Professional Documents
Culture Documents
Random Graphs Re Factoring
Uploaded by
marciomuccillo0 ratings0% found this document useful (0 votes)
25 views4 pagesThis paper describes a random graph based model to represent an object oriented software system. The system is represented as a graph made of a set of nodes and arcs with given crossing probabilities. The model provides also the representation of the refactoring process as a random propagation through the graph.
Original Description:
Copyright
© Attribution Non-Commercial (BY-NC)
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis paper describes a random graph based model to represent an object oriented software system. The system is represented as a graph made of a set of nodes and arcs with given crossing probabilities. The model provides also the representation of the refactoring process as a random propagation through the graph.
Copyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
25 views4 pagesRandom Graphs Re Factoring
Uploaded by
marciomuccilloThis paper describes a random graph based model to represent an object oriented software system. The system is represented as a graph made of a set of nodes and arcs with given crossing probabilities. The model provides also the representation of the refactoring process as a random propagation through the graph.
Copyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 4
Modeling XP Refactoring Using Random Graphs
Michele Marchesi Giancarlo Succi Nicola Serra
DIEE Center for Applied Software Engineering DIEE
Università di Cagliari Free University of Bolzano-Bozen Università di Cagliari
Piazza d’Armi Piazza Domenicani 3 Piazza d’Armi
I-09123 Cagliari, Italy I-39100 Bolzano-Bozen, Italy I-09123 Cagliari, Italy
+39(070)675 5899 +39(0471)315-640 +39(070)675 5899
michele@diee.unica.it Giancarlo.Succi@unibz.it nicola.serra@diee.unica.it
ABSTRACT In the followings, we present our model, introduce sig-
This paper describes a random graph based model to nificant metrics built on it, and provide some results on
represent an object oriented software system. The system the application of the model to four large C++ projects
is represented as a graph made of a set of nodes and a set performed at a North American telecommunication com-
of arcs with given crossing probabilities. The model pany.
provides also the representation of the refactoring process
as a random propagation through the graph. 2 RANDOM GRAPHS
Random graphs theory was devised around ’60 by two
Empirical data taken by real software projects are used
mathematicians, Paul Erdos and Alfred Rèmyi [3], and it
for a first validation of the approach.
was developed during the last decade by researchers such
Keywords as Palmer [9] and Bollobas [2]. Random graphs theory
Refactoring, Random Graphs, Software Engineering. has been successfully applied to model systems charac-
terized by high level of complexity in different fields
1 INTRODUCTION such as biology, sociology, computer science.
Extreme Programming (XP) [1] succeeds where require-
According to Erdos and Rèmyi, a random graph can be
ments are constantly changing. In fact, response to
built starting from a set of n nodes without connections.
change is a kernel concept of XP approach. This means
Then, considering each possible couple of nodes, a con-
that during XP process a software system is constantly
nection is drown with probability p or nothing is done
evolving and it is subject to continuous modification.
with probability 1-p.
There are two kinds of system changes. The first is the
Starting from this simple definition Erdos and Rèmyi
incremental change, when functionality is gradually
demonstrated a number of proprieties. All proprieties are
added, producing temporary and intermediate releases.
given on almost all random graphs, meaning that the
The second is the evolutionary change, occurring when
probability the propriety is true approaches 1 as the num-
design and code are constantly revisited and simplified,
ber of nodes becomes large (n → ∞).
in the refactoring phase.
Two different formal definitions are possible [7]. In the
Understanding how a single modification affects the
first, a Complete Graph is defined as follows:
whole system may help in reducing the cost of the XP
development process and to make better usage of the Kn≡ {En , [n]}, where [n]≡ {1,2,..,3} is the Set of Nodes
team efforts. The model we introduce in this paper pro- and En≡ {(i,j) | i∈[n], j∈[n], i≠j} is the Complete Set of
vides a representation of software systems based on ran- Arcs. Given a Complete Graph Kn≡ {En , [n]}, a Random
dom graphs theory. The system is represented as a graph Graph is defined as follows:
made of nodes and arcs. A node is the representation of a
specific software entity – for instance, a class – and an Gn,m≡ {En,m , [n]}
arc is the representation of a specific relationship be- (1)
tween two software entities – for instance, inheritance. where En,m is a random subset of m arcs extracted from
Given a specific system, there is no randomness in its En .
structure, since the graph representing the system is per-
fectly determined. On the contrary, the evolution of a The second definition, called Independent Model, doesn’t
specific software system due to maintenance or refactor- need the definition of Complete Graph.
ing shows a random behaviour, and it may be modelled Given 0≤p≤1, the Independent Model is defined as fol-
as the growth process of a random graph. lows:
The way a change influences the whole system is com- Gn,p≡ {En,p , [n]}
puted as a fluid random propagation through the graph (2)
representing the system itself. The main hypothesis is
that the modification does not change the graph represen- where every possible arc ε∈En appears independently on
tation of the system, or modifies it in a negligible way. En,p with probability p.
Under this hypothesis, the impact of a modification can As the number of nodes become large, model Gn,m and
be computed on the system representation before the the independent model Gn,p become equivalent, and a
changing takes place.
150
specific propriety true on Gn,m is also true on Gn,p. Attribute Extends
Interface Calls
The previous definitions may be modified to adapt them
Uses
for representing a given real situation or focusing on
certain aspects. In our context, we are interested in repre- Instance
senting software systems and maintenance process. The Parameter
model we propose may be seen as a modification of Gn,m. Implements
According to definition (1), we define Gn,m starting from
the complete graph and then randomly selecting a m-
Each relationship is made of a Server node and a Client
subset of arcs. Let’s call our model Gn,m,p. To build Gn,m,p
node. Moreover, for each type of relationships it is de-
we start from a colored graph with nodes and arcs of
fined a crossing probability from server to client (Prob-
different types. Then, subgraphs of Gn,m itself are ran-
ToCLient) and a crossing probability from client to server
domly selected.
(ProbToServer).
A more practical way to look at the model, is to consider
For example, suppose ni to be the representation of a
it as a graph (not random) traversed by a random propa-
software module needing a refactoring action. The
gation process. According to this view, every arc is char-
Change action impact will propagate along an edge to
acterized by a propagation probability p. Starting from a
adjacent nodes with probability ProbToClient if ni is the
specific node, the propagation process may cross each arc
server node or with probability ProbToServer if ni is the
with probability p or stop with probability 1-p. Thus, the
client node of the relationship.
focus is on the process rather than on the static structure
of the graph. This approach isn’t new. A similar model Given a specific software system, its RG Model is made
has been successful adopted for representing an epidemi- of nodes and relationships connected according to the
ological virus propagation within a population or to de- rules described by RG Metamodel shown in Table 2.
scribe how computer viruses may infect computer nets
[8].
Table 2 – RG Relationships.
3 APPLYING THE MODEL TO THE RG Relationships Client Server
REPRESENTATION OF SOFTWARE
Contains Class Attribute
SYSTEMS: THE RG MODEL
Object oriented software systems are made of entities Interface Attribute
such as classes, methods, attributes, variables and rela- Method Attribute
tionship among such entities. For instance, a specific InnerClass Class Class
class is the super class of its subclasses, that is an inheri- Global Class
tance relationship exists between the superclass and its Function Class Method
subclass, or a specific method is related with the class it
Interface Method
belongs to. When a module within the system needs to be
Extends Class (subClass) Class (superClass)
changed or refactored, this could affect related modules
and entities. The way a change will affect the whole Interface Interface
system depends upon the kind of entity involved in refac- Calls Method (calling) Method (called)
toring or change and upon the kind of relationship this Uses Method Attribute
entity has with other software modules. If the change to Parameter Method Attribute
an entity affects another entity, this is in turn changed, Instance Attribute Class
and other entities related to it may be affected. Thus,
Implements Class Interface
refactoring may be seen as a random process, which
propagates across the software system.
We can represent a software system as a graph where a Let’s take a look at all possible configuration admitted by
specific kind of software module is represented by a an instance of RG Model.
specific type of node and a specific relationship between Class nodes may be connected with Class, Method, At-
software entities is represented by a specific type of edge. tribute, Global and Interface nodes. Two nodes of type
Let’s call our model RG Model. Class can be connected by relationships of type Inner-
An instance of RG Model is made of a set of nodes of 5 Class and/or relationships of type Extends. Extends rela-
different types, and a set of relationships between pairs of tionship represents inheritance, with the subclass as
nodes of 9 different types (Table 1). server node and the superclass as client node. InnerClass
implements inner class definition, with external class as
Table 1 – Types of Nodes and Relationship. client. A Class node may be connected to a Method node
Node Types Relationship Types through the Function relationships, that is a method be-
Global Contains longs to a class.
Class InnerClass Connections between Class and Attribute nodes are pro-
Method Function vided by Instance and/or Contains relationships. Instance
151
implements the relationship between an object and its model is that refactoring does not change, or changes in a
class, Contains implements the relationship between a negligible way, the structure of the graph. This may seem
class and its instance variables. Class nodes are related to quite a strong assumption, since refactoring precisely
Global nodes using InnerClass relationships and Inter- aims to restructure and simplify the program. However,
face nodes are related with Class nodes by Implements our hypothesis is that most part of refactoring is made
relationships. working on the existing structure of the program, and that
the work on the changed structure does not introduce a
Nodes of type Method may be connected to nodes of type
substantial bias. Moreover, many refactoring are made on
Method, Class, Attribute and Interface.
methods, and are not likely to have impact on the graph
The Calls relationship provides a representation of a call structure.
between two methods, where the called method is the
server node. Method nodes may be connected to Attribute
nodes through relationships of type Uses, Parameter Table 3 – Probability values of crossing the arcs of the graph.
and/or Contains. Method nodes may also be connected to Relationships ProbToServer ProbToClient
Interface (or Class) nodes through Function relation- Contains 0.5 0.8
ships. All meanings should be clear. InnerClass 0.3 0.5
Two Interface nodes may be connected by Extends rela- Function 0.8 0.0
tionships, providing representation of inheritance be- Extends 0.2 0.9
tween interfaces. Interface nodes may connect Attribute Calls 0.2 0.5
nodes through Contains relationships. Uses 0.2 0.0
The RG Model provides a static view of the system, that Parameter 0.0 0.5
is the representation of all entities and relationships Instance 0.1 0.8
within an object oriented software system. Obviously, Implements 0.2 0.8
given a specific system, there is no randomness in its
graphic representation, since all entities and relationships
within the system are well determined. However, the set Three different types of metrics have been defined:
of all (existing and potential) software systems may be
Cost, related to the total number of lines of code
modeled as a random graph, characterized by defined
(LOC) involved in propagation;
distributions of the class, methods, attributes etc. [5].
Marks, related to the total number of visited nodes;
4 THE DYNAMIC VIEW: RG VISITS AND RG
Visits, integrating Marks metric over all existing
METRICS.
Class nodes.
Maintenance and refactoring are dynamic activities
which start from a specific software entity and affect Each visit is independently run a large number of times,
other parts of the system, accordingly to the type of starting from every class node of the graph. Starting from
refactored entity and to the type of relationship this entity a Class node and propagating across adjacent arcs, Cost
has with other entities. metric accounts for the total number of lines of code
(LOC) involved in propagation. Similarly, starting from a
The way a change could affect the whole system has a
Class node and propagating across adjacent arcs, Marks
random nature. Given the graph representation of a soft-
metric accounts for of how many nodes are touched dur-
ware system, maintenance and refactoring (which from
ing propagation. Visits metric is quite different, and it
now on we’ll simply call “refactoring”) may be thought
provides a more global meaning. It records how many
as a random propagation process, which starts from the
times a specific node is touched after a set of visits has
first node, typically a Class node, representing the soft-
been performed, starting from all the existing Class
ware module needing a change, and propagates according
nodes.
to given probability values across the whole graph.
In our approach, refactoring is simulated with a visit to 5 RESULTS AND CONCLUSIONS
the graph. The visit starts from a specific Class node and To validate the RG Model, we developed an application
propagate randomly to adjacent nodes according to cer- able to build the graph representation of a generic soft-
tain probability values defined for each type of crossed ware system and to compute the three defined metrics.
relationship (Table 3). These values are based on pro- We used this application to build the RG Model and
grammers’ empirical experience and have been devised simulate all the visits on five large C++ projects devel-
interviewing a number of programmers and averaging oped by a North American telecommunication company.
their answers. To avoid unending propagation of the Table 4 shows the number of nodes and relationships of
visits through the graph, a fading coefficient has been different types for each project. Note that no Interface
defined. It is a multiplicative factor smaller than one, nodes and no Implements relationships have been found
which decreases the probabilities of propagation as long by the application, according to the fact that all projects
as the propagation itself is running. were developed using C++ language. For each project,
the number of maintenance interventions per file, and
As already pointed out, the underlying hypothesis of the
152
some classical metrics (LOC, CK) were known. Our only between RG Metric and revisions, but also between
intention was to find a correlation between defects and RG Metrics and LOC.
RG Metrics. Thus, all possible visits have been computed
for each project, producing a large amount of data.
Table 5 – Spearman correlation coefficient between three projects and
Since data about revisions and data about RG Metrics do the proposed metrics.
not show normal distribution – as usually happens on
software data [4] – we couldn’t use the traditional Pear- Rg metrics Correlation Project#1 Project#2 Project#3
son coefficient. Cost Spearman 0.505 0.460 0.588
Significance 0.000 0.000 0.000
Visits Spearman 0.185 0.293 -0.052
Table 4- Nodes and arcs in the five considered projects. Significance 0.001 0.000 0.717
Proj. 1 Proj. 2 Proj. 3 Proj. 4 Proj. 5 Marks Spearman 0.048 0.369 0.383
Global 851 888 516 1065 544 Significance 0.396 0.000 0.006
Class 2093 2523 1217 2641 1721
Attribute 25507 28739 13761 22524 17864 Table 5 shows that Cost metric is the best correlated with
Method 19395 15333 9961 19572 9724
Interface 0 0 0 0 0 the number of revisions, having also perfect significance.
Contains 38784 49154 20986 40398 30534
InnerClass 4278 5046 2434 5268 3442 More experiments are obviously needed to be more de-
Extends 2074 1274 536 1714 558 finitive. The main problem remains the difficulty to find
Function 42022 30798 19814 39462 19492 software with good documentation about refactoring,
Calls 27901 20830 9588 10475 11032 which should allow to perform significant statistical
Uses 70572 65106 37594 34406 29158
analysis.
Instance 14186 10846 4382 8524 6692 However, the obtained results are encouraging about the
Parameter 9668 6334 4996 5282 3456 usefulness of our model.
Implements 0 0 0 0 0
1.1 REFERENCES
1. Beck K., Extreme Programming Explained, Addison-
For this reason, to correlate the number of revisions with
Wesley, 1999.
RG Metrics, we adopted the Spearman robust correlation
2. Bollobas B., Random Graphs, Academic Press, London,
coefficient [6]:
1985
n 3. Erdos E. e Rèmyi A., On the evolution of random graphs,
¦ di 2 Magyar Tud. Akad. Mat. Kut. Int. Kzl.5, 1960
i =1
rs = 1 − 6 ⋅ 4. Fenton N. E. e Pfleeger S. L., Software Metrics, A Rigor-
n ⋅ ( n 2 − 1) ous & Practical Approach, Second Edition, PWS Publish-
(3) ing Company, Boston, MA, 1997
5. Focardi S.,Marchesi M., Succi G., A Stocastic Madel of
Given n samples, Xi and Yi, in ascending order, Spearman Software Maintenance and its Implication on Extreme Pro-
correlation is computed as shown in (3), where di= Xi-Yi. gramming Proccess, Extreme ProgrammingExamined, Ad-
dison Wesley, 2001.
The computation of the correlation coefficient is fol-
6. Frund J.E. e Simon G.A, Modern Elementary Statistics,
lowed by a test of significance. Significance is the chance Prentice-Hall, Upper Saddle River, NJ, 1997
of correlation value not being true [10].
7. Janson S., Random Graph,
Table 5 shows that a correlation seems to exist. However, http://www.math.uu.se/~svante/papers/sjb4.ps, 2000
we have to be careful. As it usually happens in software 8. Kephard J. O. e White S. R., Directed-Graph Epidemiol-
engineering experiments, our data were incomplete and ogical Models of Computer Viruses, online at:
rough. The main problem is that the number of revisions http://researchweb.watson.ibm.com/antivirus/SciPapers/Ke
for each project is given for files – not for classes. To phart/VIRIEEE/virieee.gopher.html
compute defects per class we accounted for the number 9. Palmer E.M., Graphical evolution. An introduction to the
theory of random graphs, Wiley, 1985.
of lines of code per class within the file. This means that
the numbers in table 5 accounts for the correlation not 10. Wonnacott T.H. and Wonnacott R.J, Introductory Statistic,
John Wiley & Sons, New York, 1997.
153
You might also like
- NN AND DEEP LEARNING INSIGHTSDocument82 pagesNN AND DEEP LEARNING INSIGHTSMario CordinaNo ratings yet
- Algorithmic Information Theory: G. J. ChaitinDocument10 pagesAlgorithmic Information Theory: G. J. ChaitinEAPNo ratings yet
- ManpreetDocument3 pagesManpreetSurya KantNo ratings yet
- Liao and Smidt - 2022 - Equiformer Equivariant Graph Attention TransformerDocument25 pagesLiao and Smidt - 2022 - Equiformer Equivariant Graph Attention Transformer1045013245leoNo ratings yet
- Two Hardware Implementations For Modular Multip - 2021 - Journal of InformationDocument12 pagesTwo Hardware Implementations For Modular Multip - 2021 - Journal of Informationnosofo4431No ratings yet
- Rethinking Modular Multi-Exponentiation AlgorithmsDocument15 pagesRethinking Modular Multi-Exponentiation Algorithmsfsd fsdfdsNo ratings yet
- Offline Arabic Handwriting Recognition With MultidDocument9 pagesOffline Arabic Handwriting Recognition With MultidHaladr KhaldiNo ratings yet
- A Performance Comparison of Recent Network Simulators: Elias Weing Artner, Hendrik Vom Lehn and Klaus WehrleDocument5 pagesA Performance Comparison of Recent Network Simulators: Elias Weing Artner, Hendrik Vom Lehn and Klaus WehrleAdnan ShaukatNo ratings yet
- Proving The: MultiprocessDocument19 pagesProving The: MultiprocesssatyamkumarmodNo ratings yet
- Attention Is All You Need 1hodz0wcqbDocument11 pagesAttention Is All You Need 1hodz0wcqbAbhishek JunghareNo ratings yet
- Attention Is All You NeedDocument11 pagesAttention Is All You NeedSaniyah Mushtaq100% (1)
- Attention Is All You Need Paper - RemovedDocument9 pagesAttention Is All You Need Paper - RemovedfhghNo ratings yet
- Approx - Multiplierusing NNDocument12 pagesApprox - Multiplierusing NNSelva KumarNo ratings yet
- PARALLEL NEURAL NETWORK FOR HANDWRITING RECOGNITIONDocument6 pagesPARALLEL NEURAL NETWORK FOR HANDWRITING RECOGNITIONDavid TodorovNo ratings yet
- Narang 2013Document5 pagesNarang 2013Geyson MaquineNo ratings yet
- Lecture 1-4: 1. Design PhilosophyDocument7 pagesLecture 1-4: 1. Design PhilosophyrajawidadiNo ratings yet
- Convolutional Knowledge Graph EmbeddingsDocument8 pagesConvolutional Knowledge Graph Embeddingsphanpeter_492No ratings yet
- Project ReportDocument13 pagesProject ReportMonica CocutNo ratings yet
- Bare Conf4Document5 pagesBare Conf4asd asdasNo ratings yet
- Deng 17 ADocument10 pagesDeng 17 ADante NoguezNo ratings yet
- Towards The Emulation of Symmetric EncryptionDocument7 pagesTowards The Emulation of Symmetric Encryptionreal personNo ratings yet
- Image Classification Using CNN: Page - 1Document13 pagesImage Classification Using CNN: Page - 1BhanuprakashNo ratings yet
- DCN FileDocument7 pagesDCN Filekarieshma sharrmaNo ratings yet
- ParallelDocument10 pagesParallelrocky saikiaNo ratings yet
- IJETR021595Document6 pagesIJETR021595erpublicationNo ratings yet
- A Theory of Generic InterpretersDocument14 pagesA Theory of Generic InterpretersAnderson VasquesNo ratings yet
- Lu DeepONet NMachineIntell21Document15 pagesLu DeepONet NMachineIntell21Amartya RoyNo ratings yet
- Towards Proof Synthesis Guided by Neural Machine Translation For Intuitionistic Propositional LogicDocument19 pagesTowards Proof Synthesis Guided by Neural Machine Translation For Intuitionistic Propositional LogicSmail SmartNo ratings yet
- NS Lab ManualDocument11 pagesNS Lab ManualBonny PrajapatiNo ratings yet
- Systolic-Based 2D Convolver For CNN in FPGA: October 2017Document8 pagesSystolic-Based 2D Convolver For CNN in FPGA: October 2017Daniel AryaNo ratings yet
- Beating C in Scientific Computing with LISP PerformanceDocument12 pagesBeating C in Scientific Computing with LISP PerformancecluxNo ratings yet
- Signal Processing With Pulse Trains: An Algebraic Approach-Part IDocument11 pagesSignal Processing With Pulse Trains: An Algebraic Approach-Part IgabrielnallathNo ratings yet
- Redes IndustrialesDocument11 pagesRedes IndustrialeskagantsNo ratings yet
- E3nn Euclidean Neural NetworksDocument22 pagesE3nn Euclidean Neural Networksmohammed ezzatNo ratings yet
- A Combined Neural Network/Gaussian Process Regression Time Series Forecasting System For The NN3 CompetitionDocument5 pagesA Combined Neural Network/Gaussian Process Regression Time Series Forecasting System For The NN3 CompetitionThomas TseNo ratings yet
- Quadratic I Ee Etc 0305Document16 pagesQuadratic I Ee Etc 0305FlorinNo ratings yet
- Neural Networks Are Multi-Layer Networks of Neurons That We Use To Classify Things, Make Predictions, EtcDocument4 pagesNeural Networks Are Multi-Layer Networks of Neurons That We Use To Classify Things, Make Predictions, EtcanshNo ratings yet
- Unit - 2 _ Mathematical Preliminaries for Lossless Compression ModelsDocument12 pagesUnit - 2 _ Mathematical Preliminaries for Lossless Compression ModelsJanvi PatelNo ratings yet
- Luo Etal Cvpr16Document9 pagesLuo Etal Cvpr16Chulbul PandeyNo ratings yet
- TSK Fuzzy Function ApproximatorsDocument11 pagesTSK Fuzzy Function ApproximatorsAdam KliberNo ratings yet
- Real-Time Convolutional Neural Networks For Emotion and Gender ClassificationDocument5 pagesReal-Time Convolutional Neural Networks For Emotion and Gender ClassificationDivyank PandeyNo ratings yet
- Software Cost Estimation Through Entity Relationship Model: AbstractDocument5 pagesSoftware Cost Estimation Through Entity Relationship Model: AbstractSyed Shah MuhammadNo ratings yet
- Character Recognition Using Neural Networks: Rókus Arnold, Póth MiklósDocument4 pagesCharacter Recognition Using Neural Networks: Rókus Arnold, Póth MiklósSharath JagannathanNo ratings yet
- Approximate Analysis of A Fault-Tolerant Join-The-Shortest-Queue PolicyDocument5 pagesApproximate Analysis of A Fault-Tolerant Join-The-Shortest-Queue PolicyssfofoNo ratings yet
- Fuzzy Software Cost Estimation Using Particle Swarm OptimizationDocument12 pagesFuzzy Software Cost Estimation Using Particle Swarm OptimizationnguyendattdhNo ratings yet
- Program LDocument20 pagesProgram LMasci MerouaniNo ratings yet
- Kfvsexp Final LaviolaDocument8 pagesKfvsexp Final LaviolaMila ApriliyantiNo ratings yet
- Signal Correlation Prediction Using Convolutional Neural NetworksDocument12 pagesSignal Correlation Prediction Using Convolutional Neural NetworksWesley BecariNo ratings yet
- Deep ONetDocument22 pagesDeep ONet梁帅哲No ratings yet
- Accuracy of Pre-Tender Building CostDocument17 pagesAccuracy of Pre-Tender Building CostJinhan KimNo ratings yet
- Computational GraphDocument17 pagesComputational GraphRam MurthyNo ratings yet
- Guo Generating Diverse and CVPR 2022 SupplementalDocument9 pagesGuo Generating Diverse and CVPR 2022 SupplementalMohanKrishnaNo ratings yet
- An Introductory Tutorial On Stochastic Linear Programming ModelsDocument30 pagesAn Introductory Tutorial On Stochastic Linear Programming ModelsGetnet MeleseNo ratings yet
- Cavin 02 AccuracyaDocument6 pagesCavin 02 Accuracyatườngt_14No ratings yet
- Image Classification Using Small Convolutional Neural NetworkDocument5 pagesImage Classification Using Small Convolutional Neural NetworkKompruch BenjaputharakNo ratings yet
- Polynomial Expansion PaperDocument4 pagesPolynomial Expansion PaperSrividyaGanapathiNo ratings yet
- Project Report: Optical Character Recognition Using Artificial Neural NetworkDocument9 pagesProject Report: Optical Character Recognition Using Artificial Neural NetworkRichard JamesNo ratings yet
- IET Electronics Letters TemplateDocument3 pagesIET Electronics Letters TemplateVerdi bobNo ratings yet
- Presentacion Arturo CalleDocument43 pagesPresentacion Arturo CalleNavarro JissellyNo ratings yet
- Java All GTU Programs 06012015 051359AMDocument23 pagesJava All GTU Programs 06012015 051359AMRohitNo ratings yet
- Django - StudentDocument18 pagesDjango - StudentPraveen GuptaNo ratings yet
- How to write a project synopsisDocument2 pagesHow to write a project synopsismohit pandeyNo ratings yet
- Bài Tập Phần Project ManagementDocument11 pagesBài Tập Phần Project ManagementhunfgNo ratings yet
- Blue Eyes Technology IEEE+FORMATDocument18 pagesBlue Eyes Technology IEEE+FORMATBalaji King100% (2)
- Create 3d Printing Website To Make MoneyDocument13 pagesCreate 3d Printing Website To Make MoneyIvan DerežićNo ratings yet
- Week 5 Lecture MaterialDocument97 pagesWeek 5 Lecture MaterialSmita Chavan KhairnarNo ratings yet
- ML Studio OverviewDocument1 pageML Studio OverviewFulga BogdanNo ratings yet
- GA-8S661FXM Schematics OverviewDocument34 pagesGA-8S661FXM Schematics Overviewtemp001No ratings yet
- Programming Logic and Design, 9th Edition. Chapter 1Document19 pagesProgramming Logic and Design, 9th Edition. Chapter 1John0% (3)
- Uniden User GuidesDocument1,059 pagesUniden User GuidesSensameaNo ratings yet
- Decision TreeDocument4 pagesDecision TreeGurushantha DoddamaniNo ratings yet
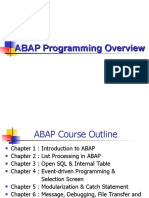
- ABAP Programming OverviewDocument393 pagesABAP Programming OverviewDuy SơnNo ratings yet
- Introduction To Software Reverse Engineering With Ghidra Session 1Document58 pagesIntroduction To Software Reverse Engineering With Ghidra Session 1Chancemille RemoNo ratings yet
- Flowcode ReportDocument2 pagesFlowcode ReportEdward LeeNo ratings yet
- SQL Server add-on services overviewDocument3 pagesSQL Server add-on services overviewShilpa SulekhNo ratings yet
- Android Development For C# and Visual Studio 2012Document2 pagesAndroid Development For C# and Visual Studio 2012johnvhorcajoNo ratings yet
- Instructions For Authors of SBC Conferences Papers and AbstractsDocument4 pagesInstructions For Authors of SBC Conferences Papers and AbstractsWill MakenzyNo ratings yet
- First Generation of Hmi Catalog enDocument20 pagesFirst Generation of Hmi Catalog enMadhun SickNo ratings yet
- Chegg: StudyDocument3 pagesChegg: StudyAbdullah MalikNo ratings yet
- 1 PDFDocument3 pages1 PDFAnurag KumarNo ratings yet
- 3c Terraform TLS ProviderDocument4 pages3c Terraform TLS ProviderEyad ZaenNo ratings yet
- Designing Combinational Logic Circuits in Verilog - 2Document32 pagesDesigning Combinational Logic Circuits in Verilog - 2Vinh Hoang XuanNo ratings yet
- Aspect Unified Ip 7.3 DsDocument2 pagesAspect Unified Ip 7.3 DsalexNo ratings yet
- How To Connect To MySQL Using PHPDocument3 pagesHow To Connect To MySQL Using PHPSsekabira DavidNo ratings yet
- Homework Assignment #3Document2 pagesHomework Assignment #3Erik VigoritoNo ratings yet
- AI Technologies Transform Military OperationsDocument20 pagesAI Technologies Transform Military OperationsKady YadavNo ratings yet
- Proyecto ICARO TestCaseDocument20 pagesProyecto ICARO TestCasePol MorenoNo ratings yet
- MRP Process in SAPDocument3 pagesMRP Process in SAPAarav ChoudharyNo ratings yet