Professional Documents
Culture Documents
Security Code Review-Identifying Web Vulnerabilities: Kiran Maraju, CISSP, CEH, ITIL, SCJP
Uploaded by
Sanjay PrajapatiOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Security Code Review-Identifying Web Vulnerabilities: Kiran Maraju, CISSP, CEH, ITIL, SCJP
Uploaded by
Sanjay PrajapatiCopyright:
Available Formats
Security Code Review- Identifying Web Vulnerabilities
Kiran Maraju, CISSP, CEH, ITIL, SCJP
Email: Kiran_maraju@yahoo.com
Security Code Review- Identifying Web Vulnerabilities
1.1.1 Abstract
This paper gives an introduction of security code review inspections, and provides details about web application security vulnerabilities identification in the source code. This paper gives the details of the inspections to perform on the Java/J2EE source code. This paper explains the process of identifying vulnerable code and remediation details. This paper illustrates the specific locations of code flows to be checked to identify web application vulnerabilities.
1.1.2 Introduction
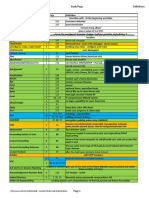
Security code review is to do code inspection to identify vulnerabilities in the code. Vulnerabilities in the code exist due to the improper design or implementation in SDLC Process life cycle while developing the application. JAVA/J2EE Security Code Review Inspection List Input Validation Unreleased resourceInspection Possible DOS inspection J2EE Resource injection Configuration Access Control Logging level Authentication inspection Inspection Access ControlConfiguration level Authorization inspection Inspection Session Sensitive data Implementation inspection inspection Class level Exception Management inspection inspection Object level Serialization inspection inspection Method level Synchronization/Threa Inspection d level inspection Variable/constan Cryptography t level inspection Inspection Inheritance EJB( Bean component Inspection Inspection )
Memory Reference Inspection Database access Inspection Computation/Numeric/Contro l Flow Inspection Network communication Inspection Web Container based Inspection I/O ( Input-Output ) Inspection File Level Inspection Native method Inspection Packaging level Inspection Inner classes/ reflection inspection
1.1.3 Input Validation Flaws
Input data requested from the client to server is not validated before being used by a web application. Attackers use the unvalidated input flaws to attack web server and backend components. Client-side validation like javascript and vbscript can be easily bypassed. Attackers use the vulnerable unvalidated input calls to be processed by server to execute the malicious content. Security code review involves identifying such unvalidated input calls and prevents those calls to be processed by the server. The following security code review checks are to be performed on tainted calls of servlet to identify unvalidated input from the attacker.
Checking for Unvalidated sources of input from URL parameters in javax.servlet.HttpServletRequest class getParameter () method
Checking for Unvalidated sources of input from Form fields in javax.servlet.HttpServletRequest class getQueryString () method Checking for Unvalidated sources of input from Cookies javax.servlet.HttpServletRequest class getCookies () method Checking for Unvalidated sources of input from HTTP headers javax.servlet.HttpServletRequest class getHeaders () method
Through the application, an attacker enters malicious data through HTML form of the input fields of the application. The following code is vulnerable because the application accepts the values provided by the client in an iterator and responds back to client with the attackers script which leads to reflected XSS vulnerability when the request.getParameteNames method was called. The following sample code illustrates the unvalidated input vulnerability.
Iterator iter = request.getParameterNames (); While (iter.hasNext ()) { String paramName = (String) iter.next (); out.println (paramName +request.getParameter (paramName)); }
Remediation: Unvalidated input vulnerabilities can be prevented either by accepting the valid data and rejecting every thing else such as creating whitelist of the legitimate input characters or cleaning the input or reject the entire input. Rejecting the input: The following code is used as whitelist input validation by accepting specific character patterns and rejecting everything else as a part of servlet request call
String input = request.getParameter ("input"); String characterPattern = "/ [^A-z]/"; If (! input. matches (characterPattern)) { out.println (Invalid Input); }
Cleaning the input: The following code is used as input validation by accepting the input and cleaning the malicious charcters by replacing with a space.
String filterPattern="[<> {}\\ [\\]; \\&]"; String inputStr = s.replaceAll (filterPattern," ");
1.1.4
Cross-Site Scripting Vulnerability
Cross-site scripting is an attack against web applications. It occurs when an web application accepts input containing malicious script through the application. This input is then sent as part of the response to the client as a reflected script which can lead to phishing attack, and the malicious script can be injected in the database as stored form so that whenever the page is accessed the injected script is executed like<Script> alert (document. cookie)</script> The following sample code illustrates the XSS vulnerability.
Iterator iter = request.getParameterNames (); While (iter.hasNext ()) { String paramName = (String) iter.next (); out.println (paramName +request.getParameter (paramName)); }
To prevent XSS attacks, it is important to focus on the areas where application code returns output to a user (client). It is important to identify calls that require output to be encoded. The code of the application replaces the special characters before displaying the output is also one of the remediation to xss vulnerability.
< > < >
( ( ) ) # # & &
The approach to preventing XSS attacks is encoding. Server-side encoding is a function in which scripting tags in all dynamic content can be replaced with codes in a chosen character set. For example, < and > becomes < and >. The J2EE , Struts and webworks frameworks support encoding.
1.1.5
Buffer Overflow Flaws
Lack of proper validation of input to the web components leads to buffer overflows. As Java is a Type safety language so overrunning the buffer is avoidable but Java based web applications can invoke native methods, libraries that are written in C and C++ using native calls. These native calls introduce vulnerabilities. To mitigate this vulnerability focus should be given on the areas where the Java Native Interface (JNI) API calls. All input passed to these calls should be validated to prevent an attacker from injecting malicious commands into the application. These JNI API calls should be reviewed to determine memory corruption does not take place which leads to buffer overflow. The following code illustrates JNI call in JSP which uses native TestDLL.dll using System.loadLibrary method.
Class JNICALL { public native String test (String name); static {System.loadLibrary ("TestDLL") ;} }
1.1.6
SQL Injection Flaws
SQL Queries and SQL Injection Attacks: SQL queries uses unvalidated user input as vulnerable script In an SQL injection attack, an attacker sends malicious input through the application interface like login page and these queries are executed in the backend database and attacker can gain control over a database or perform DOS attacks like Database shutdown. The following example illustrates JSP login form where the attacker can enter malicious commands like XP_cmdshell or *; OR 1=1 etc.
String Uname = request.getParameter (User); String Pword =request.getParameter (Password); String s = SELECT * FROM Table WHERE Username = + UName + AND Password = + Pword ; Statement stmt = connection.createStatement (); ResultSet rs = stmt.executeQuery (s); If (rs.next ()) { UID = rs.getInt (1) User = rs.getString (2) } PrintWriter writer= response.getWriter (); writer.println (User Name: + User); }
In the above example, the SQL query is created using the username and password transferred to the server without validating the input which is vulnerable to a SQL injection attack. To mitigate the risk of SQL injection is to use only stored procedures or parameterized database calls. Using prepared statement all the queries will be treated as a string but not commands to be executed by the database. The following code can be used as remediation for the above vulnerable code.
String s = SELECT * FROM Table WHERE Username = + UName + AND Password = + Pword ; PreparedStatement stmt = connnection.prepareStatement(s); stmt.setString (1, UName); stmt.setString (2, Pword);
ResultSet results = stmt.execute ();
1.1.7
Command Injection Attacks
Executing System/Operating System Commands through the application are the sources of Command Injection Attacks. Java has the provision to execute system commands with the Runtime. Exec () method. Improper validation of the exec method arguments leads to vulnerability in the source code and attacker can pass malicious commands through the exec argument and gain control of the system. The following sample code illustrates the Command injection vulnerability.
Class Execclass { public static void main (String args []) { Runtime rt = Runtime.getRuntime (); Process proc = rt.exec ("cmd.exe /C") ;} }
1.1.8
Improper Error/ Exception Handling
Improper error messages can reveal information about an application which may helps an attacker in exploiting the application. With the improper error handling detailed internal error messages such as stack traces, database dumps, exception and error details are displayed to the end user. printStackTrace () method reveals the application details and technology usage. The remediation for the improper error handling vulnerability is to redirect all the error messages to log file like using Log4j .The calls should be reviewed to determine whether the appropriate details are displayed to the user. All errors, exceptions, should be logged in log file instead of displaying directly to the end user. If the application shows the attacker a stack trace, it gives technology details. This information will enable the attacker to target known vulnerabilities in these components. A web application must be configured with a default error page. Whenever an exception comes the events should be logged to the log file and default error page should be displayed to the end user. The following example shows the improper error handling vulnerability in the code
try {} catch (ArrayIndexOutOfBoundsException e) { System.out.println ("exception: " + e.getMessage ()); e.printStackTrace (); }
The web.xml should include at least the following entries:
<Error-page> <exception-type>java.lang.Throwable</exception-type> <location>/error.jsp</location> </error-page> <Error-page> <error-code>500</error-code> <location>/error.jsp</location> </error-page>
1.1.9 Improper Access control
Improper assignment of restrictions on the privileges of authenticated users is allowed to leads to improper access control flaws. Attackers can exploit these flaws to access other users' accounts, view sensitive files, or use unauthorized functions. Improper Access Control vulnerabilities are identified by inspecting declarative and programmatic access control of J2EE applications.
Declarative deployment descriptor specifies restriction of users, beans and methods at the deployment descriptor level.
Programmatic access control can query identity of the user to verify privileges of user or business logic in the Bean program.
J2EE Access control Security covers both web-tier and EJB-tiers. At Web-tier, the access control is performed on resources which are represented in the form of an URL and at EJB-tier the access control can be applied on business methods of a bean in the application. Web-tier container enforces security policy specified in web.xml deployment descriptor and EJB container will enforce security policy specified in ejb-jar.xml deployment descriptor. Web-tier Declarative Access Control: Web-tier declarative access control applied in web.xml, by defining the security constraint applies to which application resources. The <url-pattern> element inside the <web-resource-collection> element provides restricted access to URLs. The <url-pattern> can refer to a directory, filename, or a <servlet-mapping>. The web-resource-collection element designates the access to which URLs should be restricted the auth-constraint element in web.xml specifies roles that should have access to the given URLs in url-pattern element.
<Security-constraint> <Web-resource-collection> <web-resource-name>admin pages</web-resource-name> <url-pattern>/admin/*</url-pattern> </web-resource-collection> <Auth-constraint> <role-name>administrator</role-name> <role-name>Normal user</role-name> </auth-constraint> </security-constraint>
EJB-tier Declarative Access Control: EJB components provide declarative access control with the elements defined in the ejb-jar.xml deploy descriptor. Security Roles are defined in ejb-jar.xml
<Enterprise-beans> <Security-role> <role-name>administrator</role-name> </security-role> <Security-role> <role-name> Normal user </role-name> </security-role> </enterprise-beans>
EJB-Tier Programmatic access control: EJB-Tier Programmatic access control can be implemented in the code of the Bean logic of the application. It can be implemented with the isCallerInRole () and getCallerPrincipal () methods. GetCallerPrincipal method is used to find out by whom the bean method is called and isCallerInRole method is used to check whether the caller of the application belongs to privileged role.
Public interface javax.ejb.EJBContext { Public java.security.Principal getCallerPrincipal (); Public Boolean isCallerInRole (String role); }
1.1.10 Improper Authentication Flaws
Improper assignment of account credentials and session tokens leads to Improper authentication vulnerability. Attackers can compromise passwords, session cookies and other tokens to bypass authentication. Vulnerabilities exist in the areas of weak credentials for authentication usage, unencrypted credentials and inefficient session usage. These vulnerabilities leads to privilege escalation attacks. These mechanisms must be reviewed to ensure proper implementation. Web-Tier Authentication: Authenticating users in web-tier application can be implemented in the following options.
Form
Basic DIGEST
Form-Based Authentication: Form based Authentication can be used in implementation by defining FORM in the <auth-method> element of web.xml. Using this application can use form login page login.jsp as shown in below. <
<Login-config> <auth-method>FORM</auth-method> <Form-login-config> <form-login-page>login.jsp</form-login-page> </form-login-config> </login-config>
BASIC Authentication: Form based Authentication can be used in implementation by defining FORM in the <auth-method> element of web.xml. Using this application can use authentication scheme provided by browser as shown in below.
<Login-config> <auth-method>BASIC</auth-method> <realm-name>Login</realm-name> </login-config>
EJB-Tier Authentication: Two Possible Authentication Schemes in J2EE User credential information passed to web-tier and forwards them for authentication at EJB- tier User credential information passed to web-tier and web-tier authenticates the user at Web-tier. Webtier then forwards the identity of a user to the EJB-tier.
1.1.11 Improper Session Management
Inspect the proper configurations for web.xml file for improper session management vulnerabilities. Inspect the Session Timeouts in the code. Session timeout can be checked in web.xml file. Using session. invalidate () to explicitly deactivate the sessions Session timeout can be using session.setMaxInactiveInterval ()
<Session-config> <Session-timeout> Time-in-minutes </session-timeout> </session-config>
1.1.12 Improper Cookie Management
Improper Cookie management leads to cookie poisoning and privilege escalation vulnerabilities in the application. The following vulnerable code set the cookie as persistent and stored in the local system for one hour.
Public class SetCookie extends HttpServlet { Public void doGet () { Cookie cookie = new Cookie ("Session Cookie + value); cookie.setMaxAge (3600); response.addCookie (cookie); }
The cookie values life time should be small time period and should be encrypted with efficient algorithms so that it cant be readable by anyone
1.1.13 Denial of Service
Denial of service vulnerability in the code can be identified in the areas where resource consumption or the places where attacker can disrupt the services to the legitimate users. Unreleased Resources causes Denial of Service vulnerability. Denial of service attacks cause a Web application to fail by causing the application to shut down or by consuming the available resources. Identify the calls like System.exit() to prevent from DOS. The exit method forces termination of all threads in the JVM which leads to the DOS for the legitimate user. The following program fails to release the database connection resource
Statement stmt = conn.createStatement (); ResultSet rs = stmt.executeQuery (); Stmt.close ();
The remediation for the above example is to release resources in a finally block. Never rely on finalize () to reclaim resources. If, the statement objects in the above program wont be closed frequently then the database will run out of available resources and not be able to execute any more SQL queries. The above vulnerable program can be rewritten as follows:
Statement stmt; Try { stmt = conn.createStatement (); stmt.executeQuery (); } Finally { If (stmt! = null) { Try { stmt.close (); } catch (SQLException e) { } } catch (SQLException e) { }
1.1.14 Improper Configuration Flaws
Proper server configuration is critical to a secure web application. The focus of the code review areas are from most common improper configuration vulnerabilities like Unpatched versions of the products, default files access, access to backup files, access to admin pages, using default accounts and passwords provided by vendor etc. Disabling the default servlet access: Url-pattern element in web.xml can disable the default servlet i.e. Invoking servlet.
<url-pattern>/servlet/*</url-pattern>
Disabling Unnecessary HTTP methods: Web-resource-collection in web.xml has http-method element that restricts the HTTP methods. The following shows the sample configuration of web.xml to disable PUT and DELETE HTTP methods.
<Security-constraint> <Web-resource-collection> <web-resource-name>Disallowed Location</web-resource-name> <url-pattern>/*</url-pattern> <http-method>PUT</http-method> <http-method>DELETE</http-method> </web-resource-collection> </security-constraint>
Restricting access to specific directory: Web-resource-collection in web.xml has an element to restrict access of the clients to specific directories. The following web.xml configuration shows data in the sensitive directory of the Web application should be protected.
1.1.15 Transport Level Flaws
<Security-constraint> <Web-resource-collection> <web-resource-name>Sensitive</web-resource-name> <url-pattern>/sensitive/*</url-pattern> </web-resource-collection> </security-constraint>
One of the element in deployment descriptor web.xml indicates which transport-level protections should be used when accessing the resources. Confidential invokes the use of SSL. For example, the following configuration shows the server to only permit HTTPS connections
<Security-constraint> <User-data-constraint> <transport-guarantee>CONFIDENTIAL</transport-guarantee> </user-data-constraint> </security-constraint>
Insecure transmission of secrets: Plain text transmission of secrets is critical vulnerability. Transmission of sensitive data should be done through encryption. By using HTTPS, using SSL encryption is the solution to protect sensitive web traffic.
1.1.16 Code Review Tools
Some of the Code Review Tools for JAVA/J2EE which can be used for security 1) Escjava URL: http://research.compaq.com/SRC/esc/download.html 2) Hammurapi URL: http://www.hammurapi.org/ 3) Jlint URL: http://www.willowriver.net/products/jlint.php 4) JavaPathFinder URL: http://javapathfinder.sourceforge.net/ 5) JavaPureCheck URL: http://java.sun.com/products/archive/100percent/4.1.1/index.html 6) Checkstyle URL: http://eclipse-cs.sourceforge.net/ 7) Pmd URL: http://sourceforge.net/projects/pmd 8) Findbugs URL: http://findbugs.sourceforge.net/
1.1.17 References
1) 2) 3) 4) http://www.owasp.org/documentation/topten.html ( www.owasp.org) http://www.javapassion.com/j2ee/EJBSecurity_speakernoted.pdf http://www.ouncelabs.com/audit/SoftwareSecurityAssuranceFramework.pdf The Dirty Dozen: The Top Web Application Vulnerabilities and How to Hunt Them Down at the Source ( www.ouncelabs.com ) 5) Controlling Web Application Behavior with web.xml http://developer.java.sun.com/developer/Books/javaserverpages/servlets_javaserver/servlets_java server05.pdf 6) Handling Java Web Application Input http://today.java.net/pub/a/today/2005/09/20/handling-web-app-input.html 8) http://www.owasp.org/index.php/Cryptography 7) Configuring Security in Web Applications http://e-docs.bea.com/wls/docs70/webapp/security.html 8) web.xml Deployment Descriptor Elements
9
http://e-docs.bea.com/wls/docs61/webapp/web_xml.html 9) http://www.javapractices.com/Topic86.cjp
10
You might also like
- Securing Application Deployment with Obfuscation and Code Signing: How to Create 3 Layers of Protection for .NET Release BuildFrom EverandSecuring Application Deployment with Obfuscation and Code Signing: How to Create 3 Layers of Protection for .NET Release BuildNo ratings yet
- Analyzing SQL Meta Characters and Preven PDFDocument4 pagesAnalyzing SQL Meta Characters and Preven PDFPramono PramonoNo ratings yet
- Practical Dynamic Taint Analysis For Countering Input Validation Attacks On Web ApplicationsDocument15 pagesPractical Dynamic Taint Analysis For Countering Input Validation Attacks On Web Applicationsthanga_sharmiNo ratings yet
- SQL InjectionDocument4 pagesSQL InjectionhutlokeshwaraNo ratings yet
- 19 WebSecurityThreats81Document81 pages19 WebSecurityThreats81Smita R. S.No ratings yet
- Detection of SQL Injection and Cross-Site Scripting AttacksDocument6 pagesDetection of SQL Injection and Cross-Site Scripting AttacksVũ TuấnNo ratings yet
- Running Head: Input Validation and Business Logic Security Controls 1Document6 pagesRunning Head: Input Validation and Business Logic Security Controls 1klm klmNo ratings yet
- Software Quality AssuranceDocument24 pagesSoftware Quality AssuranceSYED SUMAIR AHMED JAFFRINo ratings yet
- Quick Guide To SQL Injection Attacks and Defenses - EnglishDocument31 pagesQuick Guide To SQL Injection Attacks and Defenses - Englishsavafut007No ratings yet
- Software SecurityDocument17 pagesSoftware SecurityFajar IqbalNo ratings yet
- SQL Injection Methods & Patterns: Web SecurityDocument11 pagesSQL Injection Methods & Patterns: Web SecurityMeena RajendranNo ratings yet
- Assignment No 5 Vulnerability ManagementDocument19 pagesAssignment No 5 Vulnerability ManagementJusil T. GaiteNo ratings yet
- Chameli Devi Group of Institutions, Indore: CS-503 (C) Cyber Security Unit - VDocument10 pagesChameli Devi Group of Institutions, Indore: CS-503 (C) Cyber Security Unit - Vsignup onsitesNo ratings yet
- 01ieee Unit Testing - AcdDocument16 pages01ieee Unit Testing - AcdSanaNo ratings yet
- WAF Bypass Methods For BeginnerDocument20 pagesWAF Bypass Methods For BeginnerMostafaEl-sayedNo ratings yet
- Wvs Singles CanDocument1,007 pagesWvs Singles Canb1naryn1ghtmar3844No ratings yet
- Lectre 13Document6 pagesLectre 13AkRajNo ratings yet
- Vulnerabilities in Unit TestingDocument10 pagesVulnerabilities in Unit TestingLidio SantosNo ratings yet
- A Study On Removal Techniques of Cross-Site From Web ApplicationDocument7 pagesA Study On Removal Techniques of Cross-Site From Web ApplicationAdalberto FrancisNo ratings yet
- DEF CON 23 - Lance-Buttars-Nemus-Hacking-SQL-Injection-for-Remote-Code-Execution-on-a-LAMP-UPDATEDDocument96 pagesDEF CON 23 - Lance-Buttars-Nemus-Hacking-SQL-Injection-for-Remote-Code-Execution-on-a-LAMP-UPDATEDkashif majeed janjuaNo ratings yet
- CSRF Tokens: Cross Site Request ForgeryDocument3 pagesCSRF Tokens: Cross Site Request Forgeryzakaria mahzouliNo ratings yet
- Be LP3 Q2 41239 Ics MiniprojDocument10 pagesBe LP3 Q2 41239 Ics MiniprojWow BollywoodNo ratings yet
- SQL InjectionDocument37 pagesSQL InjectionShimelis AberaNo ratings yet
- JSP Vulnerabilities and Fixes For DevelopersDocument6 pagesJSP Vulnerabilities and Fixes For DevelopersabhijitchNo ratings yet
- Evidence Gathering System For Input Attacks: Deepak Singh Tomar, J.L.Rana and S.C.ShrivastavaDocument4 pagesEvidence Gathering System For Input Attacks: Deepak Singh Tomar, J.L.Rana and S.C.Shrivastavavol1no1No ratings yet
- SQL Injection - WikipediaDocument72 pagesSQL Injection - WikipediaVaibhav MajgaonkarNo ratings yet
- CSE 453 Problem Set 06: Exercises 05.03: C# and SQLDocument7 pagesCSE 453 Problem Set 06: Exercises 05.03: C# and SQLthomNo ratings yet
- 05563777(1)+++Document5 pages05563777(1)+++MhackSahuNo ratings yet
- Code InjectionDocument11 pagesCode InjectionJitendra RaiNo ratings yet
- Module 2 - Advanced Web Application Attacks and Remedy PDFDocument44 pagesModule 2 - Advanced Web Application Attacks and Remedy PDFMaster SharvNo ratings yet
- Project 3a Hacking Web Apps With Command Injections and Patching ThemDocument3 pagesProject 3a Hacking Web Apps With Command Injections and Patching Themmaylinpatydakin0% (1)
- Lab File (4) (It Security)Document26 pagesLab File (4) (It Security)pandeyjiiiiii995No ratings yet
- Reference 1 - 2017Document13 pagesReference 1 - 2017abenezer ketemaNo ratings yet
- ABSTRACTDocument1 pageABSTRACTImrannkhanNo ratings yet
- # Threats Where To Test Test NameDocument30 pages# Threats Where To Test Test NamegauravNo ratings yet
- Master Semminar Injection ExploitsDocument24 pagesMaster Semminar Injection ExploitsKarol StępniewskiNo ratings yet
- Create Attacks Icse2009Document11 pagesCreate Attacks Icse2009Cristine SmithNo ratings yet
- PMBDocument39 pagesPMBkartit0% (1)
- Rial Approach For Preventing SQLDocument6 pagesRial Approach For Preventing SQLShaik NooruddinNo ratings yet
- Infrastructure SecurityDocument107 pagesInfrastructure SecurityDoctor LyricsNo ratings yet
- SansaDocument10 pagesSansanntshali17No ratings yet
- Interview Preparation Part-1Document53 pagesInterview Preparation Part-1Abdul Mateen UkkundNo ratings yet
- Detection of SQL Injection Attack in Web Applications Using Web ServicesDocument8 pagesDetection of SQL Injection Attack in Web Applications Using Web ServicesInternational Organization of Scientific Research (IOSR)No ratings yet
- L28 - Security 1Document20 pagesL28 - Security 1C-dawgNo ratings yet
- Web Application Security VulnerabilitiesDocument5 pagesWeb Application Security VulnerabilitiesHailu TsegaNo ratings yet
- Routine Detection of Web Application Defence FlawsDocument5 pagesRoutine Detection of Web Application Defence FlawsijtetjournalNo ratings yet
- Adavanced Postgre SQL InjectionDocument15 pagesAdavanced Postgre SQL InjectionFelipe CostaNo ratings yet
- Abstract: Most of The Companies Nowadays Uses Websites To Run Their Operations As Well As StoreDocument7 pagesAbstract: Most of The Companies Nowadays Uses Websites To Run Their Operations As Well As StoreJohnson SneijderNo ratings yet
- SQL InjectionsDocument17 pagesSQL InjectionsRajatRathee0% (1)
- Hacking Module 14Document24 pagesHacking Module 14Jitendra Kumar Dash100% (1)
- Week 9 Lecture 15 Information SecurityDocument35 pagesWeek 9 Lecture 15 Information SecurityZulkifl HasanNo ratings yet
- A Review On Web Security Mechanism Performance Evaluation Using Vulnerability and Attack InjectionDocument4 pagesA Review On Web Security Mechanism Performance Evaluation Using Vulnerability and Attack InjectionPrateekMandiNo ratings yet
- SQL Injection Monitoring Security Vulnerabilities in Web ApplicationsDocument6 pagesSQL Injection Monitoring Security Vulnerabilities in Web ApplicationsInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Smith 2010Document9 pagesSmith 2010Jessica UrquizoNo ratings yet
- The SQL Injection and Signature EvasionDocument11 pagesThe SQL Injection and Signature Evasionsynfin80No ratings yet
- Web Application AttacksDocument5 pagesWeb Application AttacksHet Bhavin PatelNo ratings yet
- Web Sanitization From Malicious Code Injection AttacksDocument11 pagesWeb Sanitization From Malicious Code Injection AttacksSanaNo ratings yet
- SQL Injection HShahDocument7 pagesSQL Injection HShahÉderNo ratings yet
- Secure Coding Practice ChecklistDocument12 pagesSecure Coding Practice ChecklistOussama El bazNo ratings yet
- Joomla! Security Presentation - Joomladagen 2010Document17 pagesJoomla! Security Presentation - Joomladagen 2010La Mi To RiNo ratings yet
- EC-Council: Exam Questions 312-50v10Document44 pagesEC-Council: Exam Questions 312-50v10A.S.M.RashelNo ratings yet
- ctf4 InstructionsDocument66 pagesctf4 InstructionsaresthelordNo ratings yet
- Acunetix v12: Is Your Website Hackable?Document32 pagesAcunetix v12: Is Your Website Hackable?Kim AlmeidaNo ratings yet
- D1T1 - Petko Petkov - History of The JavaScript Security ArsenalDocument53 pagesD1T1 - Petko Petkov - History of The JavaScript Security ArsenalErkanNo ratings yet
- Vuln Xss Pada Suati WebDocument9 pagesVuln Xss Pada Suati WebsandraNo ratings yet
- DAST Vulnerability Scan of Webgoat Joseph Wagner CSOL 560 Professor Moore University of San DiegoDocument17 pagesDAST Vulnerability Scan of Webgoat Joseph Wagner CSOL 560 Professor Moore University of San Diegoapi-600998672No ratings yet
- 10 HTML5 SecurityDocument32 pages10 HTML5 SecurityAdarsh SuparnaNo ratings yet
- Best 25+: Senior Java & Kotlin & Fullstack Developer Interview Questions and AnswersDocument34 pagesBest 25+: Senior Java & Kotlin & Fullstack Developer Interview Questions and AnswersfuckyouNo ratings yet
- Renuka&Navya Jyothi - Indian Banks Center For Analysis of RisksDocument68 pagesRenuka&Navya Jyothi - Indian Banks Center For Analysis of RisksSUNILRATHODNo ratings yet
- A Penetration TestDocument7 pagesA Penetration TestSALMANRIZNo ratings yet
- Flask PDFDocument293 pagesFlask PDFVarun KilaruNo ratings yet
- Planning de Estudio Con S4vitar (Preparación OSCP, OSED, OSWE, OSEP, EJPT, EWPT, EWPTXv2, ECPPTv2, ECPTXv2) - HackTheBoxDocument23 pagesPlanning de Estudio Con S4vitar (Preparación OSCP, OSED, OSWE, OSEP, EJPT, EWPT, EWPTXv2, ECPPTv2, ECPTXv2) - HackTheBoxExodial FleshNo ratings yet
- Api Example 1: Vulnerability Type: Api Request's Response Leakage. Screenshot of ComponentDocument49 pagesApi Example 1: Vulnerability Type: Api Request's Response Leakage. Screenshot of ComponentAshlee GregoryNo ratings yet
- File Upload, Code Execution, LFI, RFI, SQLi, XSSDocument26 pagesFile Upload, Code Execution, LFI, RFI, SQLi, XSSJulio BarreraNo ratings yet
- Fedora Security Team Secure Ruby Development GuideDocument52 pagesFedora Security Team Secure Ruby Development GuidelindaiiakoNo ratings yet
- Website Security 101: Real-World Examples, Tools & Techniques For Protecting & Securing WebsitesDocument12 pagesWebsite Security 101: Real-World Examples, Tools & Techniques For Protecting & Securing WebsitesKristijan Žic100% (1)
- Self Paced / Online Web Application Security Testing Certification CoursesDocument4 pagesSelf Paced / Online Web Application Security Testing Certification CoursesSharmila SubbarajuNo ratings yet
- Detecting SQL Injection Attacks Using SNORT IDS: November 2014Document8 pagesDetecting SQL Injection Attacks Using SNORT IDS: November 2014Fernando RománNo ratings yet
- Cross-Site Scripting (XSS) Cheat Sheet - 2020 EditionDocument90 pagesCross-Site Scripting (XSS) Cheat Sheet - 2020 Editionsaddest jokerNo ratings yet
- AEM Developer GuideDocument124 pagesAEM Developer Guideraja sekhar reddy Bhavanam100% (2)
- Top Web App Attack Methods and How To Combat Them: Dennis Hurst, SPI DynamicsDocument74 pagesTop Web App Attack Methods and How To Combat Them: Dennis Hurst, SPI DynamicsSridhar KrishnamurthiNo ratings yet
- Web Application Security: Chuka UniversityDocument30 pagesWeb Application Security: Chuka UniversityJM MaguigadNo ratings yet
- IndexDocument40 pagesIndexComanceanu100% (1)
- CCS374 Web Application SecurityDocument18 pagesCCS374 Web Application Securitydhanush02010No ratings yet
- WP Hacme Bank v2 User GuideDocument74 pagesWP Hacme Bank v2 User GuideCesar Fabian MlNo ratings yet
- SAP Cloud PlatformDocument2,328 pagesSAP Cloud PlatformAriel Martinez100% (2)
- Learning JqueryDocument88 pagesLearning JqueryHamza MansoorNo ratings yet
- SDocument9 pagesSGabriel CostescuNo ratings yet
- State of Cybersecurity 2020: Part 2: Threat Landscape and Security PracticesDocument23 pagesState of Cybersecurity 2020: Part 2: Threat Landscape and Security PracticesRey2000No ratings yet
- Security Testing of Web Applications Issues and Challenges 2014Document8 pagesSecurity Testing of Web Applications Issues and Challenges 2014Carlos Arturo Vega LebrúnNo ratings yet