: what are the threats, challenges and obstacles to, and opportunities
for, the protection of privacy in developing countries?
The mere posing of these questions is a fruitful exercise in its own right. Privacy is simultaneously
a fundamental right that needs continuous protection as technology and societies change, a
political right that is essential to a healthy democratic state, and an economic right that holds
powerful organisations to account. Perhaps most importantly, it is also a policy domain where
we can have discussion about the changes to our societies. This discussion almost always
includes an interrogation of key facets of modern policy making: the constitution of
technological change, the value of economic structures, the effectiveness of accountability
structures, the quality of law, and ethics of changing social norms. Carefully considering these
within debates around privacy and surveillance will inform how we may approach other policy
debates that involve technological, social, legal and economic change.
1.2. Project context
Privacy is internationally recognized as a fundamental right. It has its foundations in the
constitutions of scores of countries, as diverse as Chile,
1
Ethiopia,
2
and Nepal;
3
in numerous
regional and international treaties;
4
and in the jurisprudence of courts across the democratic
world. It plays an essential role in shielding individuals from government and corporate intrusion
into their homes, communications, opinions, beliefs, identities and bodies. Privacy is at the heart
of the most basic understandings of human dignity the ability to make autonomous choices
about our lives and relationships, without outside interference or intimidation, is central to who
we are as human beings.
However, the right to privacy is not a static concept. Its content and confines are subject to
never-ending games of tug-of-war between individuals, governments and corporations.
Understanding how privacy is exhibited within national and cultural contexts, while ensuring the
protection of the core components of the right, is a complex process of negotiation, discussion
and exchange of information. In democratic systems with legal and institutional frameworks in
place, this process of negotiation is an important way of ensuring that privacy protections reflect
and respond to shifts in societal standards, technological advancements, collective practices,
and security concerns. But without representative and transparent processes, there is a real risk
that political, technological or societal changes will be used as a justification to erode the right
to privacy.
This complex process of negotiation is especially fraught in developing countries, where
governments are struggling to manage development, security, growth and modernisation in the
absence of legal systems, physical infrastructure and adequate resources. The conceptual and
practical obstacles to ensuring laws and regulations keep up with rapid technology changes and
expanding capabilities, obstacles that are incredibly difficult in even the most developed
countries, are particularly challenging for emerging economies and democracies. Corruption,
corporate influence, and weak separation of powers all dilute the strength of constitutional and
legal protections, and the immense challenge of addressing terrorism and other domestic and
regional threats in unstable political climates manifests in watered-down safeguards for
individual privacy. Combined with the demands of delivering development aid and public
services, especially in the context of rapid population growth and high unemployment, the
governments of developing countries have their hands full, and privacy is often the first right to
be weakened, threatened or disregarded.
Developing countries are some of the worlds worst privacy violators, spying on their citizens,
conducting extensive communications surveillance, actively censoring the internet and failing to
protect the privacy of personal data and digital communications. Ethnic, religious and other
minorities, human rights organisations and political movements are monitored, obstructed and
persecuted. Such practices not only persistently violate the right to privacy, but also threaten the
enjoyment of other rights and freedoms, including the freedoms of expression, association and
movement, the right to a fair trial and the right to life. In the digital age, surveillance and
censorship are two sides of the same coin in censoring the internet, the state intercepts and
examines private communications, and in conducting surveillance of activities and
communications the state effectively chills free expression and political participation. The dual
1
1981 Constitution, Art 19 (4).
2
1987 Constitution, Art. 26 (1).
3
2007 Constitution, Art. 22.
4
See, for example, the Universal Declaration on Human Rights, Art. 12; the International Covenant on Civil and
Political Rights, Art. 17; the European Convention for the Protection of Human Rights and Fundamental
Freedoms, Art. 8; and the American Convention on Human Rights, Art. 11.
control mechanisms of censorship and surveillance make a full-functioning participatory
democracy impossible.
5
Governments often seek to disguise their surveillance and control agenda by questioning the
cultural relevance of privacy in non-Western countries. Yet Privacy Internationals extensive
research, conducted under the IDRC-funded Privacy in Asia project between 2010 and 2012,
demonstrates that privacy is a right with global currency, one that speaks to individuals the world
over. Privacy is just as important to the developing world as it is to the developed. Citizens of
these countries have simply not had the information, security and political space hallmarks of
open, democratic societies to assert their right to privacy.
This is a pivotal moment for the right to privacy in developing countries and emerging
democracies. While constitutional safeguards may already exist, they remain unaccompanied by
sufficient legislative and regulatory provisions to ensure comprehensive protection of individuals
online and offline privacy. For example, research conducted by our partners in Thailand under
the Privacy in Asia project reveals that, although the 2007 Thai Constitution contains numerous
references to the right to privacy with regard to information, communications and physical
privacy,
6
there is no free-standing law in Thailand on privacy or data protection. Even in those
countries where legislative protections are in place, the lack of institutional frameworks and
functioning accountability processes undermines their enforcement and implementation. For
example, our partners in Bangladesh found that despite the presence of legislative provisions
regulating the lawful access of telecommunications under the Bangladesh Telecommunication
Act 2001, the government continues to conduct illegal wiretaps.
The technical knowledge necessary to design legislative frameworks remains in short supply in
many developing countries. In engaging with governments many of our partners in the Privacy in
Asia project have encountered policy-makers who are ignorant to the implications that domestic
data protection regimes may have for international trade. At the same time, international
regulatory consensus has yet to emerge around issues of data protection, and regional
agreements remain in flux, depriving policy-makers in developing countries of any strong
guidance or best practice upon which to base their own regulatory frameworks. The rapid
expansion of corporate ownership and misuse of personal information, witnessed by our
partners across Asia, is evidence that insufficient attention is being devoted to developing
strong legal frameworks that can keep up with technological advancements and that align with
international standards.
Eradicating long-standing traditions of invasive and widespread state surveillance and unlawful
political intelligence-gathering requires a fundamental change in social attitudes and
considerable improvements in transparency and accountability mechanisms. Research
conducted by our partners on surveillance in China, for example, suggests that communications
surveillance is widespread, despite protections in Chinas criminal and civil laws,
7
and physical
surveillance, particularly of civil society, is rampant. Moreover, the challenge of dismantling
cultures of social control and surveillance is made even more difficult in light of emerging global
trends of expanding surveillance techniques whilst reducing legal safeguards in the name of
national security.
As the right to privacy becomes more and more embattled across the developing world, there is
an increasingly urgent need to educate citizens and policy-makers about the need to fortify legal
5
Gus Hosein, Privacy as a political right, Index on Censorship, Vol. 39, No. 1, 58-68 (2010), available at
https://www.privacyinternational.org/reports/privacy-as-a-political-right
6
2007 Constitution, Arts. 32 to 36.
7
See, for example, Criminal Law, Part I, Chapter IV, Article 252 (1997); Postal Law (1987), Article 4.
protections and develop a regulatory framework, and to eradicate practices that unlawfully and
disproportionately threaten privacy. The capacity of civil society must be built and strengthened
to ensure that governments are held to account, corporate influence is exposed, and citizens are
empowered to claim their rights.
1.3. Conceptual framework
As surveillance techniques are increasingly deployed and new technologies and information
services used in the developing world, there is a pressing need to map out the policy landscape
and the threats to privacy in each country in order to identify the relevant research questions. In
collaboration with our partners, we have isolated those themes and discussions around which
there is perfect storm of advancing surveillance policies and techniques, eroding legal and
technical safeguards (if any existed), and a scarcity of research and understanding (see Fig. 1).
1.3.1. The legal and constitutional landscape
Privacy protections and attitudes towards privacy in developing countries are progressing at
uneven rates, often failing to keep pace with technological advancements, security threats and
changing international standards. In some countries, such as India and Pakistan, governments
are in the earliest stages of considering and drafting privacy legislation, while in others, such as
Brazil and Thailand, new privacy laws are currently under consideration by the legislature. In
Columbia and Argentina, recent jurisprudence has advanced protections from political
intelligence-gathering and abuses in state surveillance. Kenya promulgated a new Constitution in
August 2011, and in Zimbabwe, a new draft Constitution is currently being considered, with a
view to its adoption before the end of 2012. In order to gain a comprehensive understanding of
these changes and their implications for privacy, at the core of Privacy Internationals developing
world agenda is detailed and rigorous research into the laws, regulations, practices and
safeguards relating to privacy, surveillance and human rights. What laws and constitutional
provisions exist to protect privacy, how are they implemented and monitored, and where
are the legal and policy gaps? Collating and analyzing this information at the national level will
enable our partners to better engage in domestic advocacy efforts, provide a valuable resource
for partners in other countries and regions to draw on when designing their own research and
advocacy, and allow us to better map the development of privacy protections across the globe.
For instance, we aim to develop a database of constitutional jurisprudence on privacy, which we
envisage will represent a valuable comparative resource to courts across the developing world
which increasingly look to decisions in Canada, Europe, and the United States as they
adjudicate on comparable cases.
1.3.2. Data protection
The use and misuse of personal data provided by individuals to private and public entities
must be governed by comprehensive data regulation regimes. In many developing countries,
legislative frameworks are either at a nascent stage, or exist but are not implemented or
enforced. In India, China and Indonesia, some of the worlds most populous nations, data
protection regulations simply do not exist at all. Pakistan hosts the worlds largest database of
citizens, but has failed to put in place any safeguards or policies to ensure the security and
fidelity of the data collated. Given the rapid changes in communications, technology and the
exchange and use of data in emerging economies across the world, research is urgently needed
to understand the state of data protection in partner countries, and the local and regional
regulatory standards and best practices. The findings will help to facilitate policy engagement
efforts designed to encourage the adoption, strengthening and implementation of data
protection frameworks. Our partners may work together to identify effective policy solutions
for instance, Argentinas decisions on habeas data may inform cases in the Philippines, and our
Asian partners experience from the Privacy in Asia project may inform our Latin American
partners work on mapping the data protection landscape in their region.
1.3.3. Communications surveillance
Access to and use of communications data is an issue of particular concern in developing
countries, which tend to lack the necessary institutional frameworks, transparency norms and
oversight mechanisms to ensure that the right to privacy is respected. In countries such as
Pakistan and Zimbabwe, lawful access laws are manipulated under the banner of national
security in order to enable widespread communications surveillance arrangements. In
Bangladesh, for example, the establishment of the Bangladesh Computer Security Incident
Response Team, purportedly to monitor communications for the interests of national security,
has in fact enabled the surveillance of political dissidents and human rights defenders. We will
ask: what communications surveillance regimes are in place, how are they designed in
law and how do they operate in practice? This will enable us to uncover surveillance
practices, socialize norms of privacy in communications, and advocate for legislative and
regulatory protections in communications systems. We will also work with global experts in
technology, law, and industry leaders to develop and disseminate global best practices.
1.3.4. Export of surveillance technologies
Privacy International has been at the forefront of uncovering illicit and unethical export practices,
which facilitate the transfer of advanced surveillance technologies from the West to
undemocratic regimes in developing countries. These technologies are also being exported to
developing countries that often lack the appropriate legal frameworks to implement surveillance
techniques within the confines of the rule of law. Our partners have expressed significant
concerns in this trade and are keen to seek transparency in surveillance practices and controls
over their deployment. Where are governments buying surveillance technologies, and how
are they using them? What legal regimes are in place to establish safeguards over the
use of advanced surveillance technologies? What is the state of the art in legal
protections?
1.3.5. Political intelligence oversight
The high levels of autonomy and secrecy in the operation of national intelligence services is
disturbing even in countries with advanced constitutional and human rights protections. In
developing countries, the use of the intelligence services to monitor human rights defenders,
political opponents and other groups of interest to the state can be truly frightening, particularly
in the absence of judicial or legislative oversight mechanisms. They may become threats to
democratic development and the rule of law. In Argentina, for example, the Intelligence
Secretariat reports directly to the President, but is a highly autonomous body, with an oversight
mechanism that operates in secret. We need to ask: what is the nature and operation of local
intelligence services, what oversight mechanisms are in place, and how can these
mechanisms be implemented or enforced?
1.3.6. Politics, identity, sexual and reproductive rights, and social sorting
Under the banners of public security, health, morals and order (and in China, social harmony)
governments are increasingly using personal data and surveillance to categorize and control
citizens and organizations on the basis of the political affiliation, identity or minority status. This
often amounts to a form of social sorting, whereby governments use controls to create and
reinforce social differences and other forms of discrimination, or undermine the enjoyment of
other human rights. For example, personal information derived from the health system may be
illegitimately used to monitor the activities of people living with HIV/AIDs. In Columbia, where the
Inspector General is leading a crusade to monitor pregnancies and illegal abortions, information
kept in health databases might be subject to scrutiny for unintended reasons. In Mexico, it is
believed that data collected for the purpose of providing the Identification Card for Minors is
used for social sorting practices. We need to understand the extent to which governments
misuse personal information to pursue social sorting practices. Our research will help us
identify circumstances in which the collation of data in the name of development, security or
administration has implications for political movements, undermines the protection of sexual and
reproductive rights, and leads to the further entrenchment of social divides.
1.3.7. Delivery of public services
As governments adopt new technologies to meet the challenge of delivering public services to
rapidly growing populations, the right to privacy is increasingly qualified by considerations of
utility and efficiency. Many developing countries are establishing e-health systems, gathering
and digitizing vast amounts of personal, sensitive data about every individual that accesses the
health services, in the absence of sufficient privacy and confidentiality procedures. Social
protection and cash transfer programmes, increasingly popular development tools, are also
designed to collect and share excessive amounts of information with the aid of biometric
technologies; in South Africa, for example, around ten million individuals recipients of social
grants are currently being enrolled in a new biometric system. While these systems and services
bring great advances to the people in these countries, they are also leading to the development
of systems in developing countries that would be illegal in the developed world. What is the
state of privacy protections in public service delivery, particularly those related to e-
health systems and social protection programmes, and how can protections be improved?
1.3.8. ID, DNA and biometrics
Closely related to the delivery of public services, including health services, is the introduction in
most developing countries of identification systems, including ID cards, and centralized, digitized
DNA and biometric databases. There are grave concerns about the security and fidelity of this
information, and the potential for its misuse. In China, for example, the government has set up a
biometric data centre with the stated purpose of maintaining public security, but has allowed an
online commercial enterprise offering biometric data-matching services access to the data.
Thailand has launched a smart ID card that is believed to be the largest integrated circuit chip ID
card project in the world, geared towards the more efficient administration of public services,
while the Mauritanian government is implementing a biometric entry-exit border control system
as part of its security and counter-terrorism strategy. This project will thus ask: what privacy
risks are associated with the collection and use of personal information for ID and
biometric systems? Privacy International and its partners have long been at the forefront of
debates around identity systems in both the developing and developed world, and have fought
to bring attention to the risks posed by some of these systems as they potentially enable
violations ranging from identity theft and fraud to social sorting and persecution. Going forward,
research and advocacy efforts should be extended to new countries and regions where identity
policy is emerging as a key topic of public discourse.
2. OBJECTIVES
2.1. General objective
As countries across Africa, Asia and Latin America accelerate development, address
technological advancements, and secure national borders, the right to privacy is increasingly at
risk. Working with partners in the earlier Privacy in Asia project has given Privacy International an
insight into the fragile state of privacy protections in developing countries, and the complexity of
debates around surveillance, development and security. However, it has also shown us that the
opportunities for research and policy engagement are almost endless. Populations are
increasingly interested in privacy issues, and civil society is eager to understand and engage in
policy-making processes.
The general objective of this project is thus to enhance respect for the right to privacy in
developing countries, by building the capacity of civil society organisations to advance privacy
issues through research, policy engagement and participation in regional and international
dialogues.
Human Rights and
Privacy Laws and Regulations:
Standards and Comparative
Analysis
Data
Protection
ID, DNA and
Biometrics
Delivery of
Public Services
Communications
Surveillance
Export of
Surveillance
Technologies
Political
Intelligence
Oversight
Politics, Identity,
Sexual and
Reproductive
Rights, and Social
Sorting
Figure 1
2.2. Specific objectives
This project will be directed towards building the capacity of and providing expertise and advice
to more than twenty civil society groups across Africa, Asia and Latin America, to advance the
discourse around the right to privacy in the developing world. We will be continuing to
collaborate with many of our Privacy in Asia partners, while also bringing on board an exciting
range of new partners, representing a diverse range of disciplines and drawn from human rights
organisations, academia, activist movements and civil society. We will work with, support and
mentor our partners in their activities, connect them with others working on similar issues, help
them promote their research findings, and work with them to engage in regional and international
human rights mechanisms.
With our partners, we will work towards the following three objectives:
o Objective 1: Generate research and analysis on domestic and regional privacy issues, in
order to identify policy and legislative gaps and obstacles;
o Objective 2: Increase civil society engagement in policy-making in order to advocate for
greater protection and promotion of the right to privacy;
o Objective 3: Engage in national, regional and international governmental bodies to promote
research findings, enhance participation of national and regional stakeholders, and raise
the profile of privacy issues in regional and international fora.
The value of this research is that it will be authentic, timely, and unprecedented.
o Authenticity: This research will bring forward the voices of those who are affected by
surveillance practices, in environments where people are most vulnerable. We will elevate the
stories and the case studies to the international stage where it will inform global policy-
making and innovation.
o Timely: Privacy and surveillance issues are rising on policy agendas in the developing world
even as there is a dearth of research and analysis. Many of the surveillance policies and
techniques studied within this project have never before been subjected to scrutiny. We will
be bringing forward new information at key moments as these policies and systems are being
considered and tested, sometimes for the first time.
o Unprecedented: There has never been a global research programme on privacy and
surveillance for the purpose of informing policy-making. Previous research has been regional,
limited in scope, and almost entirely for academic audiences.
This research programme will develop rigorous and relevant research from contexts previously
unstudied, bringing forth perspectives previously unconsidered, to audiences and institutions
that are now beginning to seek greater understanding on this pressing policy issue.
3. METHODOLOGY
3.1. Project organisation
3.1.1. Partners
This project is designed to create a multi-relational network between Privacy International and
partner organisations and institutions from 17 countries across three regions (Fig. 2).
3.1.2. Spheres of influence
While a key element of this project is the generation of research on privacy in national legal and
policy frameworks, we are also seeking to construct a picture of regional developments and
trends throughout the developing world. To this end, partners research will be both inward- and
outward-looking: the development of local knowledge and understanding will be complemented
by research and engagement at the regional level. This will occur through the use of regional
Asia
VOICE, Bangladesh
University of Hong Kong, Hong
Kong
Centre for Internet and Society,
India
Thai Netizen Network, Thailand
Thai Media Policy Center,
Thailand
Bytes For All, Pakistan
Centre for Cyber Law Studies,
Indonesia
Latin America
Dejusticia, Columbia
Asociacion por los Derechos
Civiles, Argentina
Autonomous University of
Mexico State, Mexico
Centro de Tecnologia y
Sociedad, Universidad San
Andres, Argentina, in
collaboration with the Centro
de Tecnologica da Escola de
Direito da Fundacao Getulio
Vargas, Brasil
Instituto NUPEF, Brazil
Derechos Digitales, Chile
Africa
Zimbabwe Human Rights
Forum, Zimbabwe
Kenyan Ethical and Legal
Issues Network, Kenya
Media Institute of Southern
Africa, Namibia
Jonction, Senegal
Centre for Social Sciences
Research, University of Cape
Town
African Platform for Social
Protection, Kenya
Figure 2 Location of partners
contacts; partners will be encouraged to draw research from, and disseminate research to, their
own local and regional networks and partners. Furthermore, two of our partners in Africa, the
Media Institute for Southern Africa in Namibia and the Africa Platform for Social Protection in
Kenya, are umbrella networks with constituents in over 30 countries across Africa.
As partners exchange and access comparative data, they will be able to produce more nuanced
and informed local research. Privacy International will be able to draw from research to create
regional profiles and contextualise challenges and opportunities encountered by partners. Policy
engagement and advocacy will be facilitated by access to comparative data and experience,
which can act as guidance or leverage to effect political change.
3.1.3. Relationships
Relationships will be built across the following three forms of engagement:
o Between Privacy International and its partners
We have already forged mutually productive relationships with our partners, with whom we
have worked to design this project in order to ensure that it responds to their specific needs
and ambitions, as well as those of Privacy International. Throughout the project we will
supervise, mentor and advise our partners, providing substantive guidance and input where
necessary. We will also raise the profile of their research and stories using our own
dissemination strategies. Partners will report to Privacy International at regular intervals,
detailing successes, challenges, and gaps to be filled. The Privacy International team will
regularly meet with partners, attend partner meetings and workshops, and keep appraised of
partners progress. Privacy International will also conduct evaluation in accordance with the
evaluation framework articulated below (see Section 6.3).
o Between partners working on related themes
Privacy International will facilitate the exchange of research and knowledge between partners
working on the same and related thematic issues. This will be achieved through the
establishment of an online platform to enable inter-partner communications and exchange of
Figure 3 Reach of partner research
research, as well as regular regional and global workshops that will bring partners together to
enable face-to-face discussion and debate. Partners will be able to share information,
discuss the challenges they are facing, seek solutions in their peers experiences and
propose further forms of collaboration.
o Between partners working in the same region
As the right to privacy has currency across, as well as between, national and regional
borders, in conducting their research partners will inevitably find that there are some issues
and challenges that they share with their neighbours. Equally, solutions may be found in
regional collaboration or engagement with regional mechanisms. Accordingly, Privacy
International will facilitate intra-regional communication and collaboration, both online and in
person, and expects to create networks that will outlast the duration of this project. Privacy
International also welcomes the opportunity to work with partners who may introduce us to
regional bodies with whom we are unfamiliar.
3.2. Effecting change
3.2.1. Pathway of change
Building a world where privacy is protected by governments, respected by corporations and
valued by individuals requires local, regional and global policy interventions. At Privacy
International, we see opportunities for change across all levels and in all sectors of policy-
making, whether it be in engaging with local government officials in Bangladesh to improve
lawful access procedures, or in discussing data retention with Google executives in
Mountainview. We seek out and create windows for change with a range of stakeholders, in a
range of settings, with a range of outcomes.
In every instance, however, we believe that effecting policy change starts with ensuring that
policy deliberation is informed by high-quality contextualised research and analysis. Research
that is rigorously conducted, generated, collated and analysed can be instrumental in shaping
and shifting the opinions of policy-makers, guiding policy formulation, and motivating policy
change. Research must also be strategically disseminated, targeted at specific institutions,
processes, or even media. In order to achieve this, research must be conducted in a way that
both engages and informs stakeholders. Research must not only be communicated to policy-
makers upon completion, but the very process of research must engage with those stakeholders
and constituencies who influence policy.
3.2.2. Sites of engagement
In order to effect the change imagined by this project, Privacy International has identified a wide
range of stakeholders with whom to engage and fora in which to intervene. These constituencies
and stakeholders include:
o Regulators, policy-makers, and parliamentarians
Privacy International has extensive experience meeting with regulators in telecommunications
and consumer protection, with senators and MPs; and with civil servants, all of whom want
more information but are not often sure where to get the relevant data. In turn, by engaging
with these stakeholders we can learn from their own experiences, and understand their
informational needs. In particular, we will work closely with the Office of the Privacy
Commissioner of Canada.
o Civil society: consumer groups, human rights groups, and media
Our partners in this project are predominantly drawn from within civil society, but we are also
constantly seeking additional implementing partners. Working in privacy requires identifying
those groups such as those working in consumer protection, human rights or media affairs
for whom privacy is not necessarily a high priority, or where awareness of privacy issues is
quite low. Engaging with these groups often requires considerable dialogue to raise
awareness and draw conceptual links with privacy issues, in addition to more general
capacity-building efforts. We can also learn from the experiences of these groups, so our
engagement methodology focuses on soliciting their views on the pressing policy issues,
technological challenges, the effectiveness of current controls and reviews in their domains,
and their views of the future landscapes.
o Academia and research institutions
Our partners include some of the leading research institutions in their countries and globally.
Other partners will be liaising with their national institutions to promote engagement with
academia through public lectures, seminars, and workshops. The project leaders have
academic research backgrounds and regularly publish in academic journals and make use of
academic literature to inform our work. As with the previous projects, the London School of
Economics and Political Science will be a partner on this project, providing research support
to our partners including assistance with research design and guidance with analysis and
dissemination.
o Industry organizations
Industry is a key source of expertise for understanding the challenges and risks in law,
regulation, and technological innovation, and for foreshadowing future developments. We
will consult with our extensive networks in industry to identify legal risks, the directions of
technological innovations, and how we can best benefit from lessons learned from previous
initiatives. IT, telecommunications, and media companies also tend to have their own
extensive networks, and we will engage with these by utilizing our pre-existing strong
relationships with companies like Facebook, Google, Twitter, and Vodafone. We will also
bring our research to industry by providing them with our partners research these
companies can be made more aware of the operating conditions and effects of their
practices outside of North America and Western Europe.
o Technology and security experts
The importance of epistemic communities in influencing policy through the provision of
knowledge to policy-makers cannot be underestimated. The community of technology
experts are integral to informing public discourse, and essential to diffusing ideas and setting
standards. They can act as the missing link between policy-makers and the often complex
and technical matters they are required to deal with. In many cases they also shape the
development of the technology and capabilities that facilitate or protect against privacy
violations. In this respect, it is vital that Privacy International remains engaged with these
communities; not only can we connect them to partners and policy-makers, we can also
advance our own research and advocacy agenda through such relationships. At Privacy
International, we regularly work with the worlds leading experts on privacy and security. We
solicit their opinions, review their latest research, and involve them in our research processes
as appropriate. We will seek their guidance on pressing policies in our partners' countries,
seek their commentaries for key reports and present their work at our workshops.
o Regional and international institutions and fora
We have worked closely with international bodies, including the UN Refugee Agency
(UNHCR), the UN Special Rapporteurs on Terrorism and Human Rights and Extreme Poverty
and Human Rights, and the Organisation for Economic Cooperation and Development
(OECD). We will consult with our colleagues within these organisations to identify their
understandings of the current and future risks, the directions of innovations in this domain,
and the effectiveness of policy solutions. We will seek to engage in the Universal Periodic
Review (UPR) system of the United Nations Human Rights Council, other treaty-body review
processes, other regional fora such as the Inter-American Commission on Human Rights, the
African Commission on Human and Peoples Rights, and the Commonwealth Secretariat,
and regional regulatory bodies such as the European Union and the forum for Asia-Pacific
Economic Cooperation (APEC).
3.3. Partners thematic priorities
Our research will cover the breadth and depth of the complex themes articulated in Section 1.3
above. Partners in Africa, Asia and Latin America will focus on different elements and
applications of each theme, and regional and global comparisons and summaries produced by
Privacy International will draw the threads together in order to produce a comprehensive map of
the landscape of privacy in the developing world. Each partner will conduct baseline research on
the legal and constitutional frameworks for privacy in their respective countries. This information
will inform Privacy Internationals policy engagement, and will feed into our research
publications, reports, and various advocacy materials (see Section 5.2 Outputs and
Dissemination).
In addition, we have worked with our partners to identify the privacy issues and challenges that
are of particular priority in their respective countries and regions. This has been a participatory
process, whereby partners have been encouraged to choose subjects which are of interest to
their organisation or the wider human rights community, and which they see as giving rise to
pressing concerns related to the protection and promotion of privacy.
Accordingly, in addition to baseline research, partners will pursue thematically-oriented research
projects that fall within one of the seven other themes identified in the conceptual framework
(Fig. 1).
3.3.1. Data protection
In a collaboration between Centro de Tecnologia y Sociedad, Universidad San Andres, and the
Centro de Tecnologica da Escola de Direito da Fundacao Getulio Vargas, partners in Argentina
and Brazil will identify the core issues of the development of data protection laws in Latin
America, conduct a policy analysis of the rational for enacting data protection laws, the
functioning of those laws, and whether there is an impact on the level of data protection in the
region. Derechos Digitales will work on the data protection regime in Chile, and also conduct
outreach and capacity-building workshops with civil society organisations in other Latin
American countries that are not already engaged in the privacy and human rights discourse. The
Thai Netizen Network will look at the online privacy of internet users in Thailand. Our partners in
VOICE in Bangladesh, CIS-India in India, Bytes for All in Pakistan, and the Centre for Cyber
Law Studies in Indonesia will all conduct research on data protection regimes in their respective
countries, with a view towards encouraging the adoption, strengthening and implementation of
data protection laws and regulations. We will also continue our collaboration with our academic
partner at the University of Hong Kong, who is conducting a comparative study of personal data
protection in Greater China, including Mainland China, Hong Kong, Macau and Taiwan.
Privacy Internationals work on international data protection standards is being established at the
Council of Europe, the European Union, the OECD; and we will bring in the expertise of the
Office of the Privacy Commissioner of Canada to provide information on Canadas legal
framework.
3.3.2. Communications surveillance
The surveillance of telecommunications and online communications will be the focus of our
partners at the Media Institute of Southern Africa, a media freedom network with its
headquarters in Namibia and national offices in eleven countries in Southern Africa. The
Zimbabwe Human Rights Forum will undertake research on the use of communications
surveillance in Zimbabwe to monitor human rights defenders and political activists. The Thai
Netizen Network in Thailand and Centre for Cyber Law Studies in Indonesia will also conduct
research on the controls and surveillance techniques utilised by governments in monitoring
online activity. Derechos Digitales will focus on the implications of communications surveillance
for criminal prosecutions in Chile.
3.3.3. Export of surveillance technologies
Our Indian and Pakistani partners, CIS-India and Bytes for All, will conduct research and
advocacy around the technology industry, seeking to understand and raise awareness of the
production of surveillance technologies, which are subsequently employed to facilitate human
rights violations. Our analyses of the legal frameworks around these advanced surveillance
techniques will inform the work of all our partners across these themes.
3.3.4. Political intelligence oversight
The Asociacion por los Derechos Civiles in Argentina will research the use of intelligence
agencies for domestic political surveillance, while the Zimbabwe Human Rights Forum will seek
to understand and expose the web of mechanisms of political intelligence and surveillance in the
Zimbabwean context. Dejusticia in Columbia will conduct a general assessment of the
countrys intelligence law and develop interpretation recommendations.
3.3.5. Politics, identity, sexual and reproductive rights, and social sorting
The complex relationship between the collection of personal information and the use of such
information to achieve discriminatory objectives will be explored by a number of our partners. In
Columbia, Dejusticia will investigate how the misuse of the Inspectorate-Generals powers to
control legal abortion infringes upon womens sexual and reproductive rights. Our partners at
the Autonomous University of Mexico State will research the impact of social sorting practices in
Mexico, while Instituto Nupef will ask whether the adoption of e-health systems in the public
health sector in Brazil threatens the right to privacy amongst already vulnerable populations.
Also working around health systems will be the Kenyan Ethical and Legal Issues Network
(KELIN), which will conduct research and trainings on the right to privacy of people living with
HIV/AIDs in Kenya, while also undertaking a regional survey of privacy protections with respect
to HIV/AIDs in East Africa.
3.3.6. Delivery of public services
Our collaboration with the Centre for Social Sciences Research at the University of Cape Town
in South Africa will yield research on the use of biometric technologies in the administration of
cash transfer programmes in sub-Saharan Africa, with a particular focus on South Africa. Both
KELIN and Instituto Nupef will also look at the privacy implications of the use of technologies in
delivering public services through the health systems of Kenya and Brazil.
3.3.7. ID, DNA and biometrics
Many of our partners have serious concerns about the increased use of biometric technology
and DNA information in databases and identification systems. The Asociacion por los Derechos
Civiles in Argentina and academic partners from the Thai Media Policy Center at Chulalongkorn
University in Thailand and the Centre for Cyber Law Studies in Indonesia will all undertake
research and analysis of ID systems and biometric technologies in their respective countries.
Collaboration between Jonction in Senegal and an academic partner from McMaster University
in Canada will yield research on ID systems and border controls in Senegal and Mauritania.
3.4. Women, minorities and vulnerable groups
Running throughout each of these research areas is a further question of the disproportionate
impact of the erosion of privacy protections on particular groups and communities, especially
women, individuals subject to oppression on the basis of their political affiliation or membership
of an ethnic or sexual minority, and people living with HIV/AIDs. The protections offered by the
right to privacy are essential to protecting members of vulnerable groups who are historically
marginalised, and often persecuted, by government policies. Where those protections are
eroded, members of these groups are the first to suffer.
This project will have a particular focus on the disproportionate impact of privacy violations on
women. Surveillance and censorship particularly disadvantage women, whose voices are already
silenced and marginalised by structural discrimination and traditional patriarchal attitudes that
pervade both developed and developing countries. Privacy violations in health systems are of far
greater consequence to women, whose sexual and reproductive rights are too often under
attack from political and religious forces. The targeting of social protection programmes towards
female heads of households also exposes women to additional privacy violations. This project
will explore and expose these violations.
A second priority for this project is the impact of privacy threats on civil society organisations,
including human rights groups and journalists. The use of surveillance technology to monitor and
control the activities of human rights defenders and journalists not only violates individual rights,
but also stifles public discourse, undermines transparency and accountability, and threatens the
integrity of the democratic state. This project will be geared towards giving human rights
defenders the knowledge and information to protect themselves, and towards supporting
defenders to, in turn, inform the public and engage with policy-makers to effect change.
3.5. The role of Privacy International
3.5.1. Objective 1 Generating research and analysis
We will work with our partners to construct a comprehensive picture of the landscape of privacy
and surveillance laws in their respective countries. Partner projects will examine the systems of
laws and regulations in their respective jurisdictions and produce detailed analyses of the
strengths and gaps. We will help partners reach out to law societies, the judiciary, and other
sources of legal expertise; through alliance-building, these experts can then help partners
promote new safeguards to respond to emerging threats and risks.
As partners develop reports on each country's legal landscape, we will circulate these to our
other partners in other countries and regions to compare and contrast legal protections and
safeguards. These reports will be used as baseline markers to determine the areas that deserve
greater attention and, in turn, to guide further policy engagement. Drawing from our experience
in the Privacy in Asia project, we expect that the answers to the research questions posed will
differ considerably both across and between regions. Furthermore, the existence of laws does
not necessarily mean that there is a regulated system in practice we need data on how
surveillance is conducted on the ground, as well as data on the effectiveness of safeguards. The
results from this research will therefore enable us to construct a nuanced picture of privacy
protections both at a regional and international level, to extract regional and global trends, and
to identify standards that might assist with regional convergence and comparison. Rankings can
be developed and best practices can be proposed as local or regional alternatives.
Privacy International will support partners by providing, where necessary, training on research
skills and techniques, providing guidance with respect to isolating sources of information, and
generally providing support and advice. The project secretariat will also prepare, where
necessary, policy briefs on the issues in which our partners will most likely be engaged. These
include legal briefings on the need for consumer protection of privacy and examples of
regulatory systems, the need for constitutional guidance and key cases and examples of the
constitutional right in practice, communications surveillance safeguards in the modern
communications environment, adequate protections around genetic forensic databases, visual
surveillance policies and practices, critical analyses of identity policies and technologies, and
cases of border and travel security abuses and failures. When these issues arise, we can then
work with our partners to contextualise each briefing for their circumstances, and identify key
audiences and stakeholders for further engagement.
3.5.2. Objective 2 Engagement in policy development
An essential part of effecting change is the effective communication of research outcomes and
the use of such research to engage in the policy-making process. Policy-makers come to the
most equitable decisions when they are equipped with useful and accessible research. Too often
they lack in-depth analyses of the technological developments and likely development paths,
knowledge of experiences to date elsewhere, analyses of policy and technology limitations, and
useful assessments of the arising risks. This project will focus on using research to fill the gaps in
knowledge and to advance the policy discourse around privacy and surveillance.
The thrust of our work towards achieving this objective will be devoted towards building the
capacity of partners to engage effectively with national actors and stakeholders, conduct
consultations, and raise awareness of privacy issues. We will encourage partners to reach out to
local experts and national organisations, and to work with local academic institutions,
particularly when organising workshops and events. Privacy International staff will attend and
participate in partner meetings and workshops in order to share expertise, support partners, and
stay engaged in the national developments.
3.5.3. Objective 3 Promotion of research findings, enhanced participation, and
raising the profile of privacy issues
Just as threats to privacy can rarely be contained by borders, so too are the solutions to privacy
challenges often found in regional and international initiatives, regulatory frameworks, and legal
mechanisms. It is vital that the results of domestic research be shared both within and between
regional groupings, to enable partners from learn from the mistakes and achievements of other
jurisdictions. We will connect our partners from the developing world with experts and
lawmakers in jurisdictions with more advanced privacy protections. We will build networks of
privacy advocates and experts, enhancing their capacity to tackle privacy issues, building their
research skills and capital, and expanding their advocacy opportunities.
A central aim of this project is to raise the profile of privacy issues in regional and international
human rights fora, which have traditionally shied away from addressing the right to privacy in any
detail, particularly its implications for industry and the responsibilities of corporations. Human
rights advocates and experts have approached the issue of online privacy tentatively, although
the recent United Nations Human Rights Council resolution recognising internet freedom as a
basic human right
8
shows the increased willingness of countries to recognise that human rights
exist online, as well as offline. Privacy advocates must seize this opportunity to bring privacy to
the forefront of human rights discourses at regional and international human rights mechanisms,
particularly the Human Rights Councils Universal Periodic Review. We will employ our expertise
in engaging with UN human rights mechanisms to help our partners prepare submissions to the
8
A/HRC/20/L.13.
UPR and engage in shadow reporting for treaty-body processes, as well as to seek out other
opportunities to bring privacy into the human rights agenda.
We cannot ignore the importance of engaging with industry and technology companies in
improving data protection standards, and accordingly we will continue to pursue our
longstanding relationship with technology and internet leaders such as Google and Facebook,
making sure our partners research and objectives are received and taken on board. It is also
vital that we engage with the regulatory frameworks around privacy and data protection. In this
respect, we will ensure our research and policy objectives are brought to intergovernmental
bodies such as the Organisation for Economic Cooperation and Development (OECD), the
European Union and APEC, and that privacy is a key part of the agenda in those forums.
3.6. Activities
Privacy International will work with our partners to conduct six types of activity in order to
achieve the project objectives: desk research; field research and surveys; policy briefings,
reports and submissions; workshops and trainings; legal and policy engagement; and advocacy
and media engagement. One or more of these activities will be employed to achieve our specific
objectives (Table 1).
3.6.1. Desk research
Partners, many of whom are lawyers or have background in legal studies or the field of
information and communication technologies, will collate and study laws, regulations, policy
documents, implementation guidelines, jurisprudence and judicial opinions, parliamentary
transcripts, executive memos and research papers, reports of independent commissions and
bodies, and media reports, in order to:
o Document constitutional and statutory provisions;
o Research key court cases on privacy issues;
o Develop an understanding of structural challenges to access to justice;
o Review the strength of legal protections within the country in other domains, such as the
strength of regulators; and
o Assess the challenges to petitioning for legislative and policy changes.
Table 1 Activities and objectives
Objective
Desk
research
Field
research
&
surveys
Policy
briefings,
reports &
submissions
Workshops
& trainings
Legal and
policy
engagement
Advocacy &
media
engagement
1. Generating
research and
analysis
2. Engagement
in policy-making
3. Promoting
research
findings,
enhancing
participation,
and raising the
profile of privacy
issues
3.6.2. Field research and surveys
In order to ensure that research conducted is comprehensive, partners will also reach out to law
societies, the judiciary, and other sources of legal expertise in order to verify or complement their
desk research. Where necessary, qualitative and quantitative research into, inter alia, health
systems, social protection programmes, identification projects, and development programmes
will also be undertaken. Perception polling and surveys will also be conducted and data analysed
and classified with adequate data analysis software.
3.6.3. Policy briefings, reports and submissions
Privacy International sees great importance in publishing research and results in multiple formats
across multiple forums. Publication of research increases the likelihood of research significantly
influencing policy dialogues and informing the public discourse. It also opens the research up to
rigorous critique and debate. The results of partners research will be published in different
venues, including as blog posts, op-eds, policy briefings, fact sheets, reports, submissions to
national, regional and international mechanisms, as well as in multiple languages, where possible
(see Section 5.2 Outputs and Dissemination). Privacy International will facilitate the
publication and dissemination of partner materials and research primarily through our website,
and will also synthesise and collate materials across research themes and regions to create
compilations and comprehensive studies.
3.6.4. Workshops and trainings
Research must not only be communicated widely upon completion but the very process of
research must involve engaging with various constituencies and stakeholders. Both in the course
of conducting research, and in order to disseminate research findings, workshops and trainings
will be held at the national, regional and global levels. Initial training sessions will be held to build
the capacity of advocates and researchers. Workshops will bring together experts, academics
and practitioners to seek input into research design and methodology, canvass ideas, and learn
from experiences. Once research is generated, training sessions and educational workshops will
be held to disseminate research findings, seek review and input, and advocate for policy
changes.
By conducting workshops and trainings, partners will ensure that research is informed by
stakeholders experiences, but also that they feel that they are part of the research process, and
are therefore vested in the research output.
3.6.5. Legal and policy engagement
In order to effect change, research must be effectively communicated to policy-makers through
strong, targeted policy engagement initiatives. Partners will meet with regulators, policy-makers
and parliamentarians to communicate research results and agitate for change. Research will be
disseminated in third-party stakeholder forums and civil society consultations, and will be
brought into regional and international human rights forums where possible. In particular, we will
seek to engage in the UPR system of the United Nations Human Rights Council, which presents
a unique and high profile opportunity to get privacy on the international agenda. We will engage
with regional bodies working on privacy regulatory frameworks, such as the European Union and
APEC. We will also consider instituting strategic litigation at the national and regional levels in
order to engage the judicial system in enforcing political changes.
3.6.6. Advocacy and media engagement
Perhaps the most effective way to influence the public discourse and, in turn, policy debates is
through the effective use of the media. We will seek and maximise media exposure, and use
media and other public platforms to publicise research and call for policy changes. Other
advocacy opportunities in which Privacy International and its partners will engage include
conferences and meetings on privacy-related issues, the UPR and other treaty-body review
processes, and other regional fora such as the Inter-American Commission on Human Rights, the
African Commission on Human and Peoples Rights, and the Commonwealth Secretariat. We will
also engage with ASEAN as it moves forward in establishing a human rights mechanism.
A large part of Privacy Internationals expertise lies in engaging the technology industry, and in
this regard we will work to ensure that partners have an opportunity to enter into dialogue with
relevant stakeholders.
3.7. Training and meetings
Privacy International will provide our partners with the necessary training to ensure that they have
the skills, expertise and knowledge to conduct their research and engage successfully with
institutions and policy-makers. We will provide training as necessary and upon request. Our
partners in Asia, most of whom worked with us on the Privacy in Asia project, by now possess all
the requisite skills and knowledge to undertake this work, but we anticipate that our partners in
Latin America and Africa, having had less engagement with privacy issues previously, will have a
greater need for training on privacy and surveillance issues. We therefore anticipate that two
regional skills training sessions will be held in the first year of the project.
Privacy International will also hold yearly global meetings to bring together all partners in the
project to facilitate the exchange of information, ideas and experiences. This will be a powerful
networking tool for partners, while allowing Privacy International to stay engaged in partners
research and advocacy efforts.
3.8. Implementing Partners
In addition to working with our project partners, Privacy International will also work with two
implementing partners, namely the Office of the Privacy Commissioner, Canada, and the London
School of Economics in the United Kingdom.
3.8.1. Office of the Privacy Commissioner, Canada
Privacy International has formed an institutional relationship with the Office of the Privacy
Commissioner of Canada (OPC) to promote global privacy protections. We are currently
working on a shared programme to engage with the Commonwealth Secretariat and La
Francophonie, two significant intergovernmental bodies operating in the developing world. The
OPC will continue to collaborate with Privacy International on this project, by participating in the
yearly workshops, and will also intervene in the project when partners request expert advice,
assistance or input. The OPC's experience in privacy and data protection will help guide our
partners. Access to the OPCs analytical frameworks, such as their reference documents on
analysing privacy in relation to national security and public safety,
9
and to their evaluation and
communications frameworks, such as the OPCs frameworks for Privacy Impact Assessments,
10
will help our partners develop their own approaches to the complex policy challenges they will
face. Finally, our partners will provide research and information that is relevant to the OPC's
strategic priority to advance global protections for Canadians,
11
in particular as the OPC
9
Statement by Jennifer Stoddart, Privacy Commissioner of Canada before the House of Commons Standing
Committee on Access to Information, Privacy and Ethics on Main Estimates 2009-2010, May 25, 2009, Ottawa,
Ontario. http://www.priv.gc.ca/parl/2009/parl_090525_e.asp.
10
A Matter of Trust: Integrating Privacy and Public Safety in the 21st Century, A Reference Document from the
Office of the Privacy Commissioner of Canada, November 2010, available in Spanish, French, and English at
http://www.priv.gc.ca/information/pub/gd_sec_201011_e.asp.
11
Expectations: A Guide for Submitting Privacy Impact Assessments to the Office of the Privacy Commissioner
of Canada, March 2011, available at http://www.priv.gc.ca/information/pub/gd_exp_201103_e.asp.
continues its work in regional and international fora.
3.8.2. The London School of Economics, United Kingdom
Privacy International has a long-standing relationship with the London School of Economics and
Political Science (LSE), and they will continue to be our partner throughout this project. The LSE
will provide research guidance, technical assistance to partners as requested, and input into
Privacy Internationals briefings and reports. We will use the networks of the LSE to establish
links with national academics and researchers to help disseminate our shared findings. The LSE
will enable relationships within the international academic community. For instance, the LSE has
co-hosted workshops in our partners countries with local universities in order to raise the profile
of the events, and to ensure the political neutrality of the audience and participants.
4. PROJECT SCHEDULE
The project will be conducted over a two-year period. In general terms, the first year of the
project will be dedicated to achieving Objective 1. Partners will conduct desk research, field
research and surveys, and begin to translate the results of their research into policy briefings,
reports and submissions. In the last quarter of the first year, and leading into the second year,
partners will address their work towards Objectives 2 and 3. Legal and policy engagement,
advocacy and media engagement will continue throughout the rest of the project. Partners will
identify opportunities for engagement at the regional and international level, and translate their
research into reports and submission that can inform policy making in difference forums.
Privacy Internationals role in managing the project will vary throughout the life of the project. At
the start of the first year we will hold skills trainings for partners in Latin America and Africa.
Midway through the first year and at the start of the second, we will coordinate regional or
thematic meetings to bring together partners and facilitate the sharing of research and
experiences. At the end of the project we will hold a global meeting in order to consolidate
networks, share lessons learned, and plan future collaborations. Narrative and financial reports
will be required from partners at regular intervals throughout the project.
Table 2 Schedule of deliverables
Deliverable Year 1 Year 2
1 2 3 4 5 6 7 8 9 10 11 12 1 2 3 4 5 6 7 8 9 10 11 12
Objective 1 Generating research and analysis
Desk
research
Field
research and
surveys
Policy
briefings,
reports and
submissions
Workshops
and trainings
Objective 2 Engagement in policy-making
Policy
briefings,
reports and
submissions
5. RESULTS AND DISSEMINATION
5.1. Results
Privacy International believes that when rigorous research is properly targeted, it can play an
essential role in policy change. In the domain of privacy and surveillance, research is perhaps
even more important, as the act of surveillance and abuse of personal information is difficult to
observe, and the arising harms are often experienced in indirect ways. For example, we do not
easily see communications being unlawfully monitored, the abuse is exhibited in the form of
detention and prosecution for political crimes using intelligence from those communications; we
do not easily see how companies misuse personal information, keep inaccurate records, and
shares it with other parties, the abuse is exhibited as poor credit scoring, discrimination in the
marketplace, and stolen identities. Research that brings these dynamics to the fore in order to
identify risks, increase awareness of abuses, highlight best practices, and inform stakeholders is
essential.
Research is the foundation of Privacy Internationals advocacy strategy. Our research is not
conducted in a vacuum; we believe that all research must be designed in ways that engages
with, responds to and informs public and policy processes. The research that Privacy
International and our partners will conduct will thus be designed to have a concrete impact upon
policy-making and political discourse. As an example, when we began our work with CIS in India
in 2008, many people were sceptical that privacy would ever become an issue in the Indian
public discourse. Four years later, in part due to the research conducted by CIS and their efforts
Workshops
and trainings
Legal and
policy
engagement
Advocacy
and media
Objective 3 Promotion, participation, profile
Policy
briefings,
reports and
submissions
Legal and
policy
engagement
Advocacy
and media
Project management
Regional
meeting
Global
meeting
Interim
narrative
report
Interim
financial
report
Final
reporting
to bring together key stakeholders, raise awareness in the media, and strategically disseminate
their work alongside the governments own policy agenda, privacy has become a key issue in
India, leading to significant policy initiatives.
We firmly believe that the research and policy engagement that we produce in the course of this
project will be instrumental in driving change and raising the profile of privacy issues in political
and public discourses across the developing world. Our outputs and means of dissemination will
reflect this objective.
5.2. Outputs and dissemination
Privacy International and its partners will produce a range of different outputs and disseminate
their research through a variety of different means. Research outputs will be designed by
partners, in collaboration with Privacy International, after contemplation of the research
objectives, and will be chosen after careful consideration of the political and societal contexts
and constraints.
All of our partners will produce research papers and reports of varying lengths, which will be
utilised as outputs in themselves (and printed or otherwise disseminated as necessary) and
which will also serve as the basis for some of Privacy Internationals advocacy and engagement
activities. In particular, research produced by our partners will feed into Privacy Internationals
Global Surveillance Monitor, a global catalogue of privacy laws and practices. We will also
produce thematic reports that draw threads and identify trends across and between regions.
Privacy International will also draw from these research papers and reports to design a
curriculum for Privacy 101, an online privacy course. At the outset, the resource will be adaptable
content for our partners to use on their own websites and initial briefings: modules such as
About Privacy or About Privacy and ID Cards will immediately give partners websites some
detailed information about privacy and surveillance issues. Over time the content will become
more relevant to their contexts, including key case studies and analyses of local policies.
Eventually there will be sufficient information at local, regional, and international levels to create
an online educational curriculum. As we integrate academic material and other key case studies
from the university course that we taught at the London School of Economics and Political
Science for more than 10 years, we envisage this course becoming an accessible resource not
only for our partners and their constituencies, but for students and professionals with interests in
surveillance and human rights issues. In the later stages, it will incorporate cases from our
partners research, and eventually be translated into the relevant languages and for various
audiences. Ultimately, we hope that Privacy 101 will become a recognised course for which
university students or professionals can gain accreditation. By ensuring that research and
analysis generated by our partners feeds into the design of Privacy 101, Privacy International will
create a curriculum that reflects the whole spectrum of privacy challenges and experiences from
across the developed and developing world.
In addition to these outputs, partners will disseminate their research and analysis through a
variety of different means, including:
5.2.1. Blog posts and websites
Blog posts on our website will be employed as a form of dissemination for all of our partners,
particularly those from Argentina, Brazil and Pakistan who have explicitly identified blogging as
an effective means of engagement. ADC, one of our partners in Argentina, will establish a
website especially to present information gathered and research generated under the project. All
of our partners will be advised on how to create and sustain privacy-relevant content on their
websites if they identify that this is relevant to their communications strategies.
5.2.2. Documentary film production
Our partner in Thailand has identified this as an effective means of disseminating their
research.
5.2.3. Newsletters, booklets, and leaflets
Our partners in Bangladesh will produce a range of short written publications for public
dissemination.
5.2.4. Opinion pieces
Many of our partners have identified media exposure, particularly through opinion pieces, as an
important means of disseminating research results. Accordingly, partners from Columbia, India,
Argentina and Brazil, Pakistan, Bangladesh and Namibia will seek to have their research and
analysis published in the form of opinion pieces in local media.
5.2.5. Policy and implementation guides
Our partner in Columbia will produce an online methodological implementation guide of the
countrys new Transparency and Accessibility to Public Information Law (2012), while our partner
in India will produce sectoral policy guides for use by policy-makers. Privacy International will
support all members in their policy domains by drafting generic policy briefings that our partners
can then adapt to their own purposes, e.g. for government consultation processes, media
briefings, etc.
5.2.6. Stakeholder forums and conferences
All our partners are using workshops, conferences, and round-tables as a means to conduct their
research and to disseminate their initial and final findings. These meetings create opportunities
to consult widely, solidify old relationships and move them into new domains, create new
networks by bringing in new partners and institutions, enfranchise participants to the outcomes
as they become part of the research process, disseminate results, and create momentum around
further work in the domain.
5.2.7. Strategic litigation
Our partner in Columbia will contemplate participating in strategic litigation under the countrys
habeas data law (1266 of 2008) with respect to exceptions to access to public information. Our
partner in Kenya also regularly participants in strategic litigation in the context of privacy in the
health system and will consider doing the same under the ambit of this project.
5.2.8. TV/radio debates
Partners in Columbia and Bangladesh have identified the importance of radio and TV debates
for informing public and political discourses.
5.2.9. Workshops and trainings
One of our partners in Thailand will hold a workshop for activists and human rights defenders,
while our Chilean partner will hold a capacity building workshop for civil society organisations in
those Latin American countries with weaker privacy discourses. Partners in Zimbabwe and
Namibia will provide training to their respective network members while partners in Kenya will
train local health practitioners about privacy issues in the context of HIV/AIDs.
6. INSTITUTIONS AND PROCESSES
6.1. Privacy International
The implementation of the project will be coordinated by the Project Director and supervised by
the Executive Director, both based at Privacy International in London, and will be supported by
a Researcher. The Project Director will oversee and advise on the design and delivery of all
partner initiatives through the revision of quarterly partner reports. She will also monitor spending
and advise on changes of funding needs through the revision of partner reports. The Project
Director will work under the supervision of the Executive Director, who will provide technical and
substantive guidance, and assess problems and mitigate risks where necessary. The Project
Director and Executive Director will collaborate to ensure harmonious working relationship and
clear lines of responsibilities for delivery of project outputs, communicate regularly with partners
and the IDRC to report on project progress, and ensure that deliverables are met in a timely
manner.
Privacy Internationals engagement with international regulatory regimes will be conducted by
the International Liaison, based in Australia, who will continue work commenced under the
Privacy in Asia project and represent Privacy International and its partners at regional fora and
consultations in the Asia-Pacific region.
The Project Director and Researcher will be assisted by Privacy Internationals international
Advisory Board, which includes over a hundred experts in the field of privacy and technology
and scholars, industry practitioners, and activists with knowledge of specific regional challenges
encountered by our partners. The main role of the Board will be to provide guidance on
implementation strategies, new developments, and to assist with dissemination.
6.1.1. Personnel
Dr Gus Hosein (Executive Director) is the Executive Director of Privacy International. He has
held academic posts at the London School of Economics and Political Science, Columbia
University, and the American Civil Liberties Union. He regularly advises international,
governmental, non-governmental, and private sector organisations on governance, civil liberties,
and technology policy. Most recently, he advised the United Nations High Commissioner for
Refugees and the UN Special Rapporteur on Terrorism and Human Rights. He is a Fellow of the
Royal Society for the encouragement of Arts, Manufactures and Commerce (FRSA). He has a
B.Math (Hons) from the University of Waterloo, and a PhD in technology regulation from the
University of London.
Carly Nyst (Project Director) is Head of International Advocacy at Privacy International. She is
an Australian-qualified human rights lawyer who previously worked as Legal Adviser to the
United Nations Special Rapporteur on Extreme Poverty and Human Rights, and was a Fellow at
the Columbia University Law Schools Human Rights Institute. In addition to experience
practicing in criminal and administrative law, Carly has worked at human rights organisations
such as the International Council on Human Rights Policy and the International Bar Associations
Human Rights Institute. She has written and published on a diverse range of human rights-related
issues, from security to development, and was the author of the Australian edition of Amnesty
Internationals No Safe Haven study of universal jurisdiction laws. She holds an LLB/BA
(International Relations) (Hons) from the University of Queensland, a Grad Dip. (Legal Practice)
from the College of Law and an MSc (International Relations) (Hons) from the London School of
Economics.
Nigel Waters (International Liaison) is a Privacy International Fellow and a Board member of
the Australia Privacy Foundation. He has had 25 years experience in privacy protection, as a
regulator (in the UK and as Deputy Australian Federal Privacy Commissioner from 1999- 2007),
consultant, academic (at the University of New South Wales) and activist. Nigel has represented
Privacy International at meetings of the APEC Data Privacy Sub-group since 2006, and is co-
author of the draft Asia-Pacific Privacy Charter.
6.2. Partner screening
We have already worked with a large number of our partners in the course of the Privacy in Asia
project. Many of our other partners, particularly those from Latin America, attended a workshop
we held in London in June 2012, and participated in the debate and discussion that formed the
conceptual foundations for this project design. The remainder of our partners were identified
through a scoping exercise that we conducted by utilising existing networks and contacts as
references.
In preparing this project, we have asked our partners to provide us with extensive information
about their organisation and personnel, methodology and research design, outputs, proposed
dissemination and engagement objectives, perceived risks and limitations, envisaged monitoring
and evaluation responsibilities, good governance and accountability frameworks, political
independence, and equal opportunities practices. While we are satisfied with the results from
this process, we will continue to work with each partner to ensure that their work meets the
highest professional, ethical and legal standards.
Furthermore, given the close nature of our relationships with our partners and the constant
contact we maintain with each of them, we are confident in our ability to ensure that partners
have the institutional support necessary to continue meet these highest standards. For all
partners that we have not previously worked with, we will be undertaking an early-stage visit to
their offices, to meet with staff and trustees, meet with their local partners, and if possible and
appropriate, meet with government and industry officials (whenever relevant to their work).
6.3. Responsiveness to new opportunities
Privacy International acknowledges that as the privacy and surveillance landscape continues to
change in the light of technological advancements and local, regional and global developments,
new opportunities may arise to engage with new and different partners in the developing world.
We have designed this project with this possibility in mind; that our financial and technical
capacities may need to stretch to include as-yet unidentified partners and projects, where
engagement with such partners might present a unique and valuable opportunity to maximise
policy and research windows.
6.4. Monitoring and evaluation
Privacy International accords great importance to ensuring that the activities of our partners are
of the highest quality and integrity. As a registered UK charity, we have obligations under charity
law to ensure that all of our work is consistent with our charitable purpose under UK law, that we
are not party political in our work, and that there is an evaluation framework for how we take up
issues and the evidential foundation for our work. In turn, we must ensure that the work of our
partners meets these same standards. We believe that these standards represent good practice,
and we are keen to help our partners develop themselves into sustainable organisations with
clear goals and processes.
We will pursue monitoring and adopt an evaluation framework that provides a continuous point
of reference to enable oversight and management. We will monitor all the projects against the
objectives, outcomes, activities and outputs specified in the partner proposals in Section 7
below. We will also require regular reporting in accordance with the Schedule of Deliverables
articulated in Section 4 above. Further payments on the project will only occur once reporting of
the previous period is complete.
We will also evaluate partners research and advocacy activities to facilitate improvement,
ensure that partners have the support and guidance they require, and increase the effectiveness
and relevance of partners activities. For each partner, evaluation will be conducted in a manner
and at time that is responsive to partners needs and respectful of their constraints, and will be a
participatory process that should facilitate the sharing of knowledge, experience and theory.
In conducting evaluation we will employ the following framework to ensure that the projects
objectives are being met:
Table 4 Evaluation framework
Baseline Extended Advanced
Objective 1:
Generating
research and
analysis
High-quality,
contextualised research
and analysis is produced
Research and analysis is
challenged and improved
through stakeholder
engagement
Research and analysis
influences national and
international research
agendas
Objective 2:
Engagement in
policy-making
Policy-makers and
stakeholders are
engaged by research and
analysis
Policy choices and
dialogues are informed
by research and analysis
Policy change reflects
outcomes of research
and analysis
Objective 3:
Promoting research
findings, enhancing
participation, and
raising the profile of
privacy issues
Research and analysis
penetrates new
dialogues and fora
New dialogues and fora
engage with and
prioritise research and
analysis
Research and analysis
impacts upon new
dialogues and fora
Privacy International will be undergoing an external evaluation in Q2 of 2014 as part of a
separate grant process, and will incorporate a review of our international programme
management as a part of that review.
6.5. Risks, prevention and mitigation
There are risks in running a project of this complexity and magnitude. Below we identify some of
the foreseeable risks and identify how we are planning to prevent these risks from damaging the
outcome of the project. Not all of these risks can be prevented through planning, however, and
we identify methods for minimising or mitigating these risks when they arise throughout the
project period.
Table 5 Research risks
Risks Prevention Mitigation
Weak research PI assist in reviewing partner research Require well articulate and
methodology. plans prior to the commencement of
research.
planned research strategies that
will be published openly in the
final reports from each partner.
Results do not match
expectations
PI will ensure that research objectives
are not overly normative or predictive,
but rather identify issues of interest
worthy of study.
Allow research objectives to
change over time as the project
objectives may too change due
to environmental changes.
Research results do not
gain traction.
PI will help identify academic and
non-academic venues for the
research results at an early stage.
Well-designed and well-
presented research with clear
policy implications will appeal to
international media and other
networks. Research can also be
presented to PIs networks to
gain traction.
Partners are placed at risk
due to the nature of their
research projects, or
because of travel and
security risks.
Budget for increased security costs
for workshop meetings. Work closely
with our partners to show that they
have international support for their
research. PI staff will be trained in
first aid, and we will incorporate
security and health and safety into
our project planning.
PI will seek security advice on
issues in each country. We will
monitor security updates
regarding travel, and ensure
travel insurance for all
international travel.
Table 6 Capacity-building risks
Risks Prevention Mitigation
Unable to create broad
networks.
We will expect all our
partners to establish a clear
strategy for establishing their
networks, and we will review
this strategy to ensure that
they have reached across all
sectors.
If problems arise, PI will use our
global and industry partners, and
global partners to identify
stakeholders with whom our partners
may engage.
Failure to capture attention of
key stakeholders.
PI will work closely with
partners to help prepare their
research announcements,
and develop strategies for
dissemination. We will
continue to run engagement
strategies-trainings sessions.
PI has a strong tradition of raising the
media profile of issues, and will share
our expertise and engage our own
networks to ensure that even in those
countries where penetration is low,
media exposure is maximized.
Lack of adequate knowledge of
issues to build capacity.
Privacy issues require a high
level of expertise. To support
our partners we have and will
continue to run workshops
on privacy issues and
develop resources that cover
issues on their policy
agendas.
To support our partners, we will link
them with international experts on
pressing issues, and provide back-
office support on policy analyses. We
will also promote inter-partner
support.
Table 7 Project implementation risks
Risks Prevention Mitigation
Partners staffing and financial
constraints change.
We will develop contractual
statements between our partners
We will generate virtual training
materials for partners to use to
and PI to ensure that regardless
of changes in organizational
staffing, the expected outputs
remain the same, allowing some
room for accommodation of
constraints.
train their staff on pressing
issues. We will require quarterly
updates on project and
organizational status to consider
if changes to project outputs are
required.
Partner repeatedly fails to
respond.
Contractual agreement between
the partner an PI will ensure that
funding is disbursed only upon
review of project work at critical
stages.
PI will reserve the right to
suspend payments. We will also
seek the advice of IDRC if this
becomes a problem. We will
ensure that the failure of a
partner will not result in the
failure of the project.
Timelines begin to slip across
the project.
Clear planning, when possible,
will prevent major failures in the
timeline.
Regular reporting to IDRC on the
progress made, and any
changes that may need to be
made to the expected
outcomes, with a clear rationale
for such changes.
PI team encounters planning
problems.
Establish clear plan for the full
duration of the project, in
negotiation with partners and
their needs.
Regular report to IDRC to
identify problems and seek
advice on resolution.
Table 8 Risks in project management
Risks Prevention Mitigation
PI team becomes overwhelmed
with demands of partners
Ensure project is adequately
staffed. Planned quarterly
discussions will ensure partners
are given continual attention. PI
will connect partners with
experts where necessary to
relieve the burden on the project
secretariat.
Seek assistance from IDRC to
guide research and engagement
strategy. Explain to partners that
the projects are led by them and
only coordinated with PI as
support, not leaders on each
project.
Administrative load of funds
management becomes
burdensome.
Partner screening, monitoring
and evaluation will ensure that
partners have sufficient
processes in place to ensure
funds are well-managed.
We will keep a reserve fund
aside for pressing and
unforeseen situations and new
partners, and will also consider
disbursing funds from this where
required for account
management.
Exchange rates fluctuate
affecting amount of funding.
Contractual agreement with
partners establishes that
partners bear the responsibility
of currency fluctuations, and
should budget and plan
accordingly.
If changes are relatively
consistent across all currencies,
then maintain proportional
funding for each project.
Problems in staff management
within PI.
Enforce monthly reporting of
activities within PI and match
against goals set out at the start
of each month. Share
communications with IDRC and
partners to ensure transparency
and accountability.
Hold regular meetings of PI staff
and advisors to ensure that all
the propose work is being
accomplished, reallocate
staffing as required.
7. PARTNER PROFILES
7.1. Africa Platform for Social Protection, Kenya (APSP)
http://www.africacsp.org/
7.1.1. Organisational overview
The APSP is a network of civil society organisations from across Africa that was established as a
response to the growing demand for a representative voice and more active engagement of
African civil society in the shaping of social protection policies, programmes and practices. It is a
network of organisations operating at national and regional levels, committed to promoting and
strengthening the social contract between states and citizens. APSP has so far supported the
establishment of National Civil Society Platforms in 30 countries. Members of national platforms
are typically national CSOs and social movements and the local offices of international NGOs.
7.1.2. Personnel
The APSP has six qualified and professional social protection specialists with extensive
knowledge and experience in social development and human rights who will work on this project.
In addition, the APSP will work with its network of platforms across the continent.
7.1.3. Project summary
Social protection is emerging as an important mechanism for poverty reduction in Africa. Since
2004, Africa has seen an increase in the number of social protection policies and programmes
being developed in nearly 40 countries on the continent. The continent is also witnessing
innovation in terms of mechanisms to manage the social protection transfers. These transfers
require substantial amounts of personal information to be gathered from potential beneficiaries
for purposes of identifying and reaching the poorest and the vulnerable. However, most of these
countries lack adequate systems, policies and legislation to protect the rights of beneficiaries
with regards to privacy of personal information. Consequently, little is known about how the
information gathered is collected, stored, accessed and used. Unfortunately this opens the
possibilities of abuse and misuse of the information gathered and violates the rights of
beneficiaries.
This project aims to understand how personal information in relation to beneficiaries in social
protection programmes is collected, stored, accessed and used in order to inform the
development of policies that safeguard the privacy rights of individuals.
7.1.4. Objectives
a) To identify the types of beneficiary information collected in Social Protection programmes;
b) To examine how social protection beneficiary information is stored, accessed and used;
c) To use the information gathered to advocate the strengthening of existing policies and inform
the development of new national, regional and international policies; and
d) To generate information that would support the creation of awareness on issues of the right
to the protection of personal information.
7.1.5. Expected outcomes
a) Improved management of information related to beneficiaries of social protection
programmes;
b) Increased understanding of the rights associated with individual privacy in relation to social
protection programmes; and
c) Increased buy-in and recognition of privacy rights of individuals by governments.
7.1.6. Project timeline, activities and outputs
7.1.7. Risks and limitations
One of the challenges envisioned is that of obtaining permission to carry out the study of
government-run programmes. There might be resistance as the issue under study is sensitive and
government suspicion might be high. To allay this, the APSP will seek to work with the
government from the onset of the study so that the nature of the study is understood. The study
will endeavour to collaborate with government personnel involved in the running of the social
protection programmes. The APSP works with National Civil Society Platforms that will engage
with their respective governments.
In cases where there may be no or little buy-in into the research findings by governments, the
APSP will continue to advocate for the respect of privacy rights for social protection
beneficiaries across the continent.
Activity Year 1 Year 2
Q1 Q2 Q3 Q4 Q1 Q2 Q3 Q4
Objective 1
Partners meeting (APSP & Privacy international)
Develop/review research questions for
interview/questionnaire (government, APSP & PI)
Develop research concept notes for sharing with
governments
Recruit local consultants
Stakeholders forum
Interview government officials, key informants and
beneficiaries (case studies) on beneficiary information
collected
Review beneficiary registries, literature review, interview
forms and support documentation within Social
Protection programmes etc.
Objective 2
Review the MIS in use
Interview government officers responsible for MIS,
communication, practitioners in the field
Interview beneficiaries views on privacy, consent,
resultant effects (if any)
Interview governments human rights agency on privacy
policy or lack of it
Analyse the research findings
Compilation of the report
Validation of report
Finalise the report
Objective 3 & 4
Develop an advocacy strategy based on the findings
Develop relevant advocacy materials
Present the report at inter-ministerial meeting of the AU
Present report at side event at CSD meeting in New York
Hold workshop with platforms to discuss/get their input
in advocacy strategy & materials
Incorporate privacy issues in platforms national work
plans & advocacy agenda
7.2. Asociacin por los Derechos Civiles, Argentina
http://www.adc.org.ar/
7.2.1. Organisational overview
The Asociacin por los Derechos Civiles (ADC) is a Buenos Aires-based independent NGO
created in 1995, committed to the promotion of respect for human rights in Argentina and Latin
America. It conducts research-based advocacy to promote changes in public policies and uses
precedent-setting public interest litigation to reverse violations of rights (e.g. gender rights,
discrimination, freedom of expression, access to public information) and to enforce social and
economic rights (health, education and labour). It also proposes legal and institutional reforms in
order to strengthen democracy.
7.2.2. Personnel
Jos Miguel Onaindia is the current President of the Board of Directors, and daily management
of the ADC is in the hands of lvaro Herrero, Executive Director. The ADC consists of fifteen
permanent staff members, the majority of whom are lawyers. The project will be coordinated by
Ramiro lvarez Ugarte, Director of the Access to Public Information Area.
7.2.3. Project summary
This project aims to tackle two distinct but closely-related challenges to privacy in Argentina. The
first issue is political surveillance, which, in the absence of effective oversight of intelligence
agencies, is a fact of life in Argentinian politics. Recent jurisprudence in the Supreme Court has
opened doors to enable debate about the role of intelligence agencies. The second issue is the
extensive collection of biometric information; the surrendering of personal information to the
State has been entrenched in Argentinian national culture since the advent of the National
Identity Card in the 1960s, and the establishment of a new database of biometric information
(SIBIOS) has thus far gone uncontested in public discourse.
7.2.4. Objectives
a) To raise awareness within the general public and specific stakeholders of the problems
involved in the extensive use of intelligence agencies for internal and partisan political
surveillance and of the risks involved in the massive collection and storage of biometric data;
b) To bring into public debate information, research and perspectives on the way these two
issues affect the rights of citizens and hamper democratic self-government;
c) To create instances of debate on these issues within civil society, bringing to the discussion
table the perspectives of public officials, journalists, academics and activists;
d) To provide a precise diagnosis of the specific problems involved in the legal framework that
regulates intelligence agencies and the recollection of biometric data;
e) To propose ways of solving these problems through the identification of best practices and
the development of specific reform proposals; and
f) To relate research with the situation of privacy in other countries of the Americas through the
Inter-American system of Human Rights.
7.2.5. Expected outcomes
a) A public better informed on privacy issues and on the perils of a surveillance society;
b) Stakeholders committed to the issue and working to solve the problems at hand;
c) An ongoing debate on political surveillance and on the extensive registration of biometric
data;
d) A network of actors interested in promoting reform; and
e) A set of tools available to promote change and reform through (i) lobbying, (ii) sharing of
information and (iii) strategic litigation.
7.2.6. Project timeline, activities and outputs
7.2.7. Risks and limitations
The projects main risk is that the research may not be effective in promoting the kind of public
debate and concern needed to advance any reform proposal. Another risk is that the
organisation will be subject to some kind of retaliation from the intelligence agencies themselves.
ADC believes their main tool for fighting these risks is an open and inclusive coalition of civil
society organizations and human rights activists capable of promoting change. If such a
coalition exists, the risks involved in possible retaliation measures would greatly diminish, and
ADC would have a strong voice promoting change. The proposed workshops and open forums
are aimed not only at gathering information but also at creating the conditions for building such
a coalition.
7.3. Autonomous University of Mexico State, Mexico
http://www.uaemex.mx/
7.3.1. Organisational overview
The Autonomous University of Mexico State (UAEM) is a public Mexican institution offering 47
undergraduate programs, two technical career programs, 84 postgraduate programs, 37
specialties, 36 master degrees and nine doctorate degrees. The institution maintains 12 research
centres and provides a system of distance learning education programs initiated in 1996.
7.3.2. Personnel
The researchers participating in this project are Nelson Arteaga Botello, Vanessa L. Lara
Carmona and Hiram R. Pia Libien. Nelson holds a Doctorate in Sociology (Summa Cum Laude)
from the University of Alicante, a Masters of Sociology (Honorary mention) from the University
Iberoamericana, and an undergraduate degree in sociology from the Autonomous University of
the State of Mexico. Vanessa is full time professor in the Political and Social Science
Department of the Autonomous University of the Mexico State and a Doctoral candidate in
Social Sciences, specializing in Sociology for The College of Mexico A.C. (2010). She holds a
Masters in Social Sciences from the Latin-American Social Sciences Faculty and a Bachelors
degree in Sociology from the Autonomous University of Mexico State. Hiram is a Doctor of Law,
specialising in Computer Law, and is currently Director of Legislative Matters of the General
Lawyers of the Autonomous University of Mexico State.
Activity Year 1 Year 2
Q1 Q2 Q3 Q4 Q1 Q2 Q3 Q4
Interviews and preliminary research and comparative
papers
Launching Conference
Closed Workshops
Open Forums and Policy Briefs
Media Campaign
Webpage / Resource Centre
Internet Campaign
First Draft of Final Report and Closed Workshop
Campaign to Promote Final Report
Final Report Presentation Conference
7.3.3. Project summary
This project aims to explain the effects of usage and regulation policies for surveillance devices
(video surveillance systems, identification cards, and copyright regulations such as the
controversial Anti-Counterfeiting Trade Agreement) on discriminatory practices and social
sorting processes in Mexico. Responding to the worrying links between the installation of video
surveillance systems and the implementation of urban renovation policies, the use of the
Identification Card for Minors for social classification, and the implications of ACTA for freedom
of expression, this project will seek to understand and expose the illegitimate purposes to which
surveillance technologies and arrangements are directed.
7.3.4. Objectives
a) To analyse the development of regulations for the installation of video surveillance cameras
in three of the countrys cities (The Federal District, Oaxaca and Queretaro) and to
understand the relation of each regulation to the particular characteristics of the
corresponding city, with regard to distinct urban development dynamics, social makeup and
political plurality;
b) To analyse the effect these regulations have on the location of cameras within the dynamics
of urban segregation;
c) To analyse the impact of the implementation of the Identification Card for Minors in Mexico,
and to identify potential risks of human rights violations with the collection and use of card
data; and
d) To analyse the social and human rights implications of a possible ratification of the ACTA,
and present regulation alternatives for information crimes in Mexico.
7.3.5. Expected outcomes
a) Regular and formal contact with public policy makers, as well as with other stakeholders in
the chosen issues;
b) Strengthened public debate on the human rights issues related to surveillance devices; and
c) Improved decision-making processes with respect to the use of surveillance devices.
7.3.6. Project timeline, activities and outputs
Activity Year 1 Year 2
Q1 Q2 Q3 Q4 Q1 Q2 Q3 Q4
Six-monthly work meetings with public policy designers,
non-profit organizations, expert consultants on research
problems (legal and social), and experts in security
technologies in Latin America.
Documentary research and the writing of three academic
papers that analyse the dynamics of the regulation for each
of the three subtopic (video surveillance systems, the
identity card, and the act). One document for the
comparative analysis.
Research and the writing of three policy recommendation
reports (one for each topic).
Updating of the current web site for the Latin American
network.
Yearly participation in public debates to generate policy
proposals directing the use and regulation of surveillance
devices.
Participation of the projects researchers in one international
seminar related to the topics of the project.
7.3.7. Risks and limitations
Freedom of expression has been a critical topic in Mexico, particularly with respect to research
that points out the weaknesses of institutions or the authorities. This project will carry out
positive research and the exchange of information, with the aim of maintaining a dialogue
without confrontation with stakeholders.
7.4. Bytes For All, Pakistan
http://content.bytesforall.pk/
7.4.1. Organisational overview
Bytes for All (B4A) Pakistan is a human rights organization with a focus on Information and
Communication Technologies (ICTs). It conducts research and organizes debates on the
relevance of ICTs for sustainable development and a strengthened human rights movement in
Pakistan. B4A is a legally registered NGO. As per bylaws of the organization, B4A can only act as
a non-profit, non-partisan organization, and its equality policy ensures that it works for all citizens
including religious and sexual minorities.
7.4.2. Personnel
B4As staff team is comprised of 9 professionals including researchers, trainers and management
staff and totally committed to the cause of ICTs for democracy, development and social justice.
7.4.3. Project summary
As Pakistan prepares itself for general elections within the next twelve months, there is an
important opportunity for privacy advocates to bring forward the issue of adopting a national
privacy policy. B4A collaborated with Privacy International in the Privacy in Asia project and will
continue the research and policy engagement that it commenced with this project. B4A will focus
on three particular privacy themes: a) communications surveillance, with a focus on internet
freedom; b) ID, DNA and biometrics; and c) data protection. B4A will particularly target its work
towards advancing privacy protections for human rights organisations and defenders.
7.4.4. Objectives
a) To monitor, document and report on privacy violations in Pakistan, with reference to the
projects thematic areas;
b) To actively engage with the UN Human Rights Council and Universal Periodic Review
process for human rights friendly privacy policies in Pakistan;
c) To conduct research on emerging issues undermining citizens online privacy in the country;
d) To campaign for data protection legislation; and
e) To build the capacity of stakeholders in online privacy and security.
7.4.5. Expected outcomes
a) B4A and selected civil society organizations have stronger knowledge about online privacy
and security;
b) Creation and fostering of leading voices for privacy rights in the country;
c) Partner organizations have implemented advocacy strategies to monitor and influence
policies that violate or threaten privacy rights of citizens in the country;
d) Coordination between civil society organizations working on privacy rights issues has
improved;
e) Steps have been taken to build a broader base of understanding and awareness about the
privacy rights for campaigns on emerging issues threatening privacy rights of the citizens;
f) The governments DNA database is officially shelved; and
g) Government develops a National Privacy Commission to uphold citizens privacy rights.
7.4.6. Project timeline, activities and outputs
7.4.7. Risks and limitations
A risk assessment reveals that the following factors may jeopardize the implementation of the
project:
- The law and order situation in Pakistan;
- A rapidly changing anti-democracy political situation in the country;
- The abrupt blocking of the communication sphere;
- Increasing inflation, which may hinder financial management of the project;
- Timely availability of resources for project activities; and
- Increasingly, no-go areas in the provinces.
B4A undertakes to mitigate these risks to the greatest extent possible by creating alternative
arrangements, and will consult extensively with Privacy International in this regard.
7.5. Centre for Internet and Society, India
http://cis-india.org/
7.5.1. Organisational overview
The Centre for Internet and Society (CIS), is a non-governmental not-for-profit organization
incorporated and registered in India. CIS will enter into a separate Memorandum of
Understanding with Society in Action Group for the purposes of this project.
7.5.2. Personnel
The project team at the Centre for Internet and Society will consist of a lead researcher, three
associate researchers and eight consultants including legal, media, outreach, and website
consultants.
7.5.3. Project summary
Currently, India is at a critical 'halfway' point with regards to privacy, as the government is in the
early stages of drafting privacy legislation, yet at the same time, projects and initiatives are
continuing to be implemented without statutory privacy safeguards in place. The Centre for
Activity Year 1 Year 2
Q1 Q2 Q3 Q4 Q1 Q2 Q3 Q4
Project inception & first visit of PI Team to Pakistan
Research on DNA Databases with Gene Watch UK
Research on Emerging Issues
UPR advocacy at UN Human Rights Council
Video Sprint on Privacy Rights
Capacity building program & privacy events
Exchange visit
Second visit by PI Team to Pakistan
Blogging, tweeting and social media networking for
Privacy Rights
Citizens campaign on Privacy Rights
Monitoring and evaluation
Progress Reporting
End of project report
Internet and Society began to research privacy in India in 2010. Since then, many developments
impacting privacy have taken place in India. This project will continue to generate vital research,
contribute to the challenges facing privacy, and influence policy impacting privacy in India.
7.5.4. Objectives
a) To provide input and influence India's privacy legislation and related policies through
research and multi-stakeholder dialogues;
b) To understand the extent, scope and impact of the traditional and emerging practices of
surveillance by the Indian government, to document these and to make them transparent,
and to recommend policy solutions to protect privacy; and
c) To raise awareness and make the right to privacy accessible to the general public,
the media, and international, national and local policy makers.
7.5.5. Expected outcomes
a) Influencing the establishment of regulatory and legal frameworks for privacy in India;
b) Engaging with policy makers with respect to policies from a privacy perspective;
c) Advancing political and academic discourse around issues related to privacy; and
d) Creating and improving public awareness of issues related to privacy
7.5.6. Project timeline, activities and outputs
7.5.7. Risks and limitations
The risks and limitations inherent in this project include:
a) The passing of the India Privacy Act: if India does not pass legislation on privacy, it will be
difficult to move forward with the objective of influencing and contributing to the legislation;
b) Acceptance of work with regards to upcoming legislation: though CIS is contributing to the
sub-committee and making recommendations to the privacy legislation, acceptance of these
recommendations is not guaranteed, which could limit the objective of influencing privacy
legislation; and
c) Capturing the attention of stakeholders at various levels of society: the project has the
objective of making the right to privacy accessible to a range of stakeholders and, although
CIS is connected to some of these stakeholders, reaching out to others and presenting
privacy in an understandable format might limit our ability to meet this objective.
Activity Year 1 Year 2
Q1 Q2 Q3 Q4 Q1 Q2 Q3 Q4
Policy analysis and trend following
Sting operations
Work around proposed privacy legislation
Blogging
White papers and expert interviews
Curriculum and guest lectures
Publication of sectoral policy guides
Online privacy community
Meetings with NGOs
Brown bags with media professionals
Round table discussions
7.6. Centre for Social Sciences Research, University of Cape Town, South
Africa
www.cssr.uct.ac.za/
7.6.1. Organisational overview
The University of Cape Towns Centre for Social Science Research (CSSR) is an interdisciplinary
research centre dedicated to conducting and building capacity for systematic, policy-relevant
social science research in South Africa, the region and across Africa. The CSSR conducts
problem-driven research on questions of democratization, development, poverty and policy; its
research is widely distributed and cited through regular seminars, a working paper series, and
additional publications and events.
7.6.2. Personnel
This project will be overseen by CSSR Director Jeremy Seekings, professor of sociology and
political studies, who has published widely on social protection. It will primarily be conducted by
Kevin Donovan, currently a Fulbright Fellow at UCT who has worked on new technology in Africa
for the World Bank and is currently researching them in the context of social protection in South
Africa (especially biometrics).
7.6.3. Project summary
The rise of social protection cash transfers has recently been hailed by one book as a
development revolution from the global South, signifying their growing importance on the
African continent. At present, there is a dearth of research on the ways in which beneficiaries are
being personally identified in social protection programs. The success of cash transfers requires
ensuring that the targeted recipients are reached. In some cases, existing identification systems
such as voter registration in Lesotho are utilized, but in others, entirely new systems are
required. Increasingly, worries about accuracy and fraud have motivated the use of biometric
identification for recipients such as in South Africa where around 10 million social grant
recipients are currently being enrolled in a new biometric initiative. This research will focus
specifically on how identification schemes particularly biometrics are being used by
governments and development organizations to deliver social protection. Although the topic of
research will be pan-African, South Africa will have particular emphasis given both the teams
location and existing experience, as well as the salience of identification and social protection in
the country. Apartheids system of identification and surveillance most famously through
mandatory passbooks has been well-documented and endows South Africa with a unique
legacy as a continuing pioneer in biometric statecraft. Additionally, South Africa has one of the
largest and most institutionalized systems of social protection, distributing grants to around 15
million beneficiaries monthly. Currently, the government and its private-sector contractor are in
the process of enrolling all recipients in a new biometric identification system to root out fraud.
7.6.4. Objectives
a) To identify the dominant trends and variety of approaches in the identification of social
protection recipients across Africa;
b) To understand for what reasons and causes these choices are being made; and
c) To analyse the emerging and likely outcomes and consequences of this form of
identification.
7.6.5. Expected outcomes
It is expected that this research will result in two broad outcomes. The process of the survey and
stakeholder consultations will serve to raise awareness within the social protection community of
key questions and issues related to privacy and biometrics. The researchs report and database
output will also serve to document and advance dialogue about how to meet the goals of social
protection in a way that is sensitive to privacy. As this is currently a largely overlooked area,
these outcomes should significantly contribute to improving policymaking.
7.6.6. Project timeline, activities and outputs
7.6.7. Risks and limitations
UCTs strong research capacity and reputation limits most risks to this research; however, one
potential challenge is ensuring the buy-in of social protection implementers in governments and
development institutions. This is most pertinent for a case study, but through a combination of
existing such as at the World Bank or emerging networks such as with the Africa Platform for
Social Protection should overcome any such difficulties.
7.7. Centro de Tecnologia y Sociedad, Universidad San Andres,
Argentina, and the Centro de Tecnologica da Escola de Direito da
Fundacao Getulio Vargas, Brasil
http://www.udesa.edu.ar/cetys
http://direitorio.fgv.br/cts/
7.7.1. Organisational overview
The project will be led by two universities in Brazil and Argentina: the Centro de Tecnologia y
Sociedad at the Universidad San Andres, Buenos Aires, Argentina, and the Centro de Tecnologia
e Sociedade da Escola de Direito da Fundao Getulio Vargas, Rio de Janeiro, Brasil.
7.7.2. Personnel
In Argentina, the project will be lead by Pablo Palazzi, working with researcher Lucila Gonzalez.
Prof. Doneda wrote a PhD thesis about data protection following an internship at the Italian Data
protection authority, and has undertaken research in Italy. He is also the founder of the Internet
Observatory at Getulio Vargas Foundation. He is the author of books and articles on data
protection and privacy. In Brasil, Danilo Doneda will lead the project with the assistance of
researcher Bruno Magrani. Prof. Palazzi has done research for CRID (Belgium), for Fordham
University law school (New York, with prof. Joel Reidenberg) and for the European Union with
respect to data protection laws in Latin America. He also prepared the reports on adequacy for
Argentina, Uruguay and Chile for the European Commission. The first two reports lead to the
adequacy approvals by the WP29 of the data protection laws of Argentina and Uruguay. He is
the author of several books on data protection and one book on computer crimes.
7.7.3. Project summary
The project will focus on the development of data protection legal frameworks in Latin American
countries from a primarily legal point of view. The researchers will identify the core issues of the
development of data protection laws in the region and their relation to the regions
Activity Year 1
Q1 Q2 Q3 Q4
Systematic literature review
Survey development
Conduct survey
Regional workshop
Research writing and editing
Output dissemination
characteristics, and will establish the pace of development in each country as well as gaps and
flaws in the systems that needs to be enhanced for future regulations. This project will go
beyond the mere compilation of statute and case law and will do a policy analysis of the
rationale for enacting data protection laws, the functioning of those laws and whether there is an
impact in the data protection level in the region.
7.7.4. Objectives
a) To build a systematic and comprehensive atlas of the data protection legal framework in
Latin American countries in order to determine the level of data protection regulations;
b) To identify the core differences between countries and group of countries in the region and
the current trends in Latin America;
c) To analyse the results of mapping laws and regulations as well as court cases. Has the level
of data protection rights been increased in practice after the enactment of the data
protection laws? and
d) To determine the rationale and objectives behind data protection laws, the level of
awareness in the population of their privacy rights, how the population exercises their privacy
rights, and the effectiveness of the system.
7.7.5. Expected outcomes
The output of the project will be a report on data protection in Latin America, showing the stage
of development of data protection legislation in the most important countries. This knowledge
base may serve as a basis or inspiration for the rest of the countries intending to legislate data
protection issues. The report would also include trends, flaws, and problems of implementation
of data protection in Latin America.
7.7.6. Project timeline, activities and outputs
7.8. Centre for Cyber Law Studies, University of Padjadjaran Bandung,
Indonesia
7.8.1. Organisational overview
This project will be conducted by the Centre for Cyber Law Studies, Faculty of Law, University
of Padjadjaran Bandung. This centre was established in early 2002. The organisation is chaired
by Professor Mieke Komar. The research centre focuses predominantly on cyber law issues and
other related issues such as e-Contract, online intellectual property rights and online privacy.
One of the major contributions of the Centre was the drafting of the Information and Electronic
Transaction Act 2008 with the Ministry of Information and Communication.
7.8.2. Personnel
Dr. Sinta Dewi will be the Project coordinator. In addition to working with the centre, Dr Dewi is
Activity Year 1 Year 2
Q1 Q2 Q3 Q4 Q1 Q2 Q3 Q4
Blog of the project
Compilation of raw data
Drafting report
International seminar
Interim conclusions
Final report
Survey of privacy rights
also a liaison for several government ministries relating to cyber law, telecommunication law,
convergence law and personal data law. Dr Dewi will be assisted by two other lecturers at the
university, Rika Ratna Permata and Prita Amalia, both of whom are experts on telecommunication
laws.
7.8.3. Project summary
Privacy protections under Indonesian law are limited in scope under the Constitution
Amendment. Although the Constitutional Court has elaborated upon the privacy protections, the
Courts decision has not yet been implemented, and is not well understood in Indonesian
political and public discourse. Privacy protections in Indonesia are closely related to two major
areas: (1) personal data protection, in connection with the identity card programme and the
credit card industry, and (2) surveillance and interception. Indonesia does not have any specific
regulations relating to personal data protection, only a Central Bank Regulation, and this has
lead to considerable difficulties in interpreting legal issues when the government or corporate
sector has breached protections related to distributions of personal data. These challenges to
privacy are also exacerbated by new technologies that provide easier ways to gather, analyse
and disseminate the personal information. With regard to surveillance, Indonesia has at least six
different regulations that authorise different government agencies to conduct wiretapping, but
no regulation of these activities. There is therefore a paucity of laws and policies in Indonesia to
regulate surveillance and data protection, and research is urgently need to understand how the
legal framework currently operates and where the legal and policy gaps exist.
7.8.4. Objectives
a) To raise awareness about privacy rights in Indonesia, particularly in personal data protection
with respect to the identity card programme and the credit card industry;
b) To monitor and report on surveillance methods employed by the government; and
c) To conduct research on how laws and policies in Indonesia address privacy, particularly with
respect to personal data protection.
7.8.5. Expected outcomes
a) Raised public awareness of privacy issues in Indonesia;
b) Targeted recommendations for policy-makers (government and parliament); and
c) Development of the legal framework.
7.8.6. Project timeline, activities and outputs
7.8.7. Risks and limitations
Since privacy is a new issue for government agencies and parliament, the main barrier is that
they will not attend the seminar. In order to gain a broader stakeholder attendance, the seminar
will be held in Jakarta and involve extensive media coverage. The other barrier relates to the
Indonesian publics current preoccupation with the issue of corruption; therefore, the privacy
Activity Year 1 Year 2
Q1 Q2 Q3 Q4 Q1 Q2 Q3 Q4
Preparing terms of reference for national seminar
Conducting national seminar
Public lecture
Reporting national seminar and preparing FGD
Conducting FGD
Preparing research paper
Attend international seminars
Submitting project report
issues and personal data protection will not attract much public attention unless media coverage
is extensive.
7.9. Thai Media Policy Center, Chulalongkorn University, Thailand
http://www.chula.ac.th/cuen/
7.9.1. Organisational overview
The project will be implemented by the research team at The Thai Media Policy Center (Thai-
MPC), Faculty of Communication Arts, Chulalongkorn University in Bangkok, Thailand.
7.9.2. Personnel
The team will be led by Dr. Pirongrong Ramasoota, who has extensive research experience in the
areas of surveillance, privacy, and the social implications of information and communication
technologies. Researchers in the team will be working in consultation and collaboration with
partners in civil society locally (such as iLaw, Association of Civil Rights and Liberty) and
international (such as Privacy International and the Australian Privacy Foundation).
7.9.3. Project summary
Thailand is one of only a few countries in the world that requires its citizens to hold national
identity cards. From the age of seven,
12
all Thai citizens are required to apply for Thai
identification cards, according to the National Identity Card Act 1983 (revised 2011). Currently,
the revised 2008 Civil Registration Act allows for the linking of personal data as it appears in civil
registration databases (including national identity card) for the purpose of maintaining national
security and peaceful order.
13
Launched in 2005, primarily to curb rising insurgency in the Malay-
Muslim dominated provinces in the south, the new smart ID card is believed to be the largest
integrated circuit chip ID card project in the world, combining smart ID cards with fingerprint
information using Match-on-Card. The linking of government databases of personal information
and bureaucratic surveillance through the new smart card have been practiced in the absence of
a comprehensive privacy or data protection law.
This project will undertake a political economy analysis of the biometric ID card sector in
Thailand. Apart from unravelling the aspects of biometric card use and its consequences, it will
also focus on how power and resources are distributed and contested in national identity
context and the underlying interests, incentives, and institutions that enable or frustrate change.
Such insights are particularly relevant if we are to advance the challenging issues around
governance of personal data, which, experience has shown, do not reflect much awareness and
will not lend themselves to technical and legal solutions alone.
7.9.4. Objectives
a) To understand the contextual factors, institutions, and social agents surrounding the
biometric ID card in Thailand;
b) To investigate the financing, procurement, and allocation of resources within the biometric ID
card sector;
c) To explore the nature of power relations between different interest groups (e.g. private
sector, NGOs, government, consumer groups) surrounding the biometric ID card in Thailand;
12
Although it
was never made public for fear of sounding discriminatory, it is quite widely perceived among the
Thai public that the Thai State enforces the ID card on seven-year-olds to help differentiate rights and benefits
of Thai children from those born of migrant labor from neighboring countries which is increasing in number in
recent years.
13
Section 12, Civil Registration Act, B.E. 2551 (2008).
d) To examine the history of the biometric surveillance sector and how this influences current
stakeholders perceptions on biometric surveillance;
e) To find out the privacy-related perceptions of subsets of stakeholders regarding biometric ID
card;
f) To analyse biometric surveillance practices and consequences thereof on civil, political, and
human rights of people in Thai society;
g) To assess whether any laws, regulations, practices or safeguards exist to address privacy-
related issues relating to the biometric card;
h) To unravel the dominant ideologies in the sector and to assess the extent to which these
ideologies serve to constrain change; and
i) To raise awareness, through the research findings, at local and international levels, about
threats to personal privacy and democratic citizenship rights as a result of the biometric ID
card.
7.9.5. Expected outcomes
While the general outcome of the project will be to arrive at tangible research findings on the
political economy of biometric card in Thailand, its application will go further than advancing
academic discourse around privacy issues. This set of findings shall equip advocacy units and
activists concerned about privacy and civil rights with capacity to improve public awareness
about biometric surveillance through ID card and its social consequences. Furthermore, the
dissemination of knowledge and ensuing advocacy should also affect policy-making, particularly
the establishment of regulatory and legal frameworks related to biometric surveillance and
privacy.
7.9.6. Project timeline, activities and outputs
Activity Year 1 Year 2
Q1 Q2 Q3 Q4 Q1 Q2 Q3 Q4
Contextual analysis and key informant interviews to
map out the past history of the biometric ID card sector
Contextual analysis and key informant interviews to
identify key stakeholders in the area of biometric
identity card in Thailand
Literature reviews and desk research to analyse national
laws, regulations, practices and safeguards which
already exist to protect citizens right to privacy and the
personal data contained in biometric ID card
Questionnaire-based survey to assess the perception of
subsets of stakeholders with respect to the biometric
identity card
Case study and stakeholder consultations to examine
the financing, procurement and allocation of resources
in the biometric ID card sector
Key informant interviews and stakeholder consultations
to investigate how different interest groups, in addition
to the government, seek to influence biometric ID card
policy
Case study and stakeholder consultations to identify
primary beneficiaries of the services using biometric ID
cards, and to determine whether there is social, ethnic,
or class inclusion/exclusion/sorting as a result
Key informant interviews and stakeholder consultations
to unravel dominant ideologies and values which shape
views around the biometric ID card
Public awareness campaign through academic
7.9.7. Risks and limitations
The main risk that is likely to be encountered is the reluctance of key agencies and stakeholders
to cooperate. Moreover, in the deeply divided context of current Thai politics, bureaucrats as
well as policy-makers are likely to play it safe and not incriminate themselves or their
associates by revealing sensitive information. The researcher may have to mitigate these risks
through workable connections and by promising total anonymity for the key informants.
7.10. Derechos Digitales, Chile
http://www.derechosdigitales.org/
7.10.1. Organisational overview
ONG Derechos Digitales (Digital Rights Non-Governmental Organisation) is an independent,
non-profit organisation founded in 2004, whose mission is to promote the defence and
protection of human rights in the digital environment. The organisations main areas of work
include freedom of expression, access to knowledge, transparency and democracy, privacy and
personal data protection, consumer protection, open business, and open education. The
organisation has been part of the Advisory Committee of Ministers for Digital Development in
Chile, the (Chilean) National Committee of Domain Names and Internet Protocol Numbers, and
of the National Net of Digital Citizens Organizations; and with the University of Chile represents
Creative Commons licenses in Chile.
ONG Derechos Digitales is currently developing a project to strengthen civil society through the
exercise of fundamental rights in the online environment called Strengthening freedom of
expression, privacy and copyright in the digital environment. This is being designed according
to user habits regarding the exercise of freedom of expression, copyright and privacy rights, and
taking into account the institutional procedures that could undermine the exercise of those
rights. This initiative includes both field and legal research, online campaigns, workshops, a
good practices guide, and making a website regarding freedom of speech.
7.10.2. Personnel
Work Team:
Claudio Ruiz Gallardo, lawyer, President.
Francisco Vera Hott, lawyer, Executive Vice President.
Daniel lvarez, legal scholar, Legal Director.
Alberto Cerda, legal scholar, Studies and International Director.
Brbara Soto Morales, lawyer, Junior Researcher
Armando Torrealba, graphic designer, Chief Designer.
Paz Pea Ochoa, journalist, Head of Communications
Hctor Vergara, computer engineer, Technical Advisor.
Organisation advisors:
Pablo Crcamo, sociologist, Methodology Consultant
Salvador Millaleo, legal scholar, External Advisor.
Patricio Velasco, sociologist, Project Consultant.
Daniel Hernndez, computer sciences researcher, Data Analysis Consultant.
7.10.3. Project summary
The Latin American region has many challenges ahead regarding privacy protection. One of
those challenges is to identify the legal framework and common practices related with criminal
prosecution, communications surveillance and data retention in the region. Crime prosecution is
seminars, public service media, and online blogs
a very sensitive issue and new technologies, whilst offering a huge opportunity for development
and progress, also create opportunities for illegal activities. To address those risks, all countries
have passed laws giving the courts and criminal enforcement bodies the power to intercept
communications in given cases, to seize computers and to request personal data from the
Internet Service Providers on individuals connections, location or activity. This project aims to
create a regional report on communications surveillance and data retention and retrieval for the
purposes criminal prosecution in Latin America.
7.10.4. Objectives
a) To prepare an extensive privacy report on Chiles legal framework and practices;
b) To obtain and compare data on privacy and criminal prosecution across Latin American
countries in order to identify common standards in the region;
c) To find out if the practices of public prosecution officers are in compliance with local and
regional human rights standards regarding privacy law;
d) To support future campaigns and policy engagement efforts in Latin American countries; and
e) To establish a regional network on crime prosecution and privacy, to share data and research
efforts.
7.10.5. Expected outcomes
a) Creating national and regional awareness about the privacy issues raised by crime
prosecution, among stakeholders in general and civil society organizations in particular;
b) Setting a reform agenda regarding privacy and crime fighting in the region, in order to
achieve an adequate level of protection;
c) Motivating future campaigning and policy engagement on crime prosecution and privacy
issues;
d) Identifying individuals and organizations who are working or willing to work on privacy issues
in countries without strong civil society engagement in privacy and/or fundamental rights;
and
e) Providing a starting point for networking and capacity building programs in the region.
7.10.6. Project timeline, activities and outputs
Activity 2013 2014
Q1 Q2 Q3 Q4 Q1 Q2 Q3 Q4
Chilean extended privacy report (Report 1)
Design of the investigation instruments
Chilean survey taking
Chilean survey results validation (national workshop)
Latin American legal framework report (Report 1)
Regional survey preparation
Workshop with selected Latin American countries
Survey application (regional level)
Processing of survey results
Criminal prosecution and privacy Latin American report (Report
3)
Translation
Website design
Website launch (first x will be an internal website)
Regional report printing
Regional report launching and distribution
7.10.7. Risks and limitations
a) Information gaps online: for some countries, information on their laws and judicial decisions
may not be available online. This issue will be solved by contacting law scholars from those
countries directly or, in extreme cases, by traveling and directly obtain the information; and
b) Personal security of survey takers: in some countries, personal security and official corruption
are issues which can represent a threat to the people who are conducting research. This
issue will be addressed through the planned workshop, which will have a special section on
fieldwork and security threats, giving advice and tools for working in difficult security
conditions without compromising the personal security and integrity of regional partners.
7.11. Dejusticia, Columbia
http://www.dejusticia.org/
7.11.1. Organisational overview
Dejusticias mission is to promote human rights and social inclusion, bolstering democracy and
the rule of law in Colombia and abroad. Dejusticias vision is to be recognized as an institution
that, based on a hybrid strategy of research and action, influences public opinion, academic
debate and public policy by means of providing expert knowledge to the academic,
governmental and civil communities domestically and internationally. Dejusticia has five lines of
work: economic, social and cultural rights; anti-discrimination; rule of law and legal culture;
judicial system; and transitional justice.
7.11.2. Personnel
Rodrigo Uprimny, who will be the director of the project, is also General Director of Dejusticia.
He holds a Ph.D. in Political Economy from the University of Amiens Picardie, an M.A. in
Sociology of Law from the University of Paris II and an M.A. in Social Economy of Development
at the University of Paris. Miguel Emilio La Rota, lawyer and economist from the University of the
Andes, will be one of the senior researchers leading the second component of the project. He
holds an M.A. in public administration and public policy from Columbia University. Today, he is
Senior Researcher and coordinates the Justice System thematic area at the Center for the Study
of Law, Justice and Society-Dejusticia. Diana Esther Guzmn, J.D., specialist in constitutional
law and M.A. in Law from the Universidad Nacional de Colombia, will be one of the senior
researchers leading the third project component. Vivian Newman, deputy director of Dejusticia
will be the lead researcher on the first component of the project. Vivian holds a J.D. from the
Universidad Javeriana officially approved by the University of Barcelona. She holds Master's
degrees in (DEA) Domestic Public Law from the University of Paris II Panthon-Assas and in
Cooperation and Development from the University of Barcelona.
Annika Daln, political scientist from the University of Uppsala (Sweden) and M.A. in gender
studies at the Universidad Nacional of Colombia, will work on the third component of the
project, while Carolina Bernal, J.D. from Universidad Eafit with two exchange semesters at
Universidad de los Andes and Universidad del Rosario, will work on the second component.
Carlos Corts, lawyer from Los Andes University of Bogot, MsC in Media and Communications
Governance, London School of Economics, will work on the second component, offering a
comparative perspective, and will also collaborate with researchers across the project by
advising on the progress of the three components as well as advising on and editing conclusions
and recommendations of the various outputs.
7.11.3. Project summary
Although a constitutional framework exists through many international conventions and an array
of laws that guarantee the right to privacy and intimacy in Colombia, there are great difficulties in
its implementation. There are three predominant privacy challenges in the country. The first
relates to access to information; while Columbia has recently adopted a Transparency and
Access to Public Information law, there is no understanding of how the government might apply
the exceptions to freedom of information, and there is ignorance of modern standards and
proportionality tests applicable to protecting or revealing private information. The second
challenge is the existence of surveillance and intelligence regulations, which are often
ambiguous, flawed or misapplied. The third challenge relates to womens sexual and
reproductive rights, and concerns the nefarious use of the Inspectorate General to expose
abortion practices.
This project aims to promote a balanced approach in a host of paradigmatic tensions
surrounding privacy, security and disclosure in Colombia: on the one hand, the right to privacy
and intimacy as well as the exercise of sexual and reproductive rights, and, on the other, access
to public information, the preservation of national security and the enforcement of the law and
public order.
7.11.4. Objectives
a) To contribute to the understanding and implementation of modern and international
standards and proportionality tests in order to work out and settle the tensions between
protecting or revealing privacy interests involved in public information;
b) To evaluate the risks and appropriateness of implementing the new Intelligence Law with
regard to constitutional privacy standards, and to measure the levels in which stop-and-
search police practices infringe constitutional privacy standards; and
c) To promote strategies and policies aimed at raising awareness of and protecting womens
access to sexual and reproductive rights without risking violation of their privacy from public
entities, as well as the right of public servants and medical staff to comply with their
professional duties without facing such repercussions.
7.11.5. Expected outcomes
a) Public servants will be able to rely on practical rules and guides for the protection of private
interests when deciding about the disclosure of public information;
b) The public will be aware of the relevance and importance of their own private interests and
intimacy rights;
c) Constituents (including public officials) will be able to rely on a broad assessment of the
Intelligence Law as well as with recommendations on certain urgent issues;
d) The public will be informed of the levels at which stop-and-search police practices infringe
constitutional privacy standards;
e) Women and womens organizations will be able to rely on strategies and policies which
protect their right to access sexual and reproductive services without risking violation of their
privacy from public entities; and
f) Public servants and medical staff will be able to meet their professional duty of confidentiality
in connection with the practice of abortion.
7.11.6. Project timeline, activities and outputs
Activity Year 1 Year 2
Q1 Q2 Q3 Q4 Q1 Q2 Q3 Q4
1) Privacy vs. Access to public information:
Implementation guide
Compilation of applicable legal framework
Study of case law
Further research on comparative law and best practice
Focus group/interviews with representatives of
stakeholders
7.11.7. Risks and limitations
There is a possibility that the current Inspector General, Alejandro Ordez, will not be re-
elected after his four-year term in office expires at the end of 2012. This would probably mean
that the Delegate of the Inspector General in Defence of the rights of Infancy, Adolescence and
Family, Ilva Myriam Hoyos, would not continue in her post either, as she is part of Ordez team
and holds her post to a large extent due to her ideological proximity to the Inspector General.
This scenario would imply a slight change in focus of the case study, expanding it to include not
only the Inspector Generals office but also other public entities that develop public policies
detrimental to privacy rights, particularly the sexual and reproductive rights, of women. In case of
a change in Inspector General, the most likely development is that the two main focal points for
the study Alejandro Ordez and Ilva Myriam Hoyos obtain public posts in other entities,
which would imply a necessity for a closer study of the policies and actions taken from those
new positions and their connection with the regulations and standards initiated in the Inspector
Generals Office.
There is also a risk that Statutory Law of Access to Information, currently under examination at
the Constitutional Court, is declared unconstitutional and void. In this event, the implementation
methodology guide offered in this proposal would still be based on case law and shared with
public servants but should be focused on the application of the current laws (about 20 laws
regarding data retention of which approximately 50% refer to private interests).
Validation of preliminary conclusions in the internal legal
committee or seminar
Finalising conclusions and recommendations
Dissemination of results
2) General Assessment of the intelligence law and its
connection with privacy constitutional standards
Compilation of applicable legal framework
Comparative law analysis
Analysis of survey results
Interviews with relevant actors
Validation of preliminary conclusions with internal legal
committee or internal seminary
Further research to tie up conclusions and close open
questions
Additional validation
Dissemination of results
3) Privacy and sexual and reproductive rights: A case
study
Compilation of applicable legal framework
Research
Interviews with relevant actors
Validation of findings with internal legal committee
Dissemination of results
Policy engagement
For the three components:
Publication of op-eds, depending on the opportunity
Participation in public debates depending on the
opportunity
Strategic litigation, if applicable, depending on the context
7.12. Instituto Nupef, Brazil
http://www.nupef.org.br/
7.12.1. Organisational overview
Instituto Nupef (Center of Research, Studies and Learning) is an independent, non-profit
organization based in Rio de Janeiro and registered in January 2009. Nupef is dedicated to
reflection, analysis, knowledge production and learning activities, with focus on ICTs as they
relate to policy-making and political processes which affect democracy, human rights,
sustainable development and social justice. Among its activities are: online and face-to-face
learning workshops, action research, development of case studies, promotion of events and
campaigns, production of printed and online publications, and advocacy. The main target
groups of Nupef's activities are: policy makers, governments, academics, civil society activists,
the media, and citizens involved or interested in knowledge building strategies to respond to
challenges which networked societies are confronted with - especially in the assertion of the
right to knowledge, freedom of expression, protection of privacy, and protection of cultural
diversity, among other fundamental rights.
7.12.2. Personnel
Coordination team:
Executive Director: Carlos A. Afonso
Financial Director: Mauro Ferreira Campos
Project and Communications Coordinator: Graciela Selaimen
Research and advocacy team:
Research Coordinator: Graciela Selaimen
Research Assistant: Julia Perez Guimares
Consultants: Graciela Hopstein and Ivnio Barros
Communications Team:
Journalist: Viviane Gomes
Intern: Isabella de Paiva
Possible partner for advocacy activities: Sexual Policy Watch, represented by Magaly Pazello.
7.12.3. Project summary
Instituto Nupef will conduct research into the uses, the professional and institutional practices
and the sociotechnical systems and technological architectures of e-health solutions with a
special attention to Electronic Health Registers - adopted by public health institutions in Brazil, in
order to understand the potential threats to individuals privacy and security introduced by their
adoption. The project is especially focused on the possible threats posed by e-health solutions
to the privacy rights of vulnerable populations such as poor women, HIV/Aids patients and the
LGBT community, due to the lack of regulation and policies that assure the proper collection,
storage and processing of sensitive personal data. With the outcomes of this work the project
will help to raise awareness among social activists, the media, policy makers and regulators; to
influence public policies and legislation for the protection of patients; and to offer possible
solutions for the development and strengthening of privacy provisions in already existing
vulnerable e-health assets and structures.
7.12.4. Objectives
a) To offer a clear picture of the present fragility of the privacy rights of patients assisted in
public health institutions that are using e-health systems;
b) To recommend policy frameworks with which to guide future decision-making in the e-health
area in Brazil; and
c) To inform the development of policies and regulatory frameworks that can prevent abuses,
provide safeguards, and ensure adequate remedies in relation to privacy in public e-health
initiatives in Brazil.
7.12.5. Expected outcomes
a) Verification of the existence of measures to protect privacy in existing e-health systems in
Brazil and understanding of their nature, effectiveness and extent;
b) A more informed discussion of specific measures and criteria related to e-health and privacy
within the national data protection legislation debate in the Brazilian National Congress;
c) Increased discussion about the need for specific legislation and public policies focussing on
the protection of privacy of the users of the Brazilian National Health System (SUS);
d) The adoption of provisions for strong and effective privacy protections in public e-health
initiatives; and
e) Increased awareness of, and educational materials regarding, threats to personal privacy in
e-health systems among policy makers, regulators, health professionals, civil society
organizations and activists who work in the defense of human rights and vulnerable
populations.
7.12.6. Project timeline, activities and outputs
Activity Year 1 Year 2
Q1 Q2 Q3 Q4 Q1 Q2 Q3 Q4
Compilation of existing regulation on health data collection by
public health institutions
Development of specific questionnaires for each of the
stakeholder groups
Application of questionnaires, tabulation and analysis of results
Development of in depth interview protocols for each of the
stakeholder groups
Realization of interviews and analysis of results
Conduction of focus groups
Recollection of stories
Organization of meetings with representatives of each of the
stakeholder groups to present and discuss research findings
Publication of research brief
Publication of policy brief
Dissemination of research brief
Dissemination of policy brief
Production and distribution of awareness raising material with
stories
Organization of a breakfast with journalists to present the
research products
Participation in national events seminars, workshops,
sessions in the Congress to disseminate the research products
Internal monitoring of processes and achievement of the
project milestones and objectives
External evaluation
7.13. Kenyan Ethical and Legal Issues Network, Kenya
http://kelinkenya.org/
7.13.1. Organisational overview
KELIN is a legal non-governmental organization working to protect, promote and advance health-
related human rights in Kenya through the provision of legal services and support, the training of
professionals on human rights, engagement in advocacy campaigns that promote awareness of
human rights issues, and the generation of research and influencing policy that promotes
evidence-based change.
KELIN will partner with the Kenya Paediatric Association (KPA) to train healthcare workers on the
legal and ethical issues relating to HIV, and with the National Empowerment Network of People
Living with HIV (NEPHAK) with whom KELIN have previously worked, providing legal advice and
training to their members on matters relating to human rights violations in the context of HIV.
Partnership agreements will be developed to guide the clear role of each partner in the
implementation of the project.
7.13.2. Personnel
KELINs Executive Director will be responsible for the overall implementation of the project, the
advocacy and training officer responsible for the aspects relating to meetings, collection of data
during the research study and the delivery of training. The Communications Officer will be
responsible for the quality of awareness material developed, and will document any success
stories from the project. The Monitoring and Evaluation Officer will be responsible for the
monitoring aspects of the project on a quarterly basis and will liaise with the external consultants
on the midterm review and final evaluation of the project. The Finance Officer will be responsible
for the finance aspects relating to this project and the administrative assistant will provide
logistical support to the project staff.
7.13.3. Project summary
The need to uphold the right to privacy and confidentiality in the context of the status of HIV-
positive patients is integral to preventing stigma and discrimination of people living with
HIV/AIDs. The exposure of information relating to ones HIV status without consent exposes
individuals to human rights violations including dismissal from employment, denial of access to
health facilities, denial of access to education services and denial of provisions of insurance
services. The breach of the right to privacy and confidentiality has also seen many women
exposed to physical and sexual abuse in family and societal contexts. The objective of this
project is therefore to provide an enabling legal and policy environment for the protection of
information relating to the HIV status of persons living with HIV in healthcare settings.
7.13.4. Objectives
a) To conduct research into the level of awareness and understanding, among healthcare
workers and people living with HIV, of the legal and policy provisions relating to the right to
privacy in relation to HIV.
b) To build competencies of health care workers in upholding the right to privacy and
confidentiality in the context of HIV through trainings and educational materials;
c) To empower the public and people living with HIV with regards to their right to privacy and
confidentiality in the context of healthcare, through media and educational materials; and
d) To share the findings of the research with key stakeholders in the health and HIV sector in
order to inform policy change.
7.13.5. Expected outcomes
a) Improved awareness among healthcare workers and people who are living with HIV of the
importance of the right to privacy and confidentiality in the context of HIV.
b) Human rights based policy reform founded on policy makers engagement with the findings
of the research.
c) An understanding of the challenges faced by healthcare workers in upholding the right to
privacy and confidentiality.
d) Improved capacity of healthcare workers to address the challenges faced in the context of
right to privacy.
e) Enhanced capacity of people living with HIV to address instances of breach of right to
privacy.
7.13.6. Project timeline, activities and outputs
7.13.7. Risks and limitations
The major risk the project faces is that it will be implemented during a period when Kenya is
having elections. Given the previous experience, this may slow down the work to be undertaken
in the last month of the first quarter and the first month of the second quarter of year one. In
order to counter this risk, the project will allow room for extended project activity in the second
year in case there is need to push the activities back as a result of the delay occasioned by the
elections.
7.14. Mauritania and Senegal Research Network
http://jonctionsenegal.free.fr/
7.14.1. Organisational overview
This is a research project undertaken by Jonction, a Senegal-based NGO. A doctoral student
from McMaster University, Philippe M. Frowd, will work in collaboration with Jonction throughout
the project.
7.14.2. Personnel
Two project coordinators will undertake the research: Ababacar Diop, President of Jonction,
Senegal, and Philippe M. Frowd.
Activity Year 1 Year 2
Q1 Q2 Q3 Q4 Q1 Q2 Q3 Q4
Oversight committee initial planning meeting
Research conducted
Oversight committee meeting
Advocacy meeting to share findings of research
Training of healthcare workers and PLHIV
Participation in radio talk show
Mid-term review of the project
Preparation of advocacy material
Dissemination of advocacy material to partners
Final evaluation of the project
Dissemination of evaluation reports
Oversight committee closure meeting
7.14.3. Project summary
This project will look at two main trends that are taking place in West Africa: the turn towards
biometric national identification systems, and forms of border management, both of which are
instantiations of a linkage between security/surveillance and development. This project will form
part of a larger doctoral dissertation research agenda looking into how African countries seek to
modernize and to make their populations more legible. This research project will focus on
Mauritania and Senegal.
7.14.4. Objectives
a) To provide a comprehensive overview of the privacy/security/surveillance landscapes in two
countries for which such an exercise has not been done before;
b) To enquire into the norms and ideas that influence the uptake of biometric technology in
African countries. To what extent is this trend path-dependent on colonial legacies? What
role do international organizations play in propagating biometrics?;
c) To uncover the means through which governments in West Africa justify certain border
control and identity management policies; and
d) To add a privacy angle to policies such as border and migration management undertaken
by Senegalese gendarmes that are not otherwise considered from this standpoint.
7.14.5. Expected outcomes
The primary outcome of this project will be to build up a stock of research for professional and
academic purposes on an issue border management and identity management in West Africa
that is the focus of very little research at present. This research will be able to inform bodies of
existing work on these phenomena in Europe and North America. Research results may also help
certain organizational interlocutors (such as the IOM) to refine their practices.
The second outcome will be to enhance public awareness particularly in Senegal of privacy
rights in the nascent information society. It is hoped that activities in Senegal will also
strengthen links between civil society actors already working in Senegal.
7.14.6. Project timeline, activities and outputs
Activity Year 1
Q1 Q2 Q3 Q4
Research
Literature review
Laws, regulations, standards, safeguards (Senegal and Mauritania)
Policy documents from international organizations (EU, IOM, ICAO)
Interviews in Senegal (January-February 2013)
Officers at the Gendarmerie Nationale
Officials at Ministry of Interior
Interviews in Mauritania (February-March 2013)
Staff at the International Organization for Migration
Officials at the Direction Gnrale de la Scurit Nationale
Deliverable
Workshop #1
Deliverable
Presentation at International Studies Association annual conference: Biometrics
and border management in West Africa
Deliverable
Report: Mapping the Privacy Landscape in Senegal (bilingual)
Deliverable
Workshop #2
7.14.7. Risks and limitations
The main risk for this project concerns access to research interlocutors. Obtaining access to
government officials and security actors in African countries can be quite challenging, and a
network of personal contacts is the most effective way of ensuring a foot in the door. This will
be mitigated by using existing personal connections (in both countries), familial relations (in the
Senegalese gendarmerie), by building a research network through workshops, and through a
snowball interview methodology.
The other main risk is a political one: any political activity even raising awareness in
Mauritania is fraught with risk, and for a foreign researcher any kind of political involvement (let
alone advocacy) is a very unwise move. There is, thankfully, a very low potential for any kind of
harm to the research team or to research subjects during the course of this research in
general. This risk will be mitigated by only disseminating the results of the research in Mauritania
to Privacy International and local interlocutors (and only if these interlocutors give their consent).
7.15. Media Institute of Southern Africa (MISA), Namibia
http://www.misa.org/
7.15.1. Organisational overview
MISA is a regional organisation with eleven national chapters in the Southern African
Development Committee. The founding of MISA was triggered by the Windhoek Declaration of
1991 by a group of activist media practitioners. MISA Education and Production Trust was
registered on 12 October 1994 in Windhoek, Namibia, by a group of activist media practitioners.
The aim of the Trust is to promote and strengthen a pluralistic and independent media in
Southern Africa as a pillar of the democratic process. MISA was formed against the backdrop
of media violations and harassment of journalists by governments in the region.
7.15.2. Personnel
Zoe Titus is the Regional Director for MISA, where she has worked for the past ten years. She
has a unique set of skills and knowledge in project management, fundraising and leadership. She
is also a member of various regional and global media networks where her expertise is
constantly sought. MISA has eleven National Chapters across southern Africa, all under her
watch. Bramwell Kamudyariwa is the Regional Manager for Finance and Administration at MISA.
Bramwell has worked extensively within southern Africa, at one time managing a newspaper
group in Zimbabwe. As a result, he holds extensive experience in managing large organisational
budgets. He has played a critical role at MISA in the review and operation of the organisations
finance and administration systems, much to the satisfaction of the basket funders.
Levi Kabwato (project contact) is the Programme Specialist for Media Freedom Monitoring &
Research at MISA. He has extensive knowledge of media freedom, freedom of expression and
broader human rights issues within southern Africa. He has previously conducted workshops and
training for journalists and media practitioners in the area of Digital Media and Digital Media
Security.
7.15.3. Project summary
The political situation in southern Africa is very fragile. The democratisation project, embarked
Deliverable
Report: ID and biometrics in Senegal and Mauritania
Deliverable
Research paper: Integrated border management and the security-development
nexus in West Africa
upon by most countries in the 1990s, is under threat as governments increasingly put massive
restrictions around media freedom and freedom of expression, often guaranteed rights in the
Constitution. In the aftermath of the developments in the Arab world, where several regimes
have fallen in revolutions largely credited to the organisation and mobilisation power of internet
applications, southern African governments seem to be awakening to this potential and have
showed determined intent to extend systematic repression beyond their geographical borders
and into cyberspace.
This project aims to contribute to the development and organising of knowledge about the
internet, online privacy and cyber security. This knowledge will aid the target audience in
becoming aware of their privacy rights and also empower them with ways of detecting and
circumventing surveillance. An added benefit will be the demystification of technology. In
achieving the above, the project will also mainstream the discourse on privacy as a fundamental
human right that needs to be protected across southern Africa and beyond. Hence, the project is
also designed to inform the development/improvement of tools for monitoring and detecting
surveillance practices, thereby increasing citizen control of the use of technology and perhaps
ushering in best practices.
7.15.4. Objectives
a) To raise awareness on issues surrounding digital security (privacy, censorship and
surveillance) for citizen and mainstream journalists in southern Africa;
b) To increase the capacity of southern African citizen and mainstream journalists in using digital
media tools to research and present evidence of human rights violations;
c) To familiarise southern African citizen and mainstream journalists with existing legal
frameworks (criminal defamation and insult laws), how these can be used to restrict Freedom
of Expression in cyberspace, and what strategies and tactics can be adopted to defend the
online space; and
d) To add to the currently thin body of knowledge on freedom of expression in cyberspace by
producing research papers, reports and manuals on promoting privacy and circumventing
repression in cyberspace, as well as on tactics to protect against and methods of detecting
and countering digital surveillance.
7.15.5. Expected outcomes
a) Citizen and mainstream journalists trained on methods and tactics of protecting their privacy
and circumventing digital surveillance;
b) Raised public awareness of issues of privacy and security online through the aid of media
networks;
c) A body of knowledge targeting freedom of expression in cyberspace, developed and made
widely accessible as part effort to streamline the related discourse; and
d) A review and comparative analysis of legal and regulatory frameworks in southern Africa,
leading to engagement with multiple stakeholders with the aim of reform ensure that there
are satisfactory safeguards for online privacy.
7.15.6. Project timeline, activities and outputs
Activity Year 1 Year 2
Q1 Q2 Q3 Q4 Q1 Q2 Q3 Q4
Research on challenges to online privacy in southern
Africa: understanding of laws, policies and
frameworks
Training/Workshop: Understanding FoE in Cyberspace
and Protection of Privacy Online: Tools and Tactics
for Online Activists
7.15.7. Risks and limitations
The project faces the risk of not having sufficient uptake by other stakeholders who are not
necessarily the target audience. This is because issues of privacy online and digital surveillance
are not currently seen as a major human rights concern. This risk will be addressed by
mainstreaming these issues into the public discourse through the aid of media networks.
Related to the above is the lack of a critical knowledge base that is focussed on southern Africa,
which can inform research and thought leadership efforts on the project. This will be addressed
by building a body of knowledge that is specific to southern Africa but also draws on other
sources from across the globe.
7.16. My Computer Law, Thailand
https://thainetizen.org/
7.16.1. Organisational overview
Thai Netizen Network (TNN) is a non-partisan group which advocates for Internet freedom,
human rights and civil liberty. Founded in 2008 by members from various professional
backgrounds, the Network runs activities based on five themes: right of access to information;
right to freedom of opinion and expression; right to privacy; participatory internet governance;
and commons. The Networks current focus is on the civil rights of internet users and the
amendment of the Computer-related Crime Act B.E. 2550. It gives consultation to human rights
lawyers on cases involving computer-related crime, and makes recommendations on the law and
its enforcement. The Network takes an active role in educating the public about media policy,
digital culture, and internet freedom through public forums, informal seminars and workshops,
university special lectures, and publications. Past activities include computer security training for
independent journalists in Bangkok, Chiang Mai, and Deep South.
7.16.2. Personnel
Personnel will be recruited specifically for the project. Two staff members from Thai Netizen
Network, Arthit Suriyawongkul (Coordinator) and Wasumol Boonyakiat (Assistant Coordinator)
will oversee the project during for the initialisation stage. Arthit Suriyawongkul has worked in
internet freedom since 2007. Prior to this, he worked in informatics research and development.
Wasumol Boonyakiat was a project analyst at National Electronics and Computer Technology
Center (NECTEC) before undertaking further study in Technology Management at Thammasat
College of Innovation. She was a coordinator for EUAsiaGrid, a Europe-Asian grid infrastructure
for e-science.
7.16.3. Project summary
In the context of Thailands rapidly expanding community of internet users and online services,
the lack of data protection and privacy regulations and laws is extremely concerning. Public
awareness of privacy issues, particularly those related to online services, is extremely low, and
there is a paucity of public knowledge about how personal data is used online. This project will
tackle these issues, and place them in a context of increasing communications surveillance by
the Thai government. Educating internet users about security measures and the safety of their
Conference attendance: International Symposium on
Online Journalism (Texas, United States)
Lecture: Citizens as Netizens: Practicing Democracy &
Exercising Human Rights Online
Survey: Framing FoE in Cyberspace in southern Africa
Campaign: Demanding Legal Protection for Citizens
Privacy Online
online communications and activities is key to increasing respect for and protection of privacy in
Thailand.
7.16.4. Objectives
!" To make Internet users aware of the level of protection they currently have;
#" To make online service providers aware of the their level of security measures and areas
requiring improvement; and
$" To make workers in information-processing industries aware of privacy issues and good
practices for data protection in the industry.
7.16.5. Expected outcomes
a) Greater understanding of privacy policy and security measures in Thailand; and
b) Increased public awareness of issues relating to online privacy and data protection.
7.16.6. Project timeline, activities and outputs
Activities Year 1 Year 2
Q1 Q2 Q3 Q4 Q1 Q2 Q3 Q4
Online Service Privacy Policy Evaluation
Online Service Security Measures Evaluation
Reprint of Security-in-a-Box A5 Flashcards
Privacy Study/Advocacy Book Thai Translation
Kickstart Expert Meetings (Web Developers + Privacy Experts)
Survey on Internet Users Understanding of Privacy and Security
Privacy Workshops with University Students
Privacy Advocacy Workshops with Activists
Public Forum on Privacy and Progress Report Seminars
Security Measure and Privacy Policy Infographics
Report on Online Privacy Situation in Thailand
7.17. University of Hong Kong, Hong Kong
http://www.law.hku.hk/
7.17.1. Organisational overview
This project will be conducted under the ambit of the Faculty of Law at the University of Hong
Kong, Hong Kong.
7.17.2. Personnel
Dr. Anne S.Y. Cheung is an associate professor at the Department of Law, University of Hong
Kong. She received her legal education at the University of Hong Kong (LL.B), University of
Toronto (JD), University of London (LL.M) and Stanford University (JSM, JSD). She specializes
in media law, internet issues on freedom of expression and privacy, socio-legal studies, the
study of domestic violence, childrens rights and feminist legal studies. In 2008, she was
awarded the Outstanding Young Researcher Award by the University of Hong Kong. She is the
co-Director of the Law and Technology Centre at the Faculty of Law, University of Hong Kong,
and a committee member of the Hong Kong Press Council. She will be working with her
research assistant, and her research networks in Macau, Taiwan and Mainland China.
7.17.3. Project summary
Given the unique and difficult position of tight political control but fast economic development
in China, this project will comprise a focused analysis of the country, with two areas of
concentration. The first will be a comparative study of personal data protection in Hong Kong,
Macau, Taiwan and China (Greater China), analysing and evaluating the protection of privacy in
national laws, practices and codes, especially measures taken by various sectors in the
absence of binding law. This will represent a continuation of the work conducted under the
Privacy in Asia project since 2009, and will represent the first kind of comparative legal study in
the area.
The second area of focus for the project will be the delicate balance between personal data
protection and security in China. China has a notorious reputation as an authoritarian state,
where tight security control is often imposed in the name of social harmony. Massive personal
data from the population is also collected in the pretext of social harmony and security. Yet,
how much of this emphasis on social harmony proves convincing?
7.17.4. Objectives
Issue 1
a) To map out the legal regulations in the four regions;
b) To analyze and evaluate the protection and enforcement of personal data legislation;
c) To identify the gaps in existing law or to identify the specific areas in personal data that are
in need of legal protection; and
d) To compare legal models and to establish which are more effective in promoting personal
data protection given the various social constraints.
Issue 2
a) To reveal cases of privacy violations in the name of security by the government, with
particular attention on various real name identity measures implemented by the authorities;
b) To delineate the legitimate security concerns from their pretext;
c) To identify the gap between stated personal data protection policy and practice/violations
by the government itself; and
d) To analyze how these cases were covered by the public, so that public opinion may act as a
critical voice in an authoritarian state.
7.17.5. Expected outcomes
a) The production of solid research that can advance future law-making in places that are yet
to have national law;
b) Legal reform and amendment for places that already have the law in place;
c) Better informed policy makers; and
d) Advancement of academic and social discourses in personal data protection.
7.17.6. Project timeline, activities and outputs
Activities Year 1 Year 2
Q1 Q2 Q3 Q4 Q5 Q6 Q7 Q8
Mobilization of Research Team and
Coordination
Desk research/Literature Review
Policy Review and mapping
Organise Privacy Conferences
Drafting of Papers
Delivery of Findings: Conferences
7.17.7. Risks and limitations
The project does not expect to encounter any security risk, but may experience difficulties in
gathering primary materials, in which case secondary resources will be relied upon.
7.18. Voices for Interactive Choice and Empowerment, Bangladesh
http://www.voicebd.org/
7.18.1. Organisational overview
VOICE is a rights-based research and advocacy organization working mainly on human rights
issues: the right to information and communication justice, privacy rights and data protection,
aid effectiveness, economic justice, and food sovereignty, both in Bangladesh and on a global
scale. By building a broader constituency of alternative voices to the mainstream development
discourse through research and public education, VOICE takes a stand against unjust and
undemocratic practices. VOICE coordinates a number of national networks and is also member
of the executive committees of different national and international networking organisations
including Campaign for Good Governance.
7.18.2. Personnel
The project team will consist of four members working full time on the project for two years,
while Accounts and Admin departments will provide regular support. The team will consist of a
Project Head, a Research Coordinator, a Campaign and Advocacy Coordinator, and a
Networking and Media Associate.
7.18.3. Project summary
The recent development of information technology has expanded the scope of communication
but has also created serious threats to personal privacy all over the world. During the last
decade and a half, electronic communication in Bangladesh has evolved considerably. VOICEs
previous research under the Privacy in Asia project found that a significant number of
Bangladeshis want a data privacy law and a privacy commission in order to ensure everyones
right to privacy. In addition, CSOs have called on the government to enact a privacy and data
protection laws to secure privacy rights and personal data. There remains a strong need to
continue pressing these issues in the Bangladeshi public discourse. Accordingly, this project
aims to undertake a detailed analysis of communication surveillance mechanisms, political
intelligence and the state of data protection in Bangladesh in order to influence policy-makers
with evidence-based research for positive steps to ensure rights.
7.18.4. Objectives
a) To understand laws, regulations, practices and safeguards relating to privacy, surveillance
and human rights;
b) To analyse the design and operation of different communications regimes, to socialize norms
of privacy in communications and advocate for legislative and regulatory protections in
communications systems;
c) To uncover the nature and operation of local intelligence surveillance services, and advocate
for the strengthening of oversight mechanisms;
d) To advocate for the adoption, strengthening and implementation of privacy and data
protection frameworks; and to monitor and evaluate the nature, effectiveness and level of the
measures of protecting privacy and data protection;
e) To increase critical awareness, enhance capacity and building networks in order to broaden
the constituency of stakeholders in policy campaigning and advocacy for data protection
and privacy rights; and
f) To create a pressure group comprising CSO members, lawyers, security technology experts,
journalists, academics and other experts to lobby for policy-level changes that promote a
privacy friendly environment.
7.18.5. Expected outcomes
a) Regulatory and legal frameworks including human rights situation and practices will be
researched and documented, and a critical perspective built up through dissemination;
b) Nature and types of communications surveillance will be collated and disseminated, and
stakeholders understanding raised;
c) Surveillance practices and motivations will be illustrated through research, an oversight
mechanism put in place, and policy engagement strengthened;
d) Policy advocacy will be strengthened, cases of rights violations documented through proper
monitoring, political discourse advanced, and positive steps undertaken to promote data
privacy;
e) Critical awareness will be raised, stakeholders capacity increased, networks strengthened,
and advocacy and campaign engagement with the policy makers established; and
f) A strong demand will be raised collectively, advancing the political discourse for an
environment enabling data privacy rights
7.18.6. Project timeline, activities and outputs
7.18.7. Risks and limitations
The topic of privacy rights, especially regarding communication surveillance, is very sensitive due
to national security interests relating to this issue. There is a possibility that the government will
misunderstand the project objectives. In order to mitigate this risk, this project will engage
political leadership to advance the discourse and to advocate at policy level for peoples
demands and right to data protection and privacy. As the project will involve a wide range of
stakeholders, the project will receive acceptance from its initiation. The media will also be
interested in publicising an issue that may help build a broader constituency. In these ways, the
risk and limitations can be avoided.
Activity Year 1 Year 2
Q1 Q2 Q3 Q4 Q1 Q2 Q3 Q4
Campaign, networking and planning meeting
Multi-stakeholder consultation
Roundtable
National Convention
Network Building Meetings
Meeting for a national commission / committee
Lecture/debate
Press Briefing
TV Talk Show
Capacity building training/ workshop
Publication of the research report and dissemination
Perception polling / survey
Internship Program
Desk Research
Newsletter
Materials for consultations/ training workshop
7.19. Zimbabwe Human Rights Forum, Zimbabwe
http://www.hrforumzim.org/
7.19.1. Organisational overview
The Zimbabwe Human Rights NGO Forum (the Forum) has been in operation since 1998,
when human rights organisations joined together to assist the victims of the Food Riots of
January 1998. The Forum consists of 19 member organisations as of March 2012, each with
thematic specialties covering a broad spectrum of human rights concerns. The Forum's vision is
of a society free of organised violence and torture. It aims to reduce organised violence and
torture and to foster a culture of non-violence, tolerance and respect for human rights in
Zimbabwe, by producing accurately documented information for local, regional and international
advocacy and legal redress. The Forum operates out of a secretariat in Harare, and an
International Liaison Office (IntLO) in London.
7.19.2. Personnel
The project will be led by the Forums Executive Director Abel Chikomo, a media and legal
expert. Abel has wide knowledge on institutional reform issues, particularly in the security sector,
and has the political astuteness to engage policy makers both at local and international levels.
The day-to-day research will be conducted by Arthur Gwagwa, IntLO Coordinator, a dually
qualified legal practitioner and solicitor in Zimbabwe and England respectively. Arthur has more
than 10 years combined legal experience, seven of which were spent practicing both in
Zimbabwe and England, including litigation on article 8 of the ECHR. An experienced writer,
Arthur also carried out research on policy analysis as part of his Masters programme. Arthur will
work with Elizabeth Bishop, who has worked with the Forum for six years. Elizabeth holds
Masters in Governance and Development and has a strong background in research. The team
will benefit from a huge pool of researchers within the Forum and among its members, as well as
a network of experts in the third sector, academics and policy makers across the country.
7.19.3. Project summary
Currently, there is a broad debate in Zimbabwe on what steps should be taken to ensure that the
Zimbabwean security sector as a whole is non-partisan and operates within the Constitution and
the various pieces of enabling legislation governing it. Zimbabwe is notorious for political
intelligence surveillance, which is now governed by the Interception of Communications Act
2007. This Act grants the President the right to intercept any communications he considers
necessary to protect "the interests of national security or the maintenance of law and order". In
reality, the interception is carried out by the Presidents Office or the Central Intelligence
Organisation (CIO).
This project will involve conducting research on the current state of policy and practice on
intelligence oversight and communications surveillance on particular social groups within and
without Zimbabwe, usually perceived to be opposed to the Zimbabwean Government interests.
The objective is to uncover the nature and operation of local intelligence services and
communication surveillance, and advocate for the strengthening of oversight mechanisms, and
the adoption of national laws, regulations, practices and safeguards that comply with
international standards.
Given the rapid changes in communications, technology and the exchange and use of data in
emerging economies across the world, there seems to be an opening for further research on the
state of data protection in Zimbabwe, and on comparable regulatory standards and best
practices. The above is particularly true for Zimbabwe due its bilateral relations with both China
and North Korea, countries which are both known for their secrecy. The findings will help to
facilitate policy engagement efforts designed to encourage the adoption, strengthening and
implementation of data protection frameworks.
7.19.4. Objectives
a) To assess to what extent Zimbabwes national laws, regulations, practices and safeguards
relating to political intelligence oversight and communications surveillance adhere to the right
to privacy;
b) To evaluate the research gaps about how to bring current policy, legislative and practice
framework in line with international standards and norms, and to understand and compile
information about comparable regulatory standards and best practices;
c) To assess to what extent the current framework is being enforced;
d) To undertake targeted policy engagement with the objective of encouraging the adoption,
strengthening and implementation of frameworks and practices that adhere to international
norms.
7.19.5. Expected outcomes
a) Public awareness of individual rights raised and capacity of the civil society to advocate
for/exercise its rights enhanced;
b) Ensuring that the issue political intelligence oversight and communications surveillance in the
context of the right to privacy is mainstreamed in the legal, political and academic discourse
thus laying a foundation for further advocacy towards changes in law or policies and practice
in line with recommendations, leading to better protection of individuals from invasion of their
privacy;
c) Government officials particularly state security actors (police, prison guards and military
officials) are more sensitised on issues of privacy and more aware of internationally accepted
standards; and
d) Law officials (including lawyers, prosecutors, judges, magistrates) doctors and specialized
NGOs are more aware of international standards relating to invasion of privacy, remedies
and mechanisms available and of how to document and take up and adjudicate on such
cases.
7.19.6. Project timeline, activities and outputs
7.19.7. Risks and limitations
a) General lack of engagement of by stakeholders especially in the civil society due to pre-
Activity Year 1 Year 2
Q1 Q2 Q3 Q4 Q1 Q2 Q3 Q4
Scoping, identifying issues, stakeholders, refining research
etc
Develop an agreed research plan with the support of the
research team.
Attend IP research training courses, undertake significant
research on topic, conduct a comprehensive literature
survey and prepare some draft chapters of the main Report
Interviews with legal experts
Consultations with other groups including civil society,
regional and international experts, security and industrial
experts, grassroots.
Writing draft chapters of the research (1
st
report),
Implementing reviews and comments and collecting
outstanding research materials. We will revise and submit
the final report and do all necessary advocacy and policy
engagement
occupation with competing interests in an election year as well as refusal by officials to
participate in trainings.
Mitigation: The Forum will use its already established networks and goodwill of its partners.
b) Increasing security threats in election year may prevent movement or activities taking place.
Mitigation: there will be a continued engagement between PI and the Forum and its member
organisations involved in implementing activities to assess this risk and make alternative
arrangements.
c) Lack of well documented and consolidated resources on Zimbabwe security, political
surveillance and privacy law and practice thus frustrating research efforts.
Mitigation: The Forum will use an established network of academic institutions and the
Zimbabwean Bar and where gaps in research are identified, the Forum will undertake
empirical research.
You might also like
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Grade 10 Music 3rd QuarterDocument56 pagesGrade 10 Music 3rd QuarterHannah Bienne Lucas Bagsic70% (10)
- November 2014 (v2) MS - Paper 1 CIE Biology A-LevelDocument2 pagesNovember 2014 (v2) MS - Paper 1 CIE Biology A-LevelEllieNo ratings yet
- Europe Language DayDocument8 pagesEurope Language DayLordi LunaNo ratings yet
- SLNB-2016-06 V.54 JuneDocument98 pagesSLNB-2016-06 V.54 JunePost Your FeedbackNo ratings yet
- LHE 3209 - Week 1 (Prac - Basics of Reading)Document29 pagesLHE 3209 - Week 1 (Prac - Basics of Reading)Xinyi MaNo ratings yet
- WBCS Preliminary Solved Question Paper 2017 PDFDocument33 pagesWBCS Preliminary Solved Question Paper 2017 PDFPartha Sarathi MannaNo ratings yet
- First Week Reflection - YALDocument1 pageFirst Week Reflection - YALAravinda PrasadNo ratings yet
- Attention - PGPM Students Project Report Format (At The End Term)Document4 pagesAttention - PGPM Students Project Report Format (At The End Term)tahseen25No ratings yet
- Jerry V Situmorang 2201111825 - English EssayDocument2 pagesJerry V Situmorang 2201111825 - English EssayJerry Vinsensius SitumorangNo ratings yet
- Additional LET Items: Foundations of EducationDocument61 pagesAdditional LET Items: Foundations of EducationRejie100% (1)
- Breaking The Relapse Cycle - FSM Research 2019Document70 pagesBreaking The Relapse Cycle - FSM Research 2019Marcelle BugreNo ratings yet
- GR 1 Term 4 2018 Maths Lesson Plan English OnlyDocument125 pagesGR 1 Term 4 2018 Maths Lesson Plan English OnlyGeraldineNo ratings yet
- Lesson 16 Personal Statement Andrea RDocument2 pagesLesson 16 Personal Statement Andrea Rapi-501679979No ratings yet
- MISAJON 11 at 12Document2 pagesMISAJON 11 at 12Jayson Bautista100% (3)
- TLE Department Action Plan 2017-2018Document10 pagesTLE Department Action Plan 2017-2018Alz Bakino Lpt100% (1)
- Cpar MidtermDocument3 pagesCpar MidtermIvy DiazNo ratings yet
- Lesson Plan in Book Review 6Document5 pagesLesson Plan in Book Review 6Yreech Eam100% (1)
- Lexicology I - HistoryDocument20 pagesLexicology I - HistoryCiatloș Diana ElenaNo ratings yet
- UMF Unit-Wide Lesson Plan TemplateDocument6 pagesUMF Unit-Wide Lesson Plan Templateapi-507784209No ratings yet
- Jude The Obscure Literature CardDocument3 pagesJude The Obscure Literature CardMadison Armer100% (1)
- Teaching Learning ProcessDocument40 pagesTeaching Learning ProcessTilarupa Bhattarai77% (30)
- Instructional MaterialsDocument24 pagesInstructional MaterialsDon Zian EncarnacionNo ratings yet
- Ed Ebreo - High Performance Team Leadership WorkshopDocument5 pagesEd Ebreo - High Performance Team Leadership WorkshopEdwin EbreoNo ratings yet
- "Social Change Impact Report Summary Report"-1 (Walden University) - SEP11Document7 pages"Social Change Impact Report Summary Report"-1 (Walden University) - SEP11retelurNo ratings yet
- Theory of International Relation 01Document12 pagesTheory of International Relation 01Kbass KolawoleNo ratings yet
- Understanding Indian CultureDocument16 pagesUnderstanding Indian CultureRavi Soni100% (1)
- Mossop 2011 Chapters 10 and 11 Andappendix 4Document29 pagesMossop 2011 Chapters 10 and 11 Andappendix 4Alban BeqiriNo ratings yet
- Development of Learner LanguageDocument3 pagesDevelopment of Learner LanguageRonalie JameloNo ratings yet
- Campus Journ ACTION PLAN 2017-18Document2 pagesCampus Journ ACTION PLAN 2017-18Christian Catajay100% (2)
- Strategic PR Plan: Rmit Vietnam UniversityDocument18 pagesStrategic PR Plan: Rmit Vietnam UniversityLavenderRoxyNo ratings yet